How to Integrate with your SIEM

The greatest minds in cybersecurity are at Fal.Con in Las Vegas, Sept. 18-21.
Register now to build skills at hands-on workshops and learn from skilled threat hunters.
Introduction
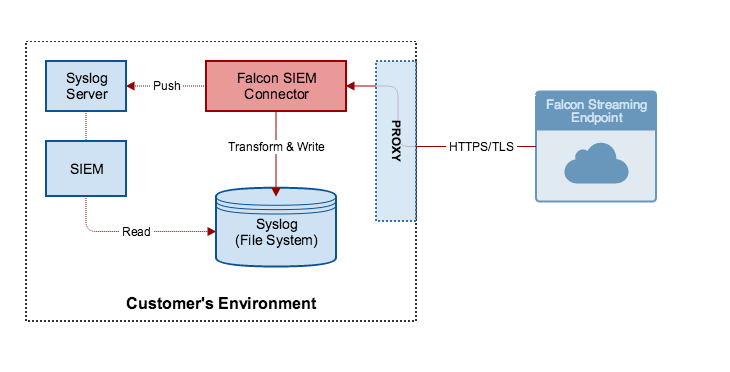
The Falcon SIEM Connector provides users a turnkey, SIEM-consumable data stream. The Falcon SIEM Connector:
- Transforms CrowdStrike API data into a format that a SIEM can consume
- Maintains the connection to the CrowdStrike Event Streaming API and your SIEM
- Manages the data-stream pointer to prevent data loss
Prerequisites
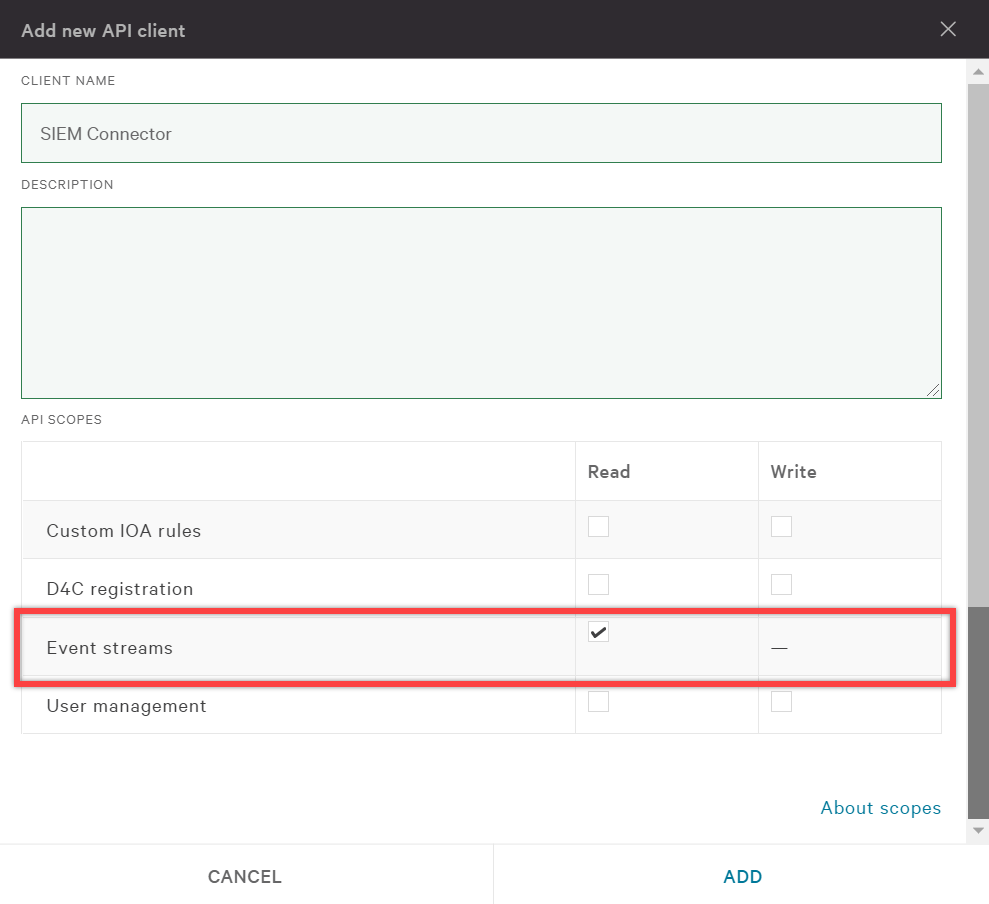
Before using the Falcon SIEM Connector, you’ll want to first define the API client and set its scope. Refer to this guide to getting access to the CrowdStrike API for setting up a new API client key. For the new API client, make sure the scope includes read access for Event streams.
Links to Installation and Configuration for the CrowdStrike Falcon® SIEM Connector
The CrowdStrike Falcon® SIEM Connector (SIEM Connector) runs as a service on a local Linux server.
The following links provide Installation and Configuration documentation for each CrowdStrike Cloud.
The process above shows how to get started with the CrowdStrike Falcon® SIEM Connector. There are many more options for this connector (using a proxy to reach the streaming API, custom log formats and syslog configurations, etc.) that can be found in the “SIEM Connector” as part of the Documentation package in the Falcon UI.


