CrowdStrike for Security Operations
Introduction
This document and video will demonstrate how the CrowdStrike solution empowers the Security Operations Center to detect and understand events quickly so that they can get proactive and take action to protect the organization.
Video
Threat Hunting
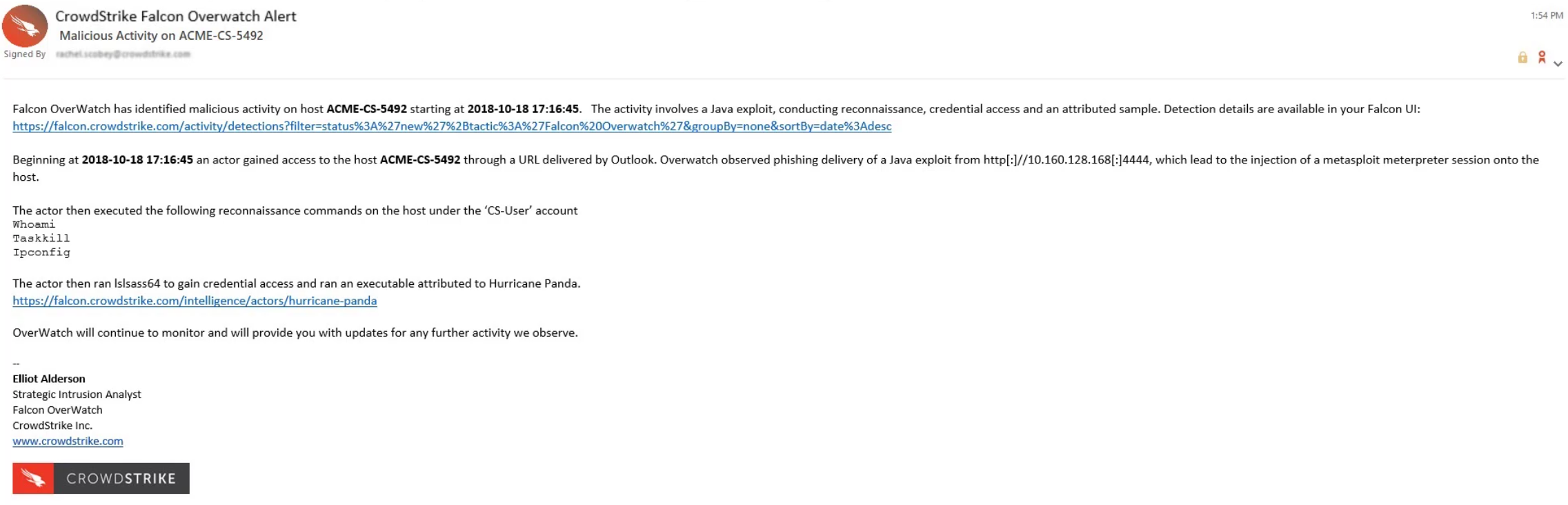
CrowdStrike’s EDR solution provides unparalleled visibility into local system events. While existing engines detect a great deal of malicious behavior, the adversary is always looking for new ways to gain access. Falcon OverWatch is there 24×7 to provide human insight and analyze events in search of potentially malicious activity that was not previously detected. The email below is an example of an OverWatch alert of potentially malicious activity.
Event Visibility
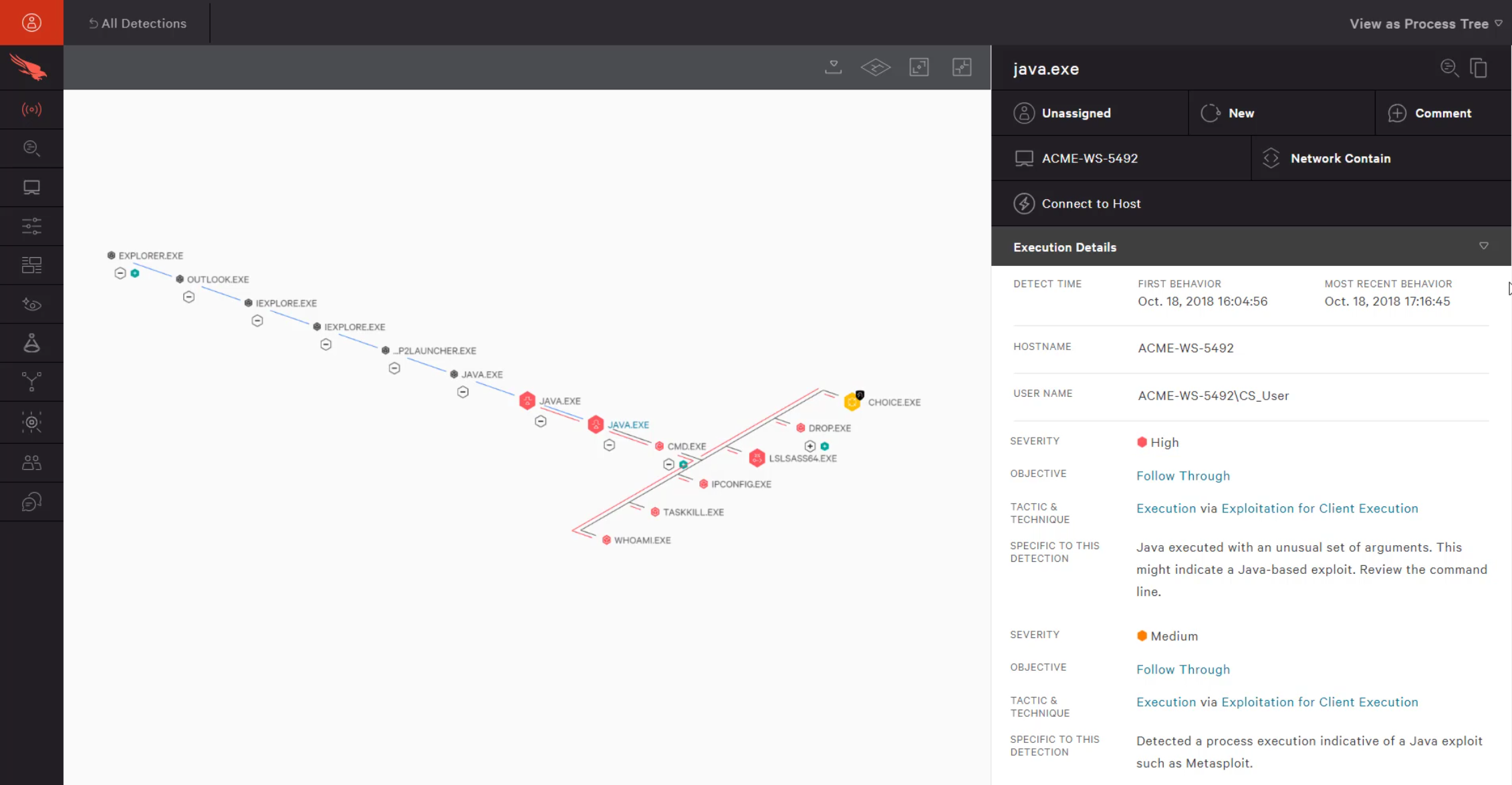
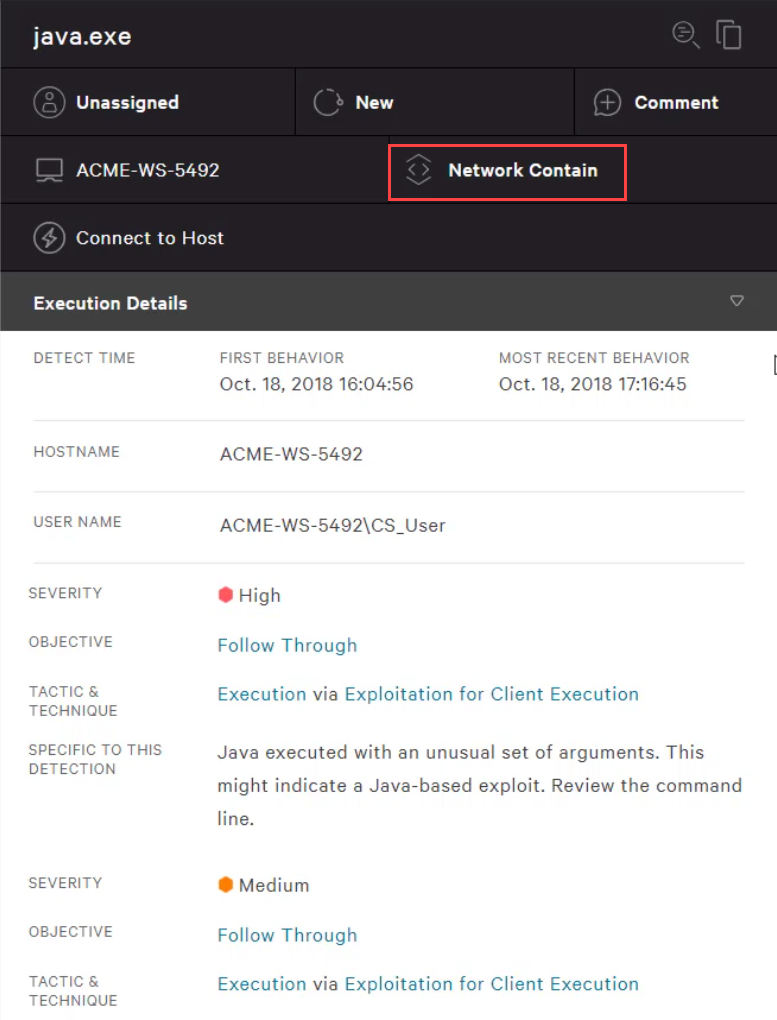
The link in the email takes us directly to the event details. There, we see the detailed visibility that Falcon Insight offers. In addition to the process tree, we see the MITRE tactic & technique as well as the objective and severity.
Falcon Insight also provides response actions including remote remediation and network containment. Network Containment helps to prevent lateral movement or external communications during your investigation.
Incident Research
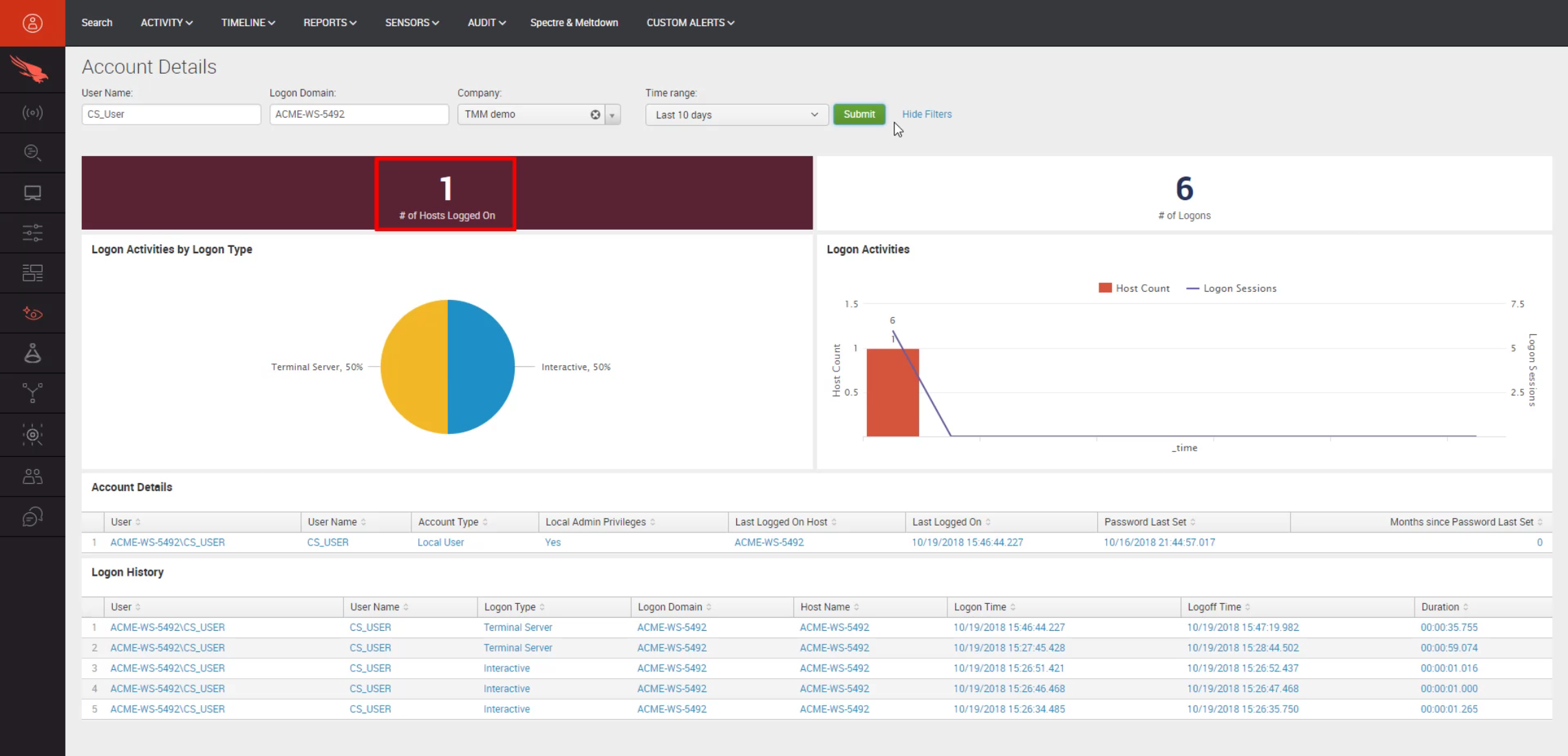
Once the incident has been identified and contained, we need to understand more about what has taken place. Using Falcon Discover, we can quickly understand if the user’s account might have been compromised. We can search on the username in question to track all login activity across all protected systems.
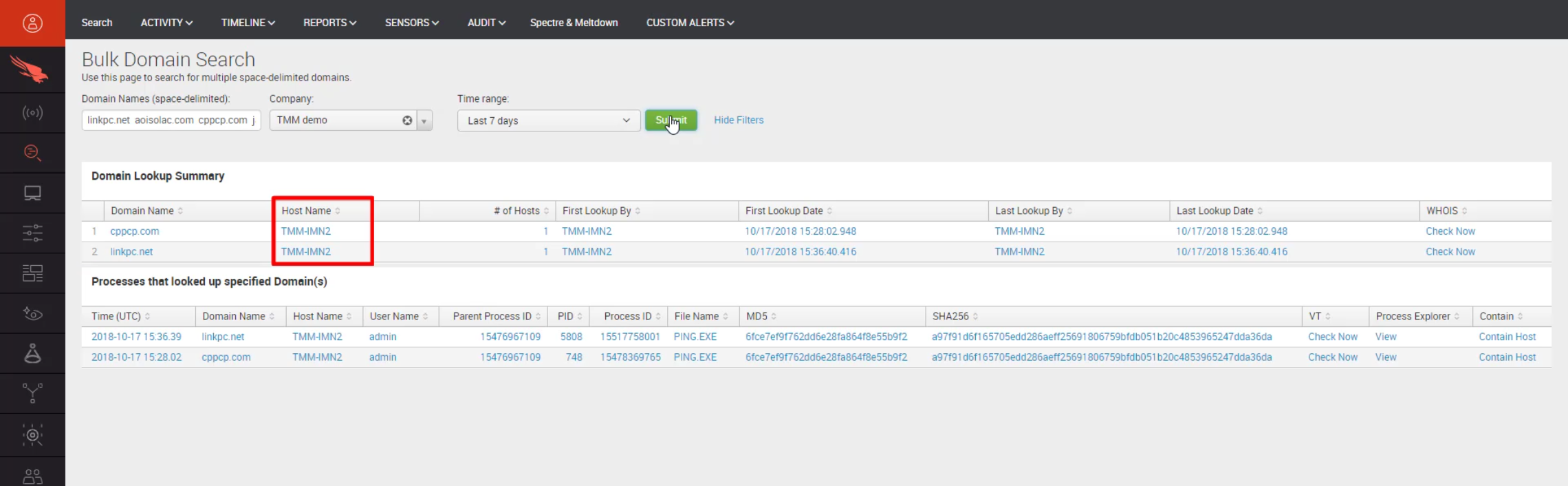
Similarly, Falcon Insight can help us understand if there has been network access to related domains or IP’s from other machines. This is especially useful to understand if this is part of a persistent or long term attack where other machines might have been previously impacted.
Intelligence Context
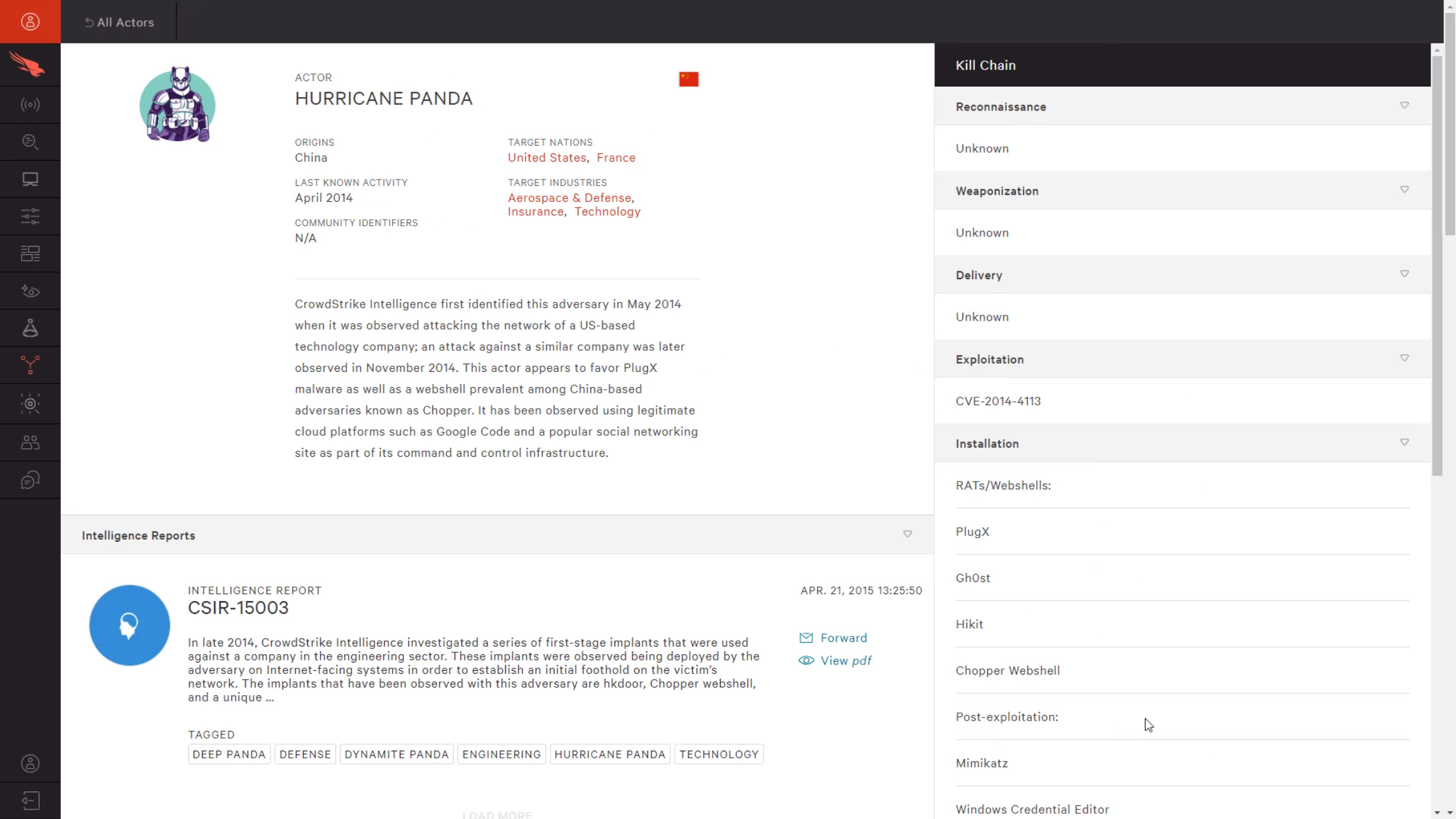
For activity that is attributed to a specific adversary, Falcon Intel’s actor profiles provide helpful information based on known behaviors of the actor. Things like commonly targeted industries, Command and Control domains, and frequently leverages vulnerabilities can help you get proactive and take steps to protect your environment from future attacks.
Vulnerability Assessment
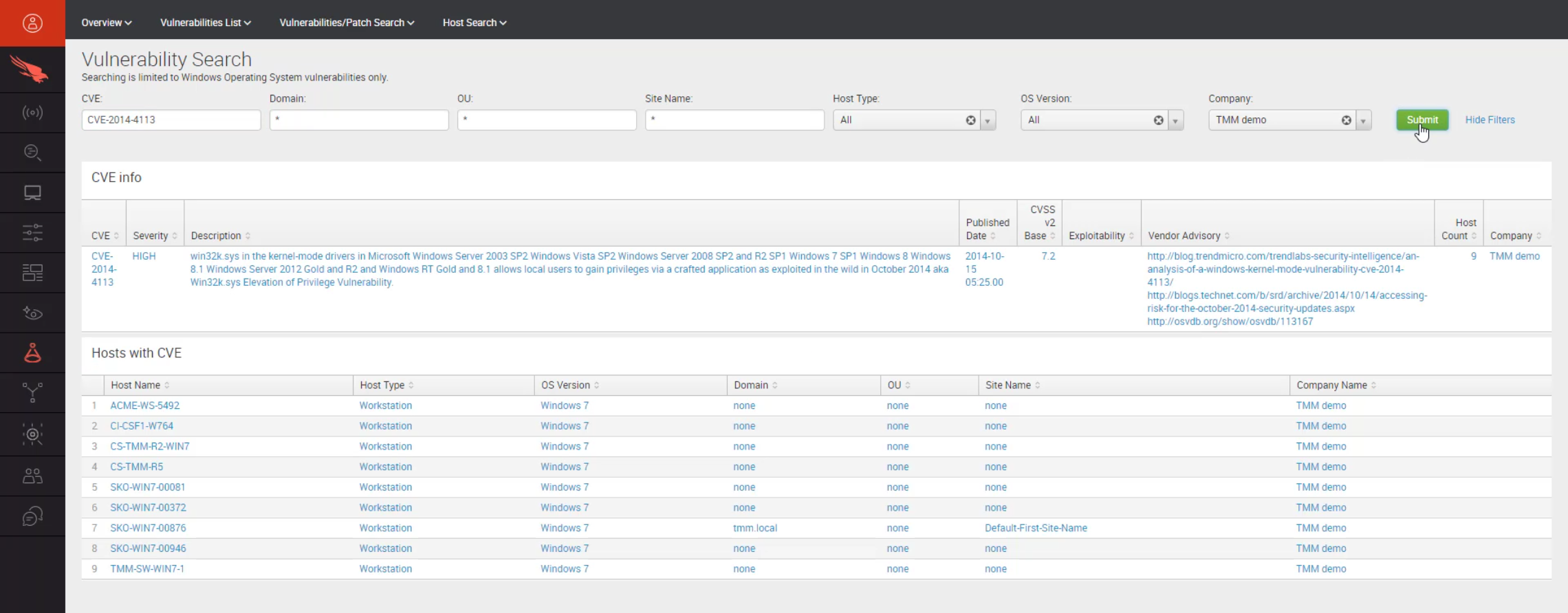
Falcon Spotlight gives you the ability to quickly assess the environmental status on specific vulnerabilities. Having this real time information is invaluable when you are responding to a threat or taking proactive action against known attackers. Sharing it with the patch management team can help them prioritize patch remediation plans.
Conclusion
CrowdStrike’s proactive threat hunting, EDR, cyber threat intelligence, IT hygiene, and vulnerability assessment tools work together to improve incident response and remediation times. Through fast detection, clear understanding and actionable measures, the Security Operations Team will be more effective and empowered to improve the company’s overall security posture.
More resources