Software Supply Chain Attacks Gained Traction in 2017 and Are Likely to Continue
One of the important topics covered in the CrowdStrike® 2018 Global Threat Report is the increase in supply chain attacks…
The Hole in the Donut: Franchise Relationships Create Unique Cybersecurity Risks
In February 2018, the nation of Canada experienced an attack on a popular franchise chain that didn’t make the front…
Meet CrowdStrike’s Adversary of the Month for March: VENOMOUS BEAR
VENOMOUS BEAR is an advanced, Russia-based adversary that’s been active since at least 2004. Some of it's aliases include Turla, Snake, and…
5 Key Cyberthreat Trends From CrowdStrike’s 2018 Global Threat Report
Update: CrowdStrike's 2020 Global Threat Report is now available! Download the report to stay ahead of today's adversaries. This week,…
CrowdStrike’s 2018 Global Threat Report Reveals the Trends, Insights and Threat Actors You Need to Know
It's been another banner year for bad actors. Not only did the volume and intensity of cyberattacks hit new highs,…
CrowdStrike Falcon Officially “In-Process” for FedRAMP Authorization
CrowdStrike® is proud to announce that it is officially “In Process” for the Federal Risk and Authorization Management Program (FedRAMP)…
CrowdStrike CTO: The Third Phase of Cyber Conflict and How to Address It
In a recent article on LinkedIn titled, “Addressing The Third Generation of Cyber Conflict,” CrowdStrike CTO and Co-founder Dmitri Alperovitch…
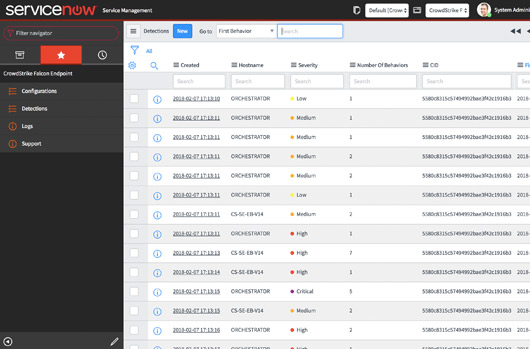
CrowdStrike Falcon Offers Plug-and-Play Integration with ServiceNow
Since the inception of the CrowdStrike Falcon® platform, an API-first approach has always been a key strategy for providing customers…
Meet CrowdStrike’s Adversary of the Month for February: MUMMY SPIDER
In continuance of our monthly blog post to introduce a new threat actor, February 2018 features a criminally motivated actor…