The Critical Role of Cybersecurity in M&A: Part 3, Post-Close
In the post-close phase of an M&A transaction, the deal may be done but the job of integration has just…
Blind Spots in the Cloud
Visibility in the cloud is an important but difficult problem to tackle. It differs among cloud providers, and each one…
Scott Hasson, Security Services Specialist on Protecting the Digital World
As a former member of the British Armed Forces, protecting people is what Scott Hasson has always done. Lucky for…
How CrowdStrike Provides Visibility for Cloud Security
Introduction With the rapid adoption of cloud deployments, many organizations are struggling to implement consistent security standards. This document and…
Learning How to Problem-Solve at Scale and Embrace a World of Continuous Change with Morgan Maxwell, Senior Engineer
At CrowdStrike, we sometimes like to say, “There’s data, big data and CrowdStrike data,” by which we mean our engineers…
A Behind-the-Scenes Look at the Life of a CrowdStrike Engineer with Sorabh Lall, Senior Engineer
Cybersecurity is all about anomalies — and perhaps no one can prove that point better than Sorabh Lall. As a…
The Critical Role of Cybersecurity in M&A: Part 2, Pre-Close
This is Part 2 of our three-part blog series on the critical importance of cybersecurity in the M&A process. Part…
Offering Our People Autonomy, Mastery and Purpose: Patrick McCormack, SVP Cloud Engineering
When deciding to take a new job, one of the biggest concerns is often who you’ll be working for —…
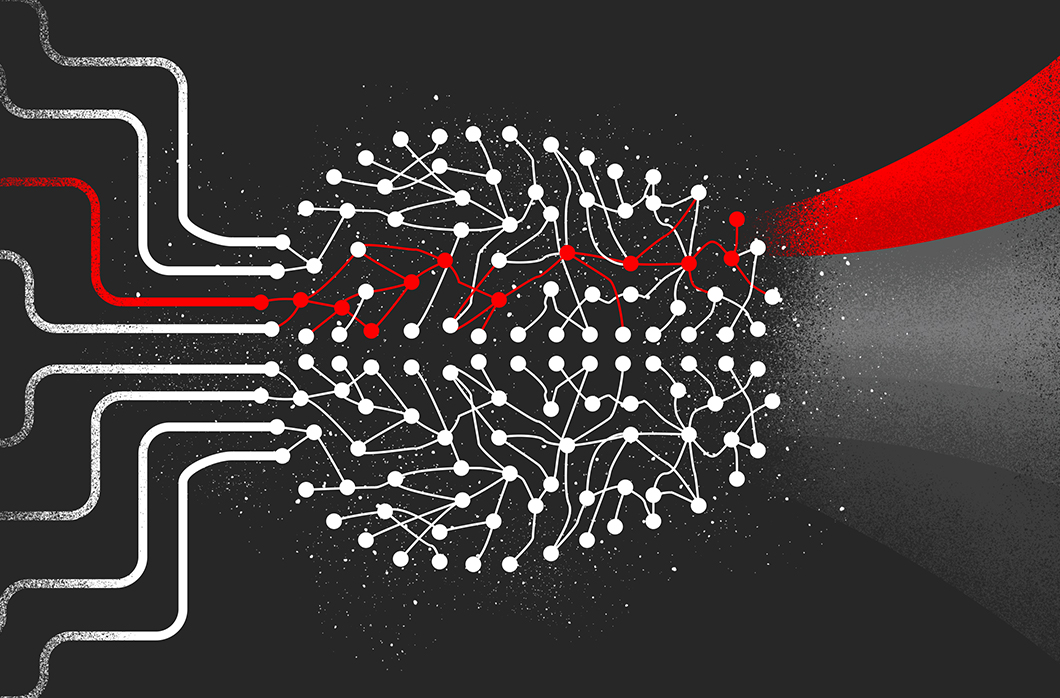
Seeing Malware Through the Eyes of a Convolutional Neural Network
Motivation Deep learning models have been considered “black boxes” in the past, due to the lack of interpretability they were…