What is a MITM Attack?
A man-in-the-middle attack is a type of cyberattack in which an attacker eavesdrops on a conversation between two targets. The attacker may try to “listen” to a conversation between two people, two systems, or a person and a system.
The goal of a MITM attack is to collect personal data, passwords or banking details, and/or to convince the victim to take an action such as changing login credentials, completing a transaction or initiating a transfer of funds.

2024 CrowdStrike Global Threat Report
The 2024 Global Threat Report unveils an alarming rise in covert activity and a cyber threat landscape dominated by stealth. Data theft, cloud breaches, and malware-free attacks are on the rise. Read about how adversaries continue to adapt despite advancements in detection technology.
Download NowWhile MITM attackers often target individuals, it is a significant concern for businesses and large organizations as well. One common point of access for hackers is through software-as-a- service (SaaS) applications, such as messaging services, file storage systems or remote work applications. Attackers can use these applications as an entryway to the organization’s wider network and potentially compromise any number of assets, including customer data, intellectual property (IP) or proprietary information about the organization and its employees.
How a Man-in-the-Middle Attack Works?
A MITM attack generally consists of two phases: interception and decryption.
Phase #1: Interception
In the interception phase, cybercriminals gain access to a network through an open or poorly secured Wi-Fi router and/or by manipulating domain name system (DNS) servers. Attackers then scan the router looking for vulnerabilities and possible points of entry. Most often this is done through a weak password, though cybercriminals may also use more advanced methods such as IP spoofing or cache poisoning.
Once a target is identified, the attacker typically deploys data capture tools to access and collect the victim’s transmitted data, strategically redirect traffic or otherwise manipulate the user’s web experience.
Phase #2.Decryption
The second phase of an MITM attack is decryption. This is when stolen data is decoded and made intelligible to the cybercriminals. Decrypted data can be leveraged for any number of nefarious purposes, including identity theft, unauthorized purchases or fraudulent bank activity. In some cases, man-in-the-middle attacks are conducted for no obvious purpose other than to disrupt business operations and create chaos for victims.
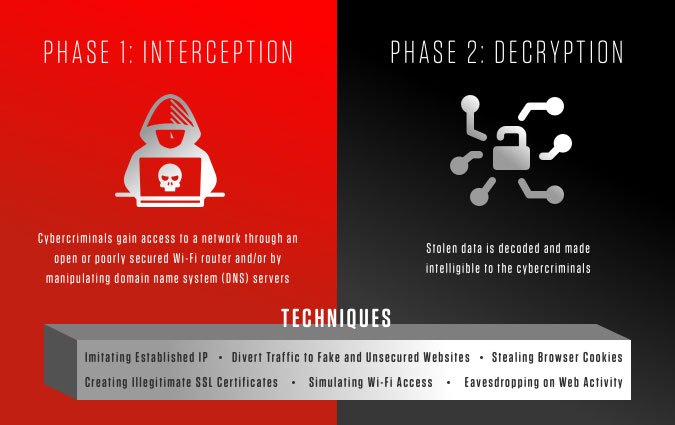
MITM Techniques
Cybercriminals use a wide variety of methods to carry out MITM attacks. Some common techniques include:
- Imitating an established internet protocol (IP) to trick users into providing personal information or spur a desired action, such as initiating a bank transfer or password change
- Redirecting a user from a known destination to a fake website to divert traffic and/or gather login credentials and other personal information
- Simulating a Wi-Fi access point to intercept any web activity and gather personal information
- Creating illegitimate secure sockets layer (SSL) certificates, which give the appearance of a secure connection to users even though the connection has been compromised
- Redirecting traffic to an unsecured website, which then gathers login credentials and personal information
- Eavesdropping on web activity, including email, to gather personal information and inform further fraudulent activity, such as phishing attempts
- Stealing browser cookies, which contain personal information
Man-in-the-Middle Attack Example
One recent mitm attacker identified by CrowdStrike was a Trickbot module called shaDll. The module installed illegitimate SSL certificates on infected computers, which allowed the tool to gain access to the user network. The module was then able to redirect web activity, inject code, take screenshots and gather data.
What was particularly interesting about this attack was that it was an apparent collaboration between two known cybercrime groups: LUNAR SPIDER and WIZARD SPIDER. The module used LUNAR SPIDER’s BokBot proxy module as a foundation and then deployed WIZARD SPIDER’s TrickBot module to complete the attack. The likely collaboration between these two adversaries highlights the growing sophistication of MITM attacks and the need for a heightened awareness.
Man-in-the-middle Attack Prevention
The following recommendations can help protect your networks against MITM attacks:
- Require network users to select strong passwords and change them on a regular basis
- Enable multi-factor authentication (MFA) on all network assets and applications
- Develop and deploy strong encryption protocols
- Equip all network assets with virtual private network (VPN) capabilities
- Deploy a comprehensive threat monitoring and detection solution
- Segment the network to ensure potential breaches are contained
- Educate employees on the risks of public Wi-Fi networks
While it may not be practical for individuals to install detection capabilities for man-in-the-middle attacks, following general cyber safety techniques can help prevent intrusion. We recommend the following best practices for individual users:
- Install malware detection security software
- Create strong passwords and change them on a regular basis
- Enable multi-factor authentication capabilities
- Avoid the use of open Wi-Fi networks and/or poorly secured public networks
- Always ensure you are browsing secure websites, as indicated by the https:// in the URL


