What is malware analysis?
Malware analysis is the process of understanding the behavior and purpose of a suspicious file or URL. The output of the analysis aids in the detection and mitigation of the potential threat.
The key benefit of malware analysis is that it helps incident responders and security analysts:
- Pragmatically triage incidents by level of severity
- Uncover hidden indicators of compromise (IOCs) that should be blocked
- Improve the efficacy of IOC alerts and notifications
- Enrich context when threat hunting
Types of malware analysis
The analysis may be conducted in a manner that is static, dynamic or a hybrid of the two.
Static analysis
Basic static analysis does not require that the code is actually run. Instead, static analysis examines the file for signs of malicious intent. It can be useful to identify malicious infrastructure, libraries or packed files.
Technical indicators are identified such as file names, hashes, strings such as IP addresses, domains, and file header data can be used to determine whether that file is malicious. In addition, tools like disassemblers and network analyzers can be used to observe the malware without actually running it in order to collect information on how the malware works.
However, since static analysis does not actually run the code, sophisticated malware can include malicious runtime behavior that can go undetected. For example, if a file generates a string that then downloads a malicious file based upon the dynamic string, it could go undetected by a basic static analysis. Enterprises have turned to dynamic analysis for a more complete understanding of the behavior of the file.
Dynamic analysis
Dynamic malware analysis executes suspected malicious code in a safe environment called a sandbox. This closed system enables security professionals to watch the malware in action without the risk of letting it infect their system or escape into the enterprise network.
Dynamic analysis provides threat hunters and incident responders with deeper visibility, allowing them to uncover the true nature of a threat. As a secondary benefit, automated sandboxing eliminates the time it would take to reverse engineer a file to discover the malicious code.
The challenge with dynamic analysis is that adversaries are smart, and they know sandboxes are out there, so they have become very good at detecting them. To deceive a sandbox, adversaries hide code inside them that may remain dormant until certain conditions are met. Only then does the code run.
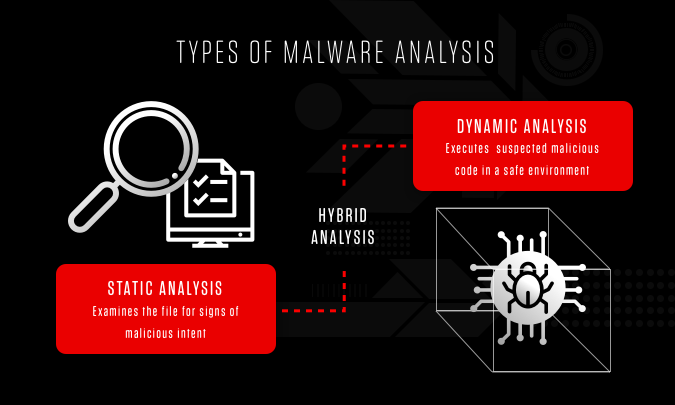
Hybrid analysis (includes both of the techniques above)
Basic static analysis isn’t a reliable way to detect sophisticated malicious code, and sophisticated malware can sometimes hide from the presence of sandbox technology. By combining basic and dynamic analysis techniques, hybrid analysis provide security team the best of both approaches –primarily because it can detect malicious code that is trying to hide, and then can extract many more indicators of compromise (IOCs) by statically and previously unseen code. Hybrid analysis helps detect unknown threats, even those from the most sophisticated malware.
For example, one of the things hybrid analysis does is apply static analysis to data generated by behavioral analysis – like when a piece of malicious code runs and generates some changes in memory. Dynamic analysis would detect that, and analysts would be alerted to circle back and perform basic static analysis on that memory dump. As a result, more IOCs would be generated and zero-day exploits would be exposed.
Learn More
Falcon Sandbox enables cybersecurity teams of all skill levels to increase their understanding of the threats they face and use that knowledge to defend against future attacks.
Malware analysis use cases
Malware detection
Adversaries are employing more sophisticated techniques to avoid traditional detection mechanisms. By providing deep behavioral analysis and by identifying shared code, malicious functionality or infrastructure, threats can be more effectively detected. In addition, an output of malware analysis is the extraction of IOCs. The IOCs may then be fed into SEIMs, threat intelligence platforms (TIPs) and security orchestration tools to aid in alerting teams to related threats in the future.

Threat alerts and triage
Malware analysis solutions provide higher-fidelity alerts earlier in the attack life cycle. Therefore, teams can save time by prioritizing the results of these alerts over other technologies.
Incident response
The goal of the incident response (IR) team is to provide root cause analysis, determine impact and succeed in remediation and recovery. The malware analysis process aids in the efficiency and effectiveness of this effort.
Threat hunting
Malware analysis can expose behavior and artifacts that threat hunters can use to find similar activity, such as access to a particular network connection, port or domain. By searching firewall and proxy logs or SIEM data, teams can use this data to find similar threats.
Malware research
Academic or industry malware researchers perform malware analysis to gain an understanding of the latest techniques, exploits and tools used by adversaries.

Stages of malware analysis
Static properties analysis
Static properties include strings embedded in the malware code, header details, hashes, metadata, embedded resources, etc. This type of data may be all that is needed to create IOCs, and they can be acquired very quickly because there is no need to run the program in order to see them. Insights gathered during the static properties analysis can indicate whether a deeper investigation using more comprehensive techniques is necessary and determine which steps should be taken next.
Interactive behavior analysis
Behavioral analysis is used to observe and interact with a malware sample running in a lab. Analysts seek to understand the sample’s registry, file system, process and network activities. They may also conduct memory forensics to learn how the malware uses memory. If the analysts suspect that the malware has a certain capability, they can set up a simulation to test their theory.
Behavioral analysis requires a creative analyst with advanced skills. The process is time-consuming and complicated and cannot be performed effectively without automated tools.
Fully automated analysis
Fully automated analysis quickly and simply assesses suspicious files. The analysis can determine potential repercussions if the malware were to infiltrate the network and then produce an easy-to-read report that provides fast answers for security teams. Fully automated analysis is the best way to process malware at scale.
Manual code reversing
In this stage, analysts reverse-engineer code using debuggers, disassemblers, compilers and specialized tools to decode encrypted data, determine the logic behind the malware algorithm and understand any hidden capabilities that the malware has not yet exhibited. Code reversing is a rare skill, and executing code reversals takes a great deal of time. For these reasons, malware investigations often skip this step and therefore miss out on a lot of valuable insights into the nature of the malware.
Learn More
Learn about the largest online malware analysis community that is field-tested by tens of thousands of users every day.
The world’s most powerful malware sandbox
Security teams can use the CrowdStrike Falcon® Sandbox to understand sophisticated malware attacks and strengthen their defenses. Falcon Sandbox™ performs deep analyses of evasive and unknown threats, and enriches the results with threat intelligence.
Key benefits of Falcon Sandbox
- Provides in-depth insight into all file, network and memory activity
- Offers leading anti-sandbox detection technology
- Generates intuitive reports with forensic data available on demand
- Supports the MITRE ATT&CK® framework
- Orchestrates workflows with an extensive application programming interface (API) and pre-built integrations
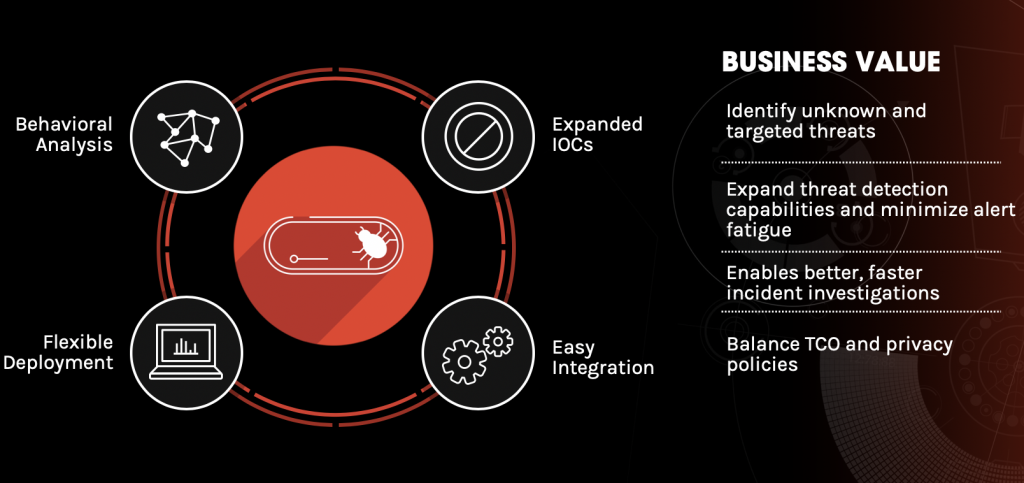
Detect unknown threats
Falcon Sandbox extracts more IOCs than any other competing sandbox solution by using a unique hybrid analysis technology to detect unknown and zero-day exploits. All data extracted from the hybrid analysis engine is processed automatically and integrated into Falcon Sandbox reports.
Falcon Sandbox has anti-evasion technology that includes state-of-the-art anti-sandbox detection. File monitoring runs in the kernel and cannot be observed by user-mode applications. There is no agent that can be easily identified by malware, and each release is continuously tested to ensure Falcon Sandbox is nearly undetectable, even by malware using the most sophisticated sandbox detection techniques. The environment can be customized by date/time, environmental variables, user behaviors and more.
Identify related threats
Know how to defend against an attack by understanding the adversary. Falcon Sandbox provides insights into who is behind a malware attack through the use of malware search a unique capability that determines whether a malware file is related to a larger campaign, malware family or threat actor. Falcon Sandbox will automatically search the largest malware search engine in the cybersecurity industry to find related samples and, within seconds, expand the analysis to include all files. This is important because it provides analysts with a deeper understanding of the attack and a larger set of IOCs that can be used to better protect the organization.
Achieve complete visibility
Uncover the full attack life cycle with in-depth insight into all file, network, memory and process activity. Analysts at every level gain access to easy-to-read reports that make them more effective in their roles. The reports provide practical guidance for threat prioritization and response, so IR teams can hunt threats and forensic teams can drill down into memory captures and stack traces for a deeper analysis. Falcon Sandbox analyzes over 40 different file types that include a wide variety of executables, document and image formats, and script and archive files, and it supports Windows, Linux and Android.
Respond faster
Security teams are more effective and faster to respond thanks to Falcon Sandbox’s easy-to-understand reports, actionable IOCs and seamless integration. Threat scoring and incident response summaries make immediate triage a reality, and reports enriched with information and IOCs from CrowdStrike Falcon® MalQuery™ and CrowdStrike Adversary Intelligence provide the context needed to make faster, better decisions.
Falcon Sandbox integrates through an easy REST API, pre-built integrations, and support for indicator-sharing formats such as Structured Threat Information Expression™ (STIX), OpenIOC, Malware Attribute Enumeration and Characterization™ (MAEC), Malware Sharing Application Platform (MISP) and XML/JSON (Extensible Markup Language/JavaScript Object Notation). Results can be delivered with SIEMs, TIPs and orchestration systems.
Cloud or on-premises deployment is available. The cloud option provides immediate time-to-value and reduced infrastructure costs, while the on-premises option enables users to lock down and process samples solely within their environment. Both options provide a secure and scalable sandbox environment.
Automation
Falcon Sandbox uses a unique hybrid analysis technology that includes automatic detection and analysis of unknown threats. All data extracted from the hybrid analysis engine is processed automatically and integrated into the Falcon Sandbox reports. Automation enables Falcon Sandbox to process up to 25,000 files per month and create larger-scale distribution using load-balancing. Users retain control through the ability to customize settings and determine how malware is detonated.
Learn how CrowdStrike can help you get more out of malware analysis:






