Endpoint Security – Remediate Threats with Real Time Response

Introduction
As adversaries breakout times reach an all time low of 79 minutes, security teams need to move faster to contain attacks before any damage is done.
CrowdStrike Real Time Response offers a powerful set of incident response options capable of mitigating a wide range of malicious activities launched by threat actors.
Accessible directly from the CrowdStrike Falcon console, it provides an easy way to execute commands on Windows, macOS, and Linux hosts and effectively addresses any issues with an extensive array of commands.
Let’s explore the power and ease of use of Real time response.
Walkthrough
CrowdStrike Falcon platform uses AI powered machine learning to detect that an adversary has begun infiltrating the environment.
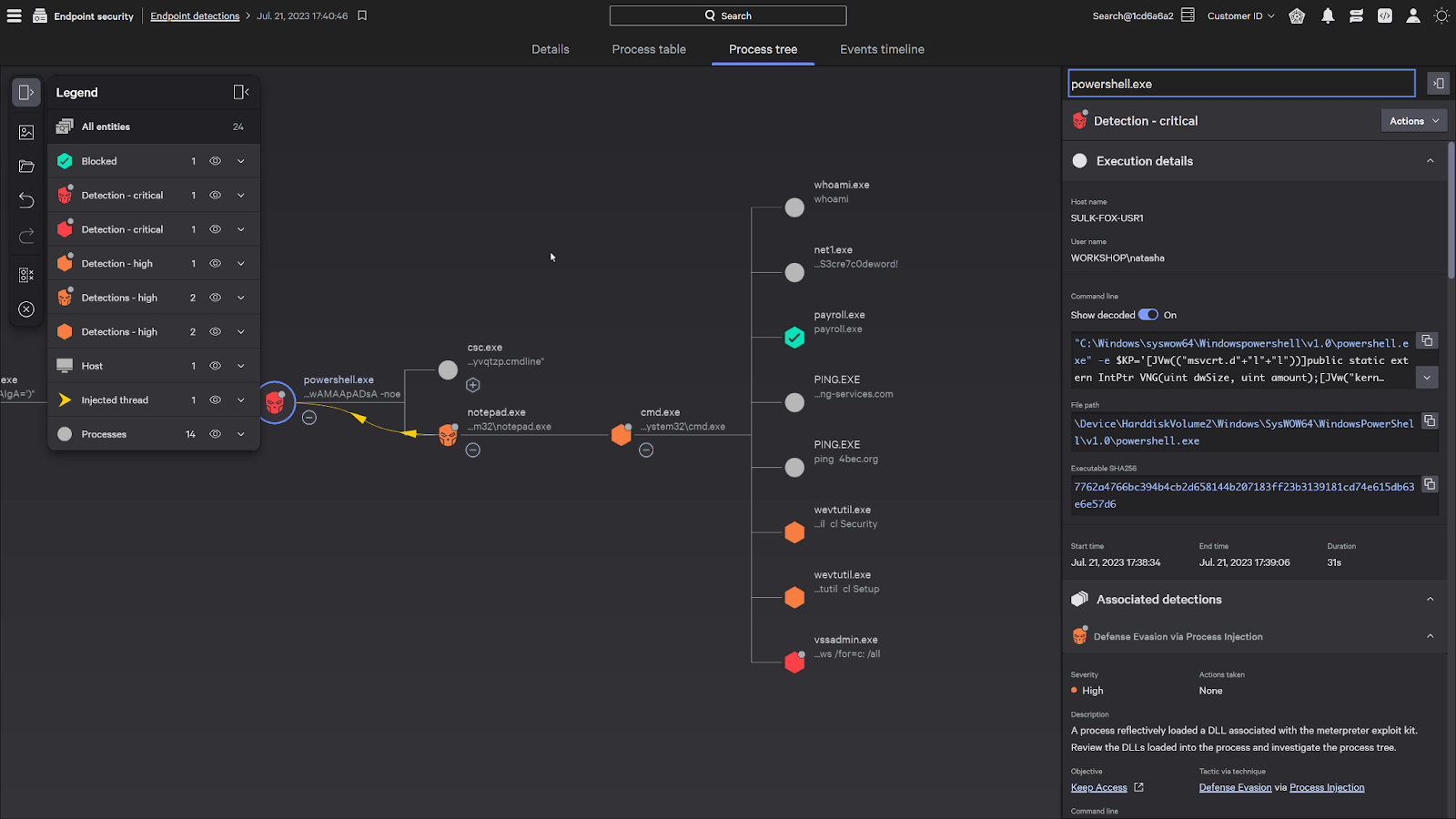
You can immediately initiate the remediation process by connecting to the impacted system with Real Time Response to contain the attack.
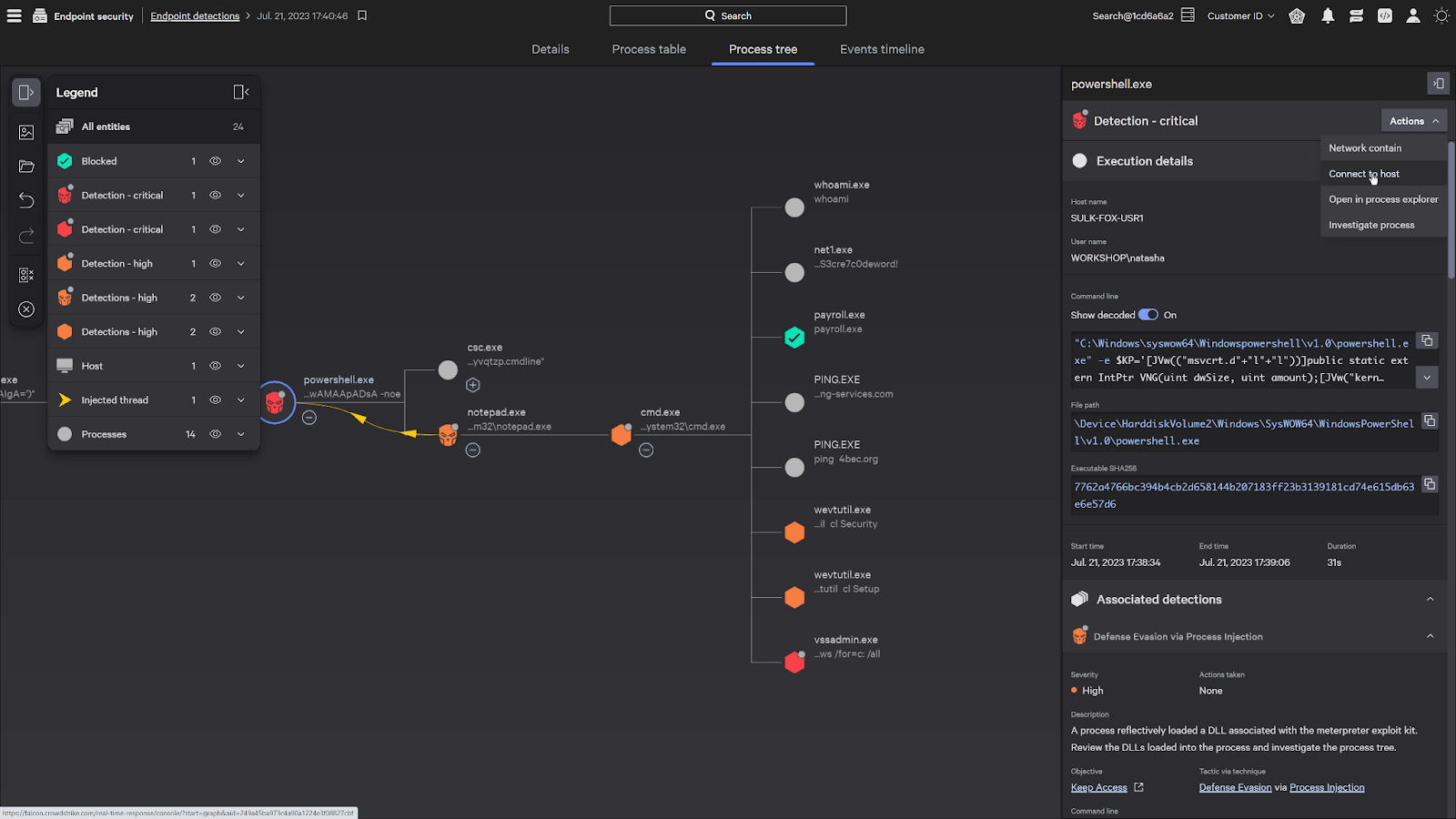
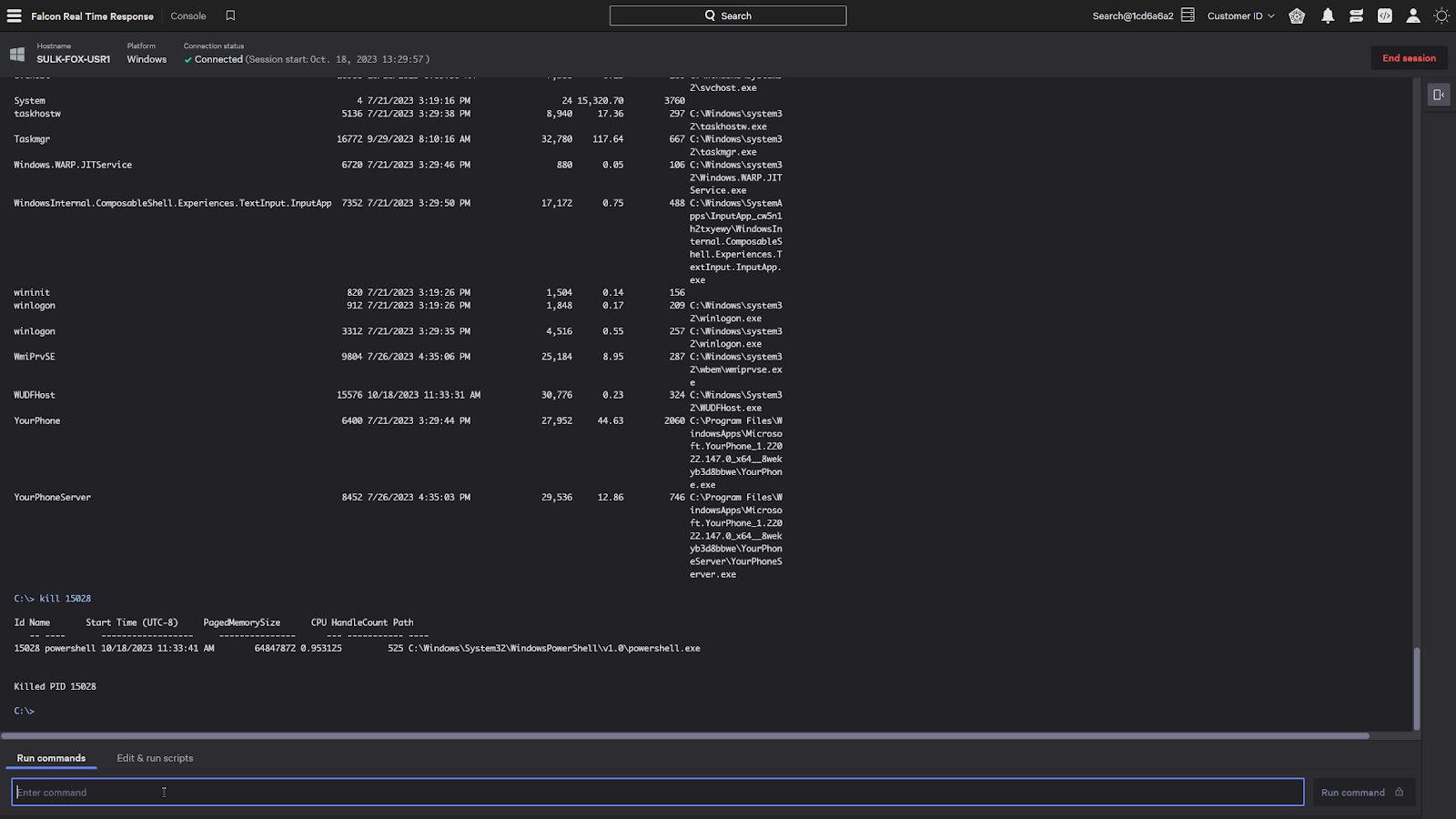
Collect information in real time to investigate incidents by executing commands to show running processes, network activity, or performing memory dumps.
Take instant action by killing rogue processes or removing malicious files to prevent continued adversarial activity.
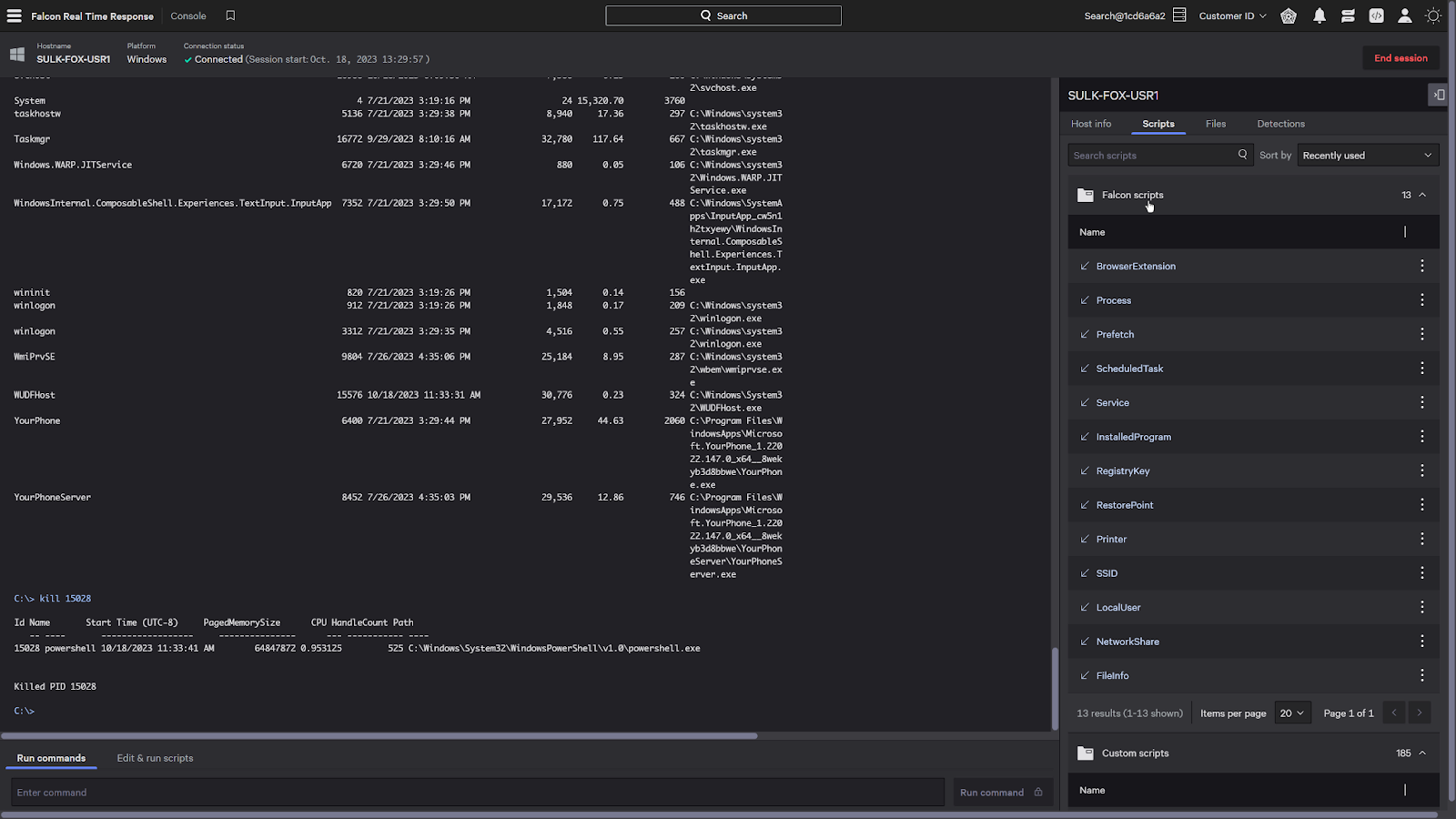
Real Time Response also allows the execution of intricate remediation actions with adaptable scripts, enabling automated execution of advanced commands.
In addition to customizable scripts, built-in Falcon scripts created by experts are provided to help bolster your incident response capabilities, provide critical insights, and enhance your investigations.
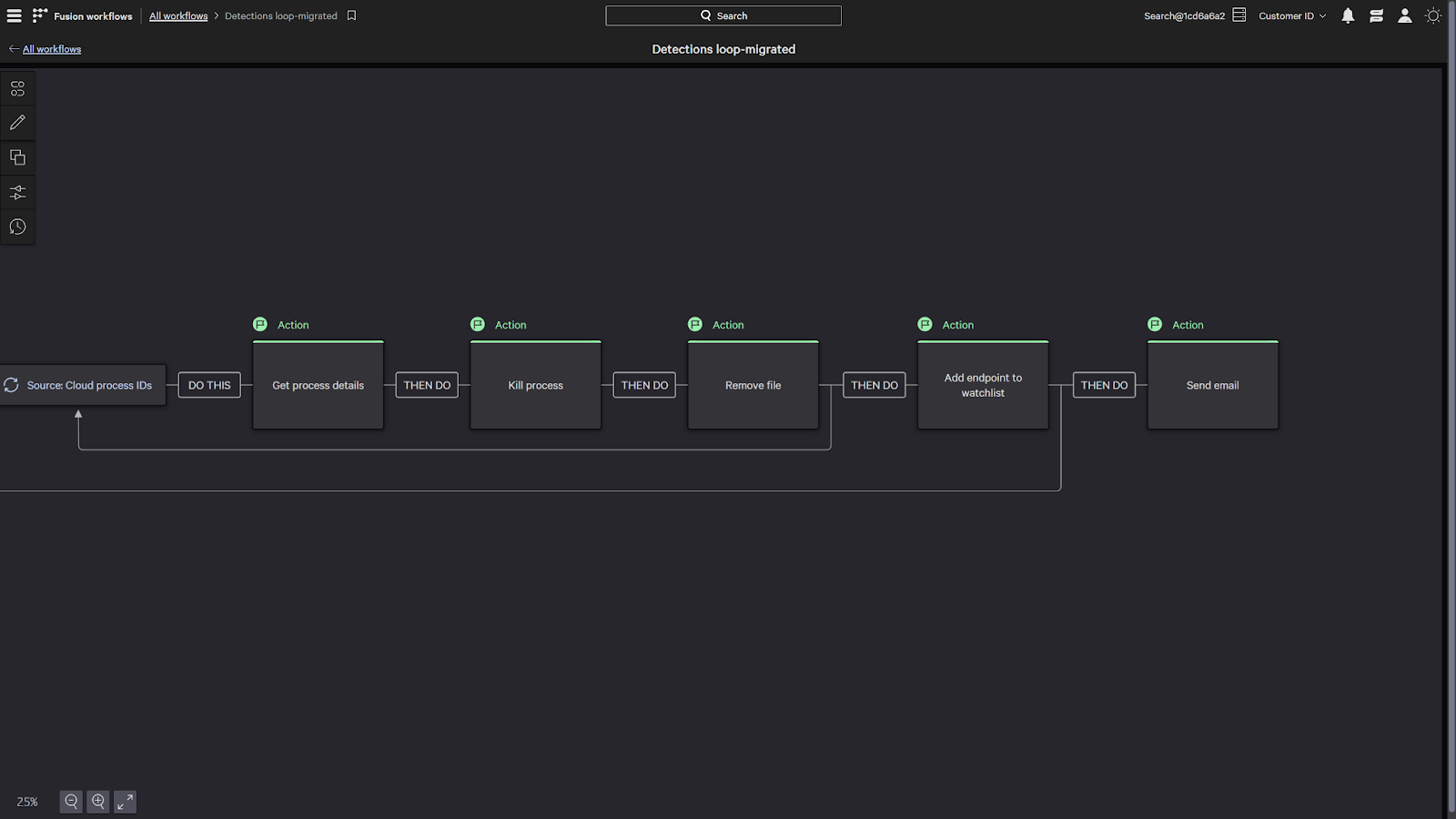
Natively part of the platform, Falcon Fusion can fully automate responses by running Real Time Response on any impacted system with easy to configure playbooks.
Conclusion
CrowdStrike’s Real Time Response enables you to execute precise, immediate remediation actions, and effectively stop breaches.
Contact us to learn how you can stop adversaries faster with CrowdStrike Real Time Response.
