The Cybersecurity and Infrastructure Security Agency (CISA) issued a mandate on November 2, 2021, for all U.S. federal agencies to fix hundreds of known vulnerabilities. Binding Operational Directive 22-01 (BOD 22-01) compels all federal departments and agencies to specifically address the vulnerabilities in the published catalog to protect and safeguard valuable federal data and information systems. The order will require all agencies to have patches in place for all vulnerabilities published prior to 2021 within six months, and all vulnerabilities from 2021 and beyond within two weeks of the issuance date.How Does Falcon Spotlight’s ExPRT.AI Work?
Falcon Spotlight’s ExPRT.AI is based on two important factors: the data that the algorithm model relies on and the structure and dynamism of the model itself. Let’s explore how this works.
The ExPRT.AI model is constantly adapting. It takes data from an impressive database of threat and exploit intelligence from a large variety of sources, and then uses both historical and new data (such as the CISA catalog) to create an output, the ExPRT Rating, which provides a more accurate and transparent rating than what SecOps staff have traditionally been forced to rely on. Since the model is always adapting, it provides a dynamic ExPRT rating — one that changes as new data comes in. When new threats or exploits are discovered, the rating for the vulnerability changes to reflect whether it should be ranked more or less severely based on the inputs.
The U.S. Department of Homeland Security and CISA will oversee the implementation of this mandate. As stated in the directive, “It is essential to aggressively remediate known exploited vulnerabilities to protect federal information systems and reduce cyber incidents.” The catalog of vulnerabilities contains many of the most highly exploited and most significant severity vulnerabilities that are known, making this list an important and essential tool for review and remediation within any organization covered in the directive.
While this directive is required only for federal agencies, CISA strongly recommends that all state and local government as well as private organizations review and monitor the provided vulnerability catalog and implement remediation procedures in the time frame specified in the directive to strengthen their overall security posture.
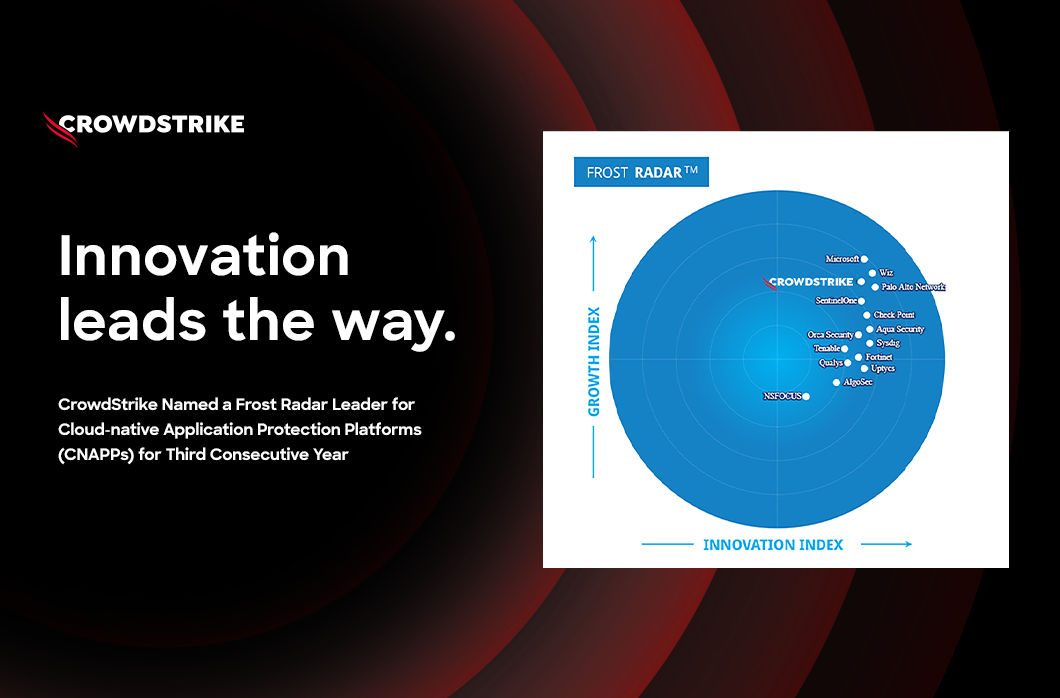
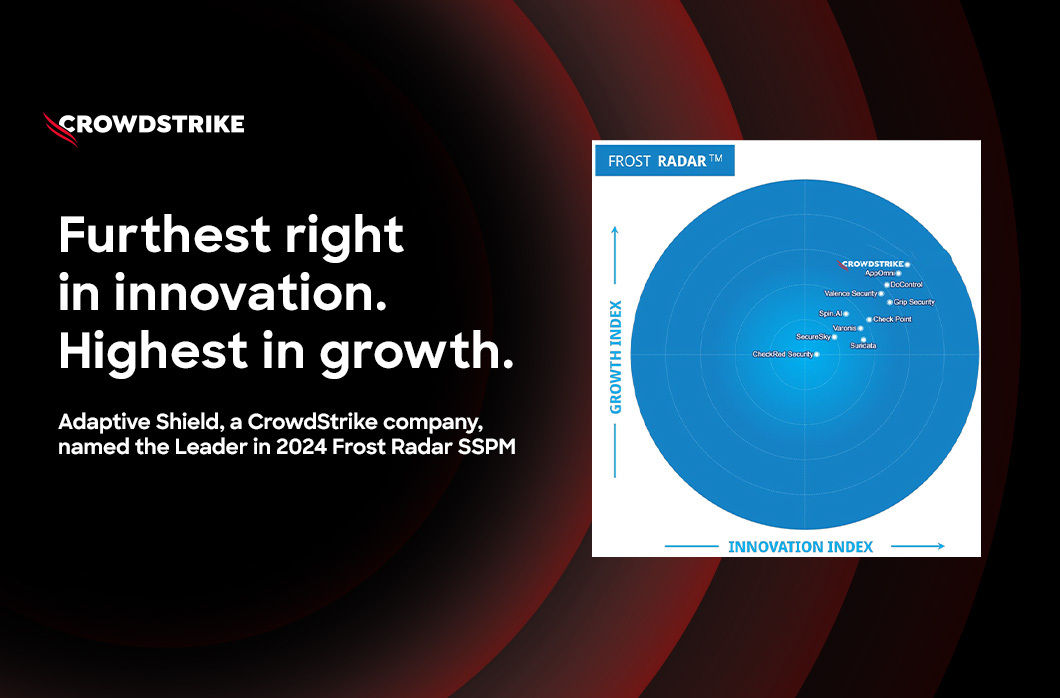
As a result of this mandate, CrowdStrike has added this catalog of vulnerabilities to Falcon Spotlight™ ExPRT.AI as a new source of exploited vulnerability data. With Falcon Spotlight, government agencies and enterprises alike are able to quickly identify and prioritize vulnerabilities that pose the most risk for their organization.
Why Issue BOD 22-01?
This is the first time CISA has issued a government-wide mandate for federal agencies to remediate vulnerabilities. CISA Director Jen Easterly stated that CISA is using its authority to help enforce and encourage federal cybersecurity efforts to protect from potential malicious actors. She goes on to say, “The Directive lays out clear requirements for federal civilian agencies to take immediate action to improve their vulnerability management practices and dramatically reduce their exposure to cyber-attacks." Because this catalog contains already known exploited vulnerabilities and due to the sensitive or valuable nature of government systems and data, this mandate is timely to help ensure the protection and defense of the U.S. infrastructure.
Falcon Spotlight’s ExPRT.AI Helps Enable IT Staff to Meet CISA Requirements
SecOps staff for both government agencies and organizations are often pressed for time. With the plethora of critical and highly scored vulnerabilities, a common issue arises where not all highly scored vulnerabilities are addressed in a timely manner. This leaves organizations with gaps or flaws within their systems — and threat actors use those holes to exploit organizations for nefarious gain. Historically, SecOps has relied on vendors to provide some prioritization information around this large body of vulnerabilities — but that is not enough. With the limited amount of time typically allocated for patching and updating systems, critical vulnerabilities are not being remediated, and that could be potentially very damaging. Falcon Spotlight goes beyond identification of these vulnerabilities and prioritizes themin a new and extremely useful way. This method utilizes the recently announced ExPRT.AI — a dynamic model that capitalizes on a wide variety of vulnerability and threat-based telemetry, including CrowdStrike’s threat intelligence — as well as CISA’s Known Exploited Vulnerabilities Catalog to provide a more intuitive, relevant score or rating that enables staff to target those vulnerabilities that would have the most detrimental impact within an organization.
How Does Falcon Spotlight’s ExPRT.AI Work?
Falcon Spotlight’s ExPRT.AI is based on two important factors: the data that the algorithm model relies on and the structure and dynamism of the model itself. Let’s explore how this works.
The ExPRT.AI model is constantly adapting. It takes data from an impressive database of threat and exploit intelligence from a large variety of sources, and then uses both historical and new data (such as the CISA catalog) to create an output, the ExPRT Rating, which provides a more accurate and transparent rating than what SecOps staff have traditionally been forced to rely on. Since the model is always adapting, it provides a dynamic ExPRT rating — one that changes as new data comes in. When new threats or exploits are discovered, the rating for the vulnerability changes to reflect whether it should be ranked more or less severely based on the inputs.While other vendors may claim to have a dynamic rating system, only CrowdStrike’s vast library of telemetry can provide such an operationally useful solution as ExPRT.AI, giving SecOps staff greater efficiency and a higher degree of visibility to immediately remediate or patch the vulnerabilities that adversaries are most likely to target, specific to their organization.
To see how Falcon Spotlight ExPRT.AI works in action, check out this demo.
Additional Resources
- Try Falcon Spotlight™ to help discover and manage vulnerabilities in your environments.
- See how CrowdStrike Falcon Complete™ managed detection and response (MDR) stops Microsoft exchange server zero-day exploits.
- Make prioritization painless and efficient. Watch how Falcon Spotlight enables IT staff to improve visibility with custom filters and team dashboards.
- Read about critical vulnerabilities your organization should prioritize in our monthly Patch Tuesday blog series — read November’s installment.
- Test CrowdStrike next-gen AV for yourself. Start your free trial of Falcon Prevent™ today.




![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1)
![Endpoint Protection and Threat Intelligence: The Way Forward [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/GK-Blog_Images-1)