CrowdStrike Falcon OverWatch™ recently released its annual threat hunting report, detailing the interactive intrusion activity observed by hunters over the course of the past year. Intrusions against the telecommunications industry emerged as a common trend, and were examined in-depth through the report. The case study below shares insights into activity at a telecommunication organization in the Middle East, Turkey and Africa (META) region, made notable by the presence of two distinct threat actors operating in the same network simultaneously. For further detail, download the CrowdStrike 2021 Threat Hunting Report today.
 Harvesting valid user credentials is a common mission objective for both targeted and eCrime actors. For targeted threat actors, such as LightBasin, it can be instrumental in fulfilling information gathering objectives. In the case of eCrime actors, credential gathering can often be a means to broaden their reach across a victim network with the goal of increasing the impact of their ultimate mission objective.
Both actors also diligently attempted to evade detection and conceal their operations. OverWatch observed the use of at least five distinct defense evasion techniques across both Windows and Linux hosts, aimed at ensuring the actors could conduct their operations without catching the eye of defenders. These included multiple techniques for clearing of artifacts, as well as masquerading malicious tooling, and registry modification to hide recent Remote Desktop Protocol (RDP) connections. Notably, OverWatch also observed LightBasin operating from hosts without Falcon
Harvesting valid user credentials is a common mission objective for both targeted and eCrime actors. For targeted threat actors, such as LightBasin, it can be instrumental in fulfilling information gathering objectives. In the case of eCrime actors, credential gathering can often be a means to broaden their reach across a victim network with the goal of increasing the impact of their ultimate mission objective.
Both actors also diligently attempted to evade detection and conceal their operations. OverWatch observed the use of at least five distinct defense evasion techniques across both Windows and Linux hosts, aimed at ensuring the actors could conduct their operations without catching the eye of defenders. These included multiple techniques for clearing of artifacts, as well as masquerading malicious tooling, and registry modification to hide recent Remote Desktop Protocol (RDP) connections. Notably, OverWatch also observed LightBasin operating from hosts without Falcon
Telecommunications in Focus
Over the past year, OverWatch observed the number of interactive intrusion attempts against the telecommunications industry double. This activity spanned all major geographic regions and was tied to a diverse range of adversaries. While OverWatch certainly sees eCrime activity against the telecommunications industry, it stands out as one of the few industry verticals that is much more commonly a victim of targeted (i.e., state-nexus) intrusion activity. Targeted intrusion adversaries often conduct operations against telecommunications providers to fulfill their surveillance, intelligence and counterintelligence collection priorities. This includes accessing information such as call detail records and, in the case of mobile providers, SMS communications.
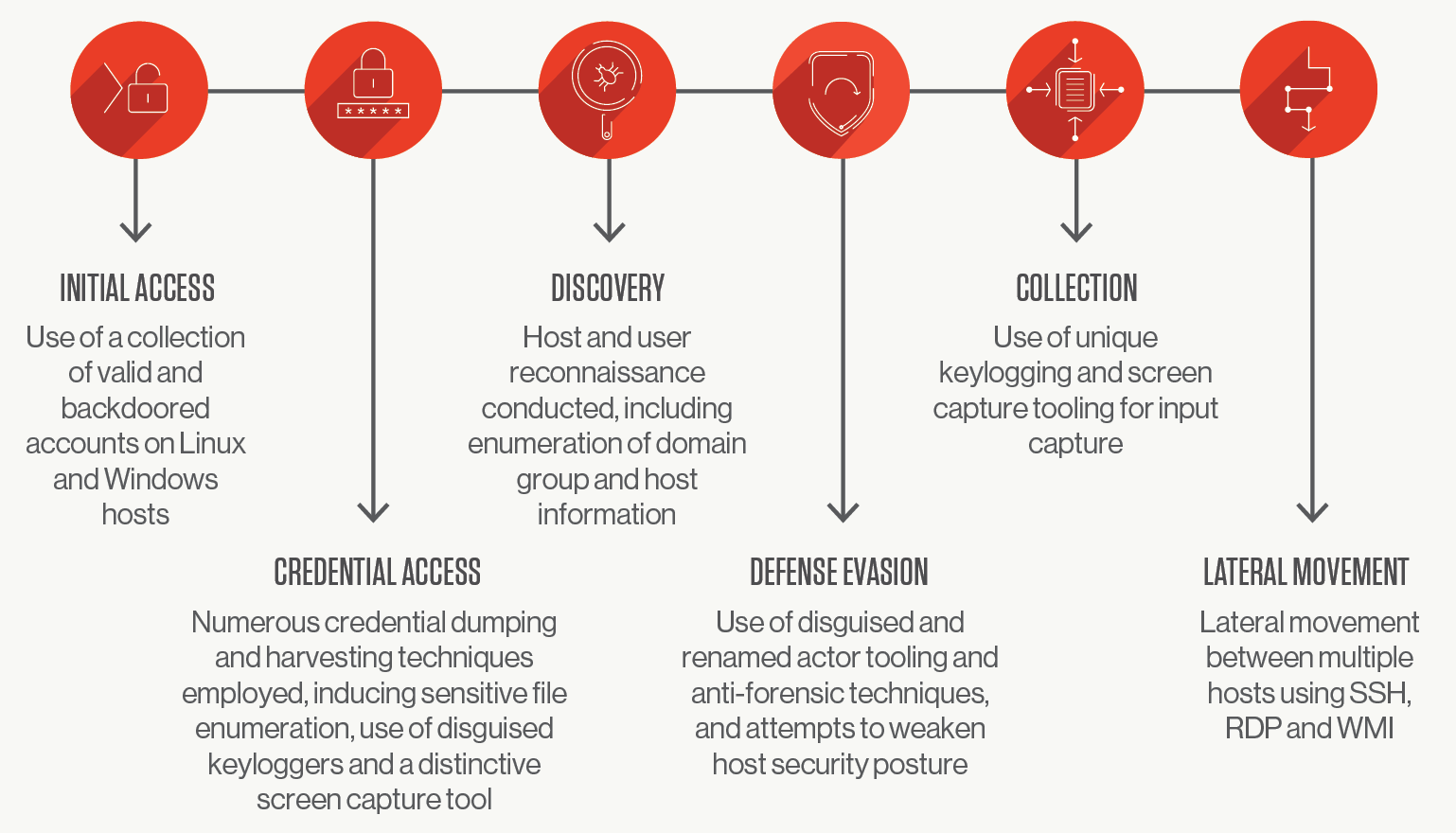
OverWatch Uncovers Double Trouble in the Wires
In this intrusion, two threat actors were observed conducting actions on objectives across a selection of both Linux- and Windows-based hosts. The actors were operating simultaneously and seemingly unbeknownst to each other. The tradecraft observed in the Linux environment overlaps with previously observed activity tracked by CrowdStrike Intelligence as part of the LightBasin activity cluster — assessed with moderate confidence as being targeted activity. In contrast, the activity observed in the organization’s Windows environment is suspected to have been carried out by an eCrime actor. As illustrated below, both threat actors used a collection of valid accounts and backdoored accounts to gain entry into Linux and Windows hosts, where both threat actors then began numerous credential dumping and harvesting techniques. Many of these techniques were successfully prevented by the CrowdStrike Falcon®® sensor.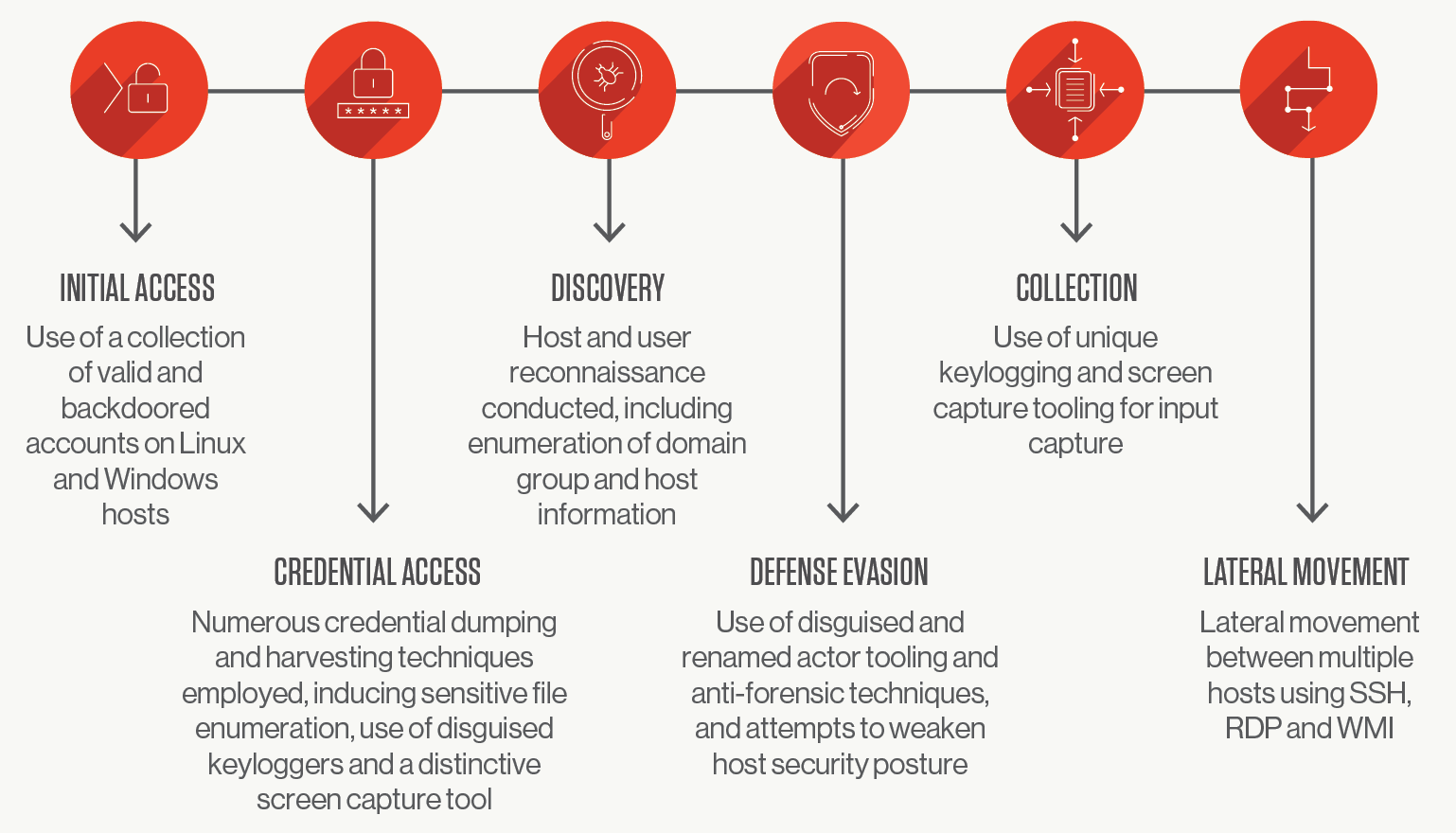 Harvesting valid user credentials is a common mission objective for both targeted and eCrime actors. For targeted threat actors, such as LightBasin, it can be instrumental in fulfilling information gathering objectives. In the case of eCrime actors, credential gathering can often be a means to broaden their reach across a victim network with the goal of increasing the impact of their ultimate mission objective.
Both actors also diligently attempted to evade detection and conceal their operations. OverWatch observed the use of at least five distinct defense evasion techniques across both Windows and Linux hosts, aimed at ensuring the actors could conduct their operations without catching the eye of defenders. These included multiple techniques for clearing of artifacts, as well as masquerading malicious tooling, and registry modification to hide recent Remote Desktop Protocol (RDP) connections. Notably, OverWatch also observed LightBasin operating from hosts without Falcon
Harvesting valid user credentials is a common mission objective for both targeted and eCrime actors. For targeted threat actors, such as LightBasin, it can be instrumental in fulfilling information gathering objectives. In the case of eCrime actors, credential gathering can often be a means to broaden their reach across a victim network with the goal of increasing the impact of their ultimate mission objective.
Both actors also diligently attempted to evade detection and conceal their operations. OverWatch observed the use of at least five distinct defense evasion techniques across both Windows and Linux hosts, aimed at ensuring the actors could conduct their operations without catching the eye of defenders. These included multiple techniques for clearing of artifacts, as well as masquerading malicious tooling, and registry modification to hide recent Remote Desktop Protocol (RDP) connections. Notably, OverWatch also observed LightBasin operating from hosts without Falconsensor coverage. Endpoints not covered by comprehensive endpoint protection create a
potential blindspot for adversaries to operate from. OverWatch strongly recommends that full endpoint protection including next-generation antivirus (NGAV) and endpoint detection and response (EDR) is deployed across all endpoints.
Screen Capture Provides a Window for Threat Actors
A point of difference in this intrusion was the use of the screen capture technique to collect information. Screen capture allows threat actors to capture sensitive information from a victim’s desktop by taking a single screen capture at any point in time. Threat actors can also schedule screen captures to take place at regular intervals. In this intrusion, threat actors used custom tooling to conduct screen capture activity. However, this can also be achieved by abusing existing system features or using native/legitimate utilities.This technique is powerful in the hands of threat actors as it provides them with the means of collecting a rich stream of sensitive information directly from a victim’s desktop. This could include, but is by no means limited to, banking information, unprotected login information, and the contents of emails and/or instant messaging communications.
Because this technique takes advantage of an inherent abuse of system resources, technology-based controls are often not enough to detect and disrupt this type of malicious activity. In contrast, continuous human-led threat hunting analyzes and looks at the behaviors associated with malicious screen capture — the writing of image files to the disk, the deployment and execution of file compression and archival utilities, etc. — and can better detect this type of anomalous traffic and disrupt it before significant damage can be done.
Recommendations for Defenders
Several features of this intrusion would likely cause challenges for defenders reliant only on technology-based controls. In particular, having threat actors deeply entrenched in the victim environment, possessing a vast array of compromised and privileged accounts, and using collection techniques such as screen capture. In this instance, OverWatch effectively bridged the gap for the victim organization and armed defenders with the vital context and actionable intelligence necessary — ultimately enabling them to disrupt the threat actors.Defenders looking to combat the abuse of valid accounts should ensure they maintain strict user and privileged account management practices. This includes avoiding the use of default accounts, regularly auditing account permissions, deploying multifactor authentication (MFA), and employing the concept of least privilege. Defenders should also avoid storing any sensitive or credential-related information in unencrypted files.
Lastly, the importance of continuous proactive threat hunting, such as that provided by OverWatch, cannot be overstated. Today’s highly motivated threat actors, regardless of their mission objective, are more diligent than ever about maintaining stealth by obscuring their activities so they are not perceived by technology-based defenses. For defenders looking to ensure their organization is protected from evasive and stealthy techniques, human driven threat hunting capabilities are a must have. To read more about the tactics, techniques and procedures (TTPs) employed by these two adversaries and to see specific indicators of compromise from this intrusion, download your copy of the OverWatch 2021 Threat Hunting Report. Inside you’ll also find a 10,000-foot overview of the threat landscape as observed by industry-leading threat hunters, six in-depth intrusion features, an exclusive look at the TTPs OverWatch threat hunters think defenders should look out for, and much more.
Additional Resources
- Read about the latest trends in threat hunting and more in the 2021 Threat Hunting Report or simply download the report now.
- Learn more about Falcon OverWatch proactive managed threat hunting.
- Watch this video to see how Falcon OverWatch proactively hunts for threats in your environment.
- Read more about how hunting part-time is simply not enough in this CrowdStrike blog.
- Learn more about the CrowdStrike Falcon® platform by visiting the product webpage.
- Test CrowdStrike next-gen AV for yourself. Start your free trial of Falcon Prevent™ today.
- Learn more on how Falcon Spotlight™ can help you discover and manage vulnerabilities in your environments.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)










































