Callback Malware Campaigns Impersonate CrowdStrike and Other Cybersecurity Companies

Today CrowdStrike sent the following Tech Alert to our customers:
On July 8, 2022, CrowdStrike Intelligence identified a callback phishing campaign impersonating prominent cybersecurity companies, including CrowdStrike. The phishing email implies the recipient’s company has been breached and insists the victim call the included phone number. This campaign leverages similar social-engineering tactics to those employed in recent callback campaigns including WIZARD SPIDER’s 2021 BazarCall campaign.
This campaign will highly likely include common legitimate remote administration tools (RATs) for initial access, off-the-shelf penetration testing tools for lateral movement, and the deployment of ransomware or data extortion.
Details
The callback campaign employs emails that appear to originate from prominent security companies; the message claims the security company identified a potential compromise in the recipient’s network. As with prior callback campaigns, the operators provide a phone number for the recipient to call (Figure 1).
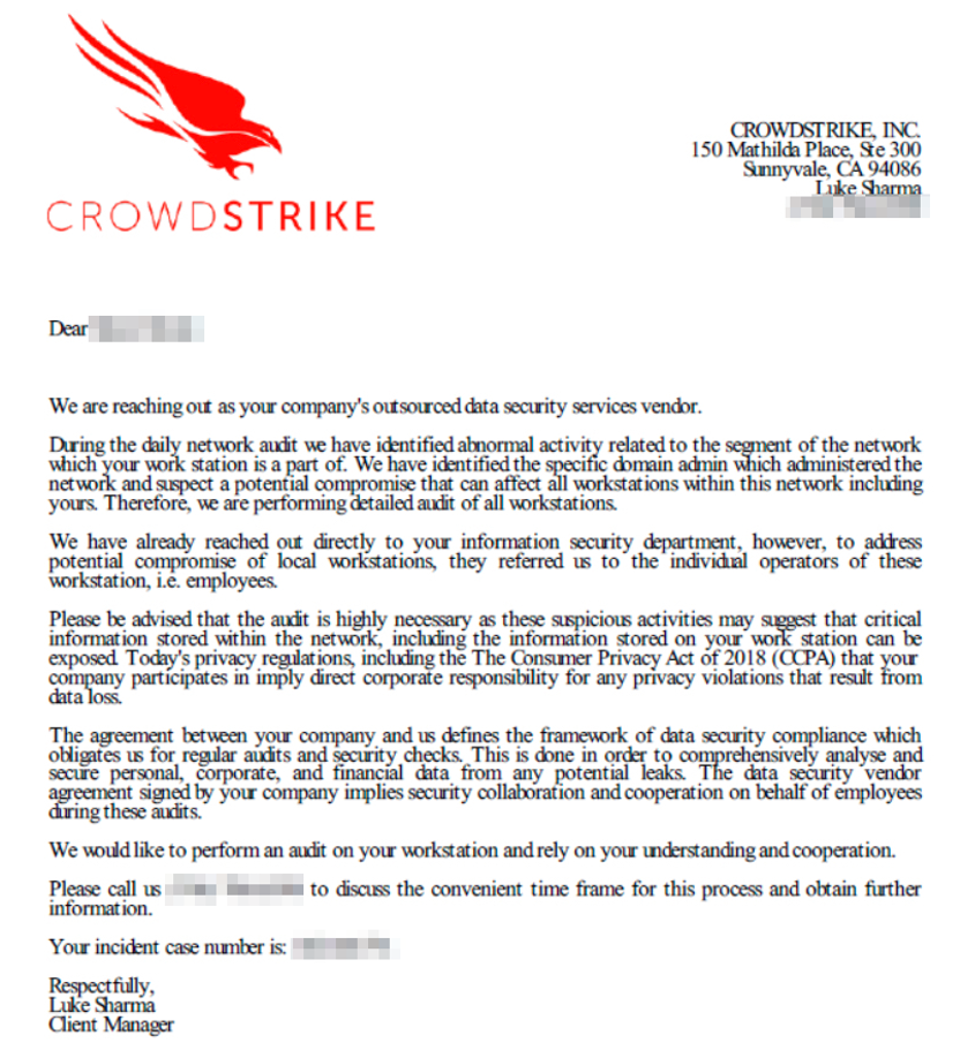
Figure 1. Example of CrowdStrike-Themed Phishing Email
Historically, callback campaign operators attempt to persuade victims to install commercial RAT software to gain an initial foothold on the network. For example, CrowdStrike Intelligence identified a similar callback campaign in March 2022 in which threat actors installed AteraRMM followed by Cobalt Strike to assist with lateral movement and deploy additional malware.
Assessment
While CrowdStrike Intelligence cannot currently confirm the variant in use, the callback operators will likely use ransomware to monetize their operation. This assessment is made with moderate confidence, as 2021 BazarCall campaigns would eventually lead to Conti ransomware — though this ransomware-as-a-service (RaaS) recently ceased operations. This is the first identified callback campaign impersonating cybersecurity entities and has higher potential success given the urgent nature of cyber breaches.
CrowdStrike will never contact customers in this manner.
Any customers receiving an email such as those in this Alert should forward phishing emails to csirt@crowdstrike.com.
Additional Resources
- Get more threat intel insights at Fal.Con 2022, the cybersecurity industry’s most anticipated annual event. Register now and meet us in Las Vegas, Sept. 19-21!
- What is Phishing?
- CrowdStrike customers can view this page for the latest recommendations and updates.
- Additional resources may be collected under Trending Threats & Vulnerabilities: Callback Malware Campaign (CSA-220707).
- Find answers and contact Support with our Support Portal.