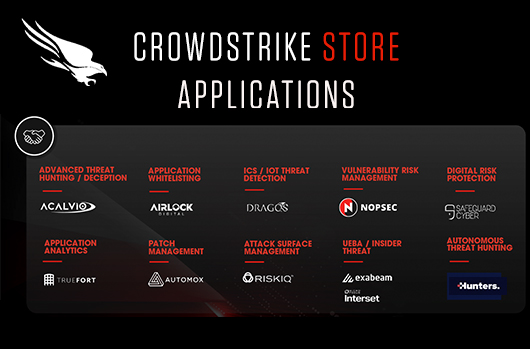
CrowdStrike Strengthens Its Cybersecurity Alliances Ecosystem in the Battle Against Advanced Threats
This year at RSA 2020, I was excited to announce the launch of several new offerings for our growing global…
Beware: Third Parties Can Undermine Your Security
Do you automatically trust your external vendors? You might want to make them earn your trust. Adversaries are constantly seeking…
The CrowdStrike 2020 Global Threat Report Reveals Troubling Advances in Cybercrime
Those of us who have worked in cybersecurity for many years often start to think we’ve “seen it all.” We…
At RSA 2020, CrowdStrike Wins SC Media Excellence Award for Best Security Company
RSA 2020 has proven to be another breakthrough event for CrowdStrike®, including highlights such as winning the SC Media 2020…
CrowdStrike Unveils Exciting New Capabilities at RSA 2020
It’s that time of the year, and the RSA 2020 conference is proving to be as ambitious and jam-packed as…
CrowdStrike’s Matt LeMiere on Why Schools Are Failing Cybersecurity
Cybercriminals have long considered schools a soft target and a recent article on GovCybersecurityHub explores the reasons why and what…
Convolutional Neural Networks Are MALE Models for PE Malware
Machine learning for computer security has enjoyed a number of recent successes, but these tools aren’t perfect, and sometimes a…
How to Sniff Out (and Block) BloodHound Attacks
The growing adversary focus on “big game hunting” (BGH) in ransomware attacks — targeting organizations and data that offer a higher…
Building a String-Based Machine Learning Model to Detect Malicious Activity
Working with text data (which we often refer to as “strings”) is common in cybersecurity applications. For example, suppose we…
Gimme Shellter
Red team penetration testers very often add tools to their arsenal that borrow techniques originating in malicious software. Shellter is…