The rise of distributed cloud services and the omnipresence of APIs has caused cloud-native application architecture to become highly fragmented. Enforcing secure access is a critical step in strengthening security as IT environments become more complex — but for many organizations, ensuring secure access across this evolving architecture is a constant challenge.
Existing secure access solutions often fail to scale within customer environments as they largely focus on managing secrets, which becomes more time-consuming and error-prone in modern environments. Employing these legacy solutions can hinder an organization’s ability to scale and secure their cloud-native applications.
Securing access to company assets is a modern security requirement and must span human and non-human identities. Like users, workloads have distinct identities and evolving security postures. Machine identities are growing exponentially, with workload identities outnumbering human identities 10:1 — a staggering ratio that doubled from 2021 to 2023. The challenges of securing these resources, and the significant losses organizations face, have created a need for a revolutionary approach to securing workload access.
Falcon Fund partner Aembit, a workload identity and access management (IAM) platform provider, has announced a new integration with the AI-native CrowdStrike Falcon platform to empower businesses to manage and enforce conditional access policies based on the real-time security posture of their applications and services. Aembit’s dynamic platform seamlessly identifies and authenticates workloads, authorizes access based on policies including security posture, and logs all accesses and access attempts for auditing and analytics. Aembit Workload IAM is designed to work across clouds, on-premises environments, SaaS services and third-party APIs.
The platform drives productivity by allowing developers to take a no-code approach to authentication. It provides centralized control and visibility, and replaces outdated secrets manager solutions, shifting the paradigm to managing access — not secrets. The partnership between CrowdStrike and Aembit demonstrates a significant step forward in Aembit’s mission to help organizations make workload-to-workload access more secure and manageable.
CrowdStrike is excited to build on its strategic investment in Aembit through CrowdStrike Falcon Fund. A key piece of this investment is a multi-faceted partnership between CrowdStrike and Aembit to ensure conditional access policies for secure workload access. Through the initial integration, customers can enforce Zero Trust for workloads with thorough and accurate assessments of workload security posture, policies that grant access based on workload identities, and conditional access dependent on workload health.
How the Integration Works
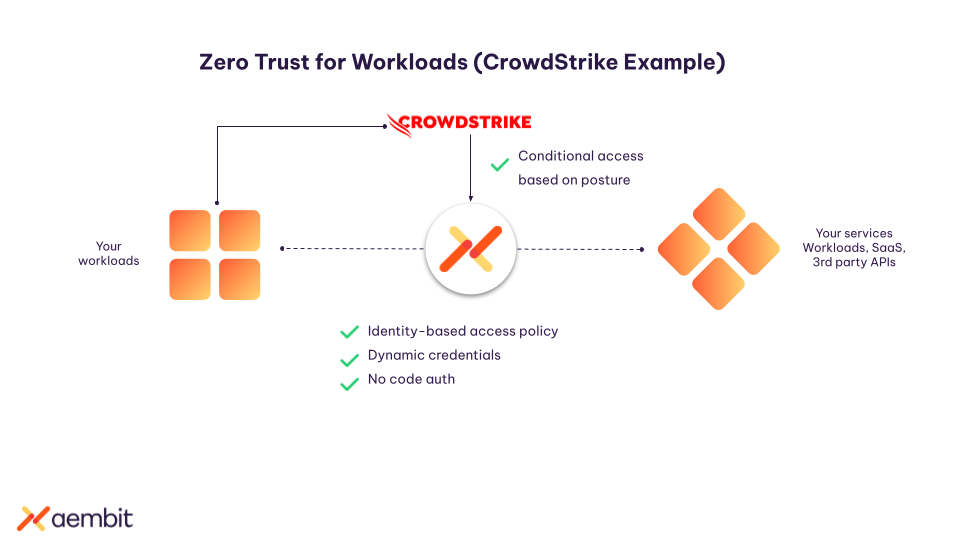 The Aembit Workload IAM solution checks to see if a CrowdStrike Falcon agent is running on the workload. It leverages CrowdStrike’s workload posture assessment, along with workload identity attestation, to evaluate the workload’s real-time security posture and determine whether workloads should be granted access to applications and data. This process ensures that access originates from a trusted workload.
The Aembit Workload IAM solution checks to see if a CrowdStrike Falcon agent is running on the workload. It leverages CrowdStrike’s workload posture assessment, along with workload identity attestation, to evaluate the workload’s real-time security posture and determine whether workloads should be granted access to applications and data. This process ensures that access originates from a trusted workload.
With this approach, enterprises can protect their workloads from unauthorized access, even against the backdrop of changing conditions and dynamic access requirements. Additional benefits from this partnership include:
- Managed workload-to-workload access: Enforce and manage workload access to other applications, SaaS services and third-party APIs based on policies set by the security team, lowering risk.
- Ease of deployment: Seamlessly integrate the Aembit Workload IAM platform with the Falcon platform in just a few clicks, creating a unified experience for managing workload identities while understanding workload security posture.
- Zero Trust security model: Adopt a Zero Trust approach, which ensures every access request is verified before access rights are granted. Aembit’s solution enforces the principle of least privilege based on identity, policy and workload security posture.
- Visibility and monitoring: Gain in-depth visibility into workload identities and access permissions to drive faster threat detection and response. Monitor and audit access logs based on identity for comprehensive security oversight.
Please visit the Aembit integration page in the CrowdStrike Marketplace to learn more and request the integration today.
Additional Resources
- Learn more about Falcon Fund and CrowdStrike’s partnership with innovative companies.
- See how CrowdStrike gives you comprehensive protection across your organization through our 15-day free trial.
- Visit the CrowdStrike Marketplace to explore additional partner integrations.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)







































