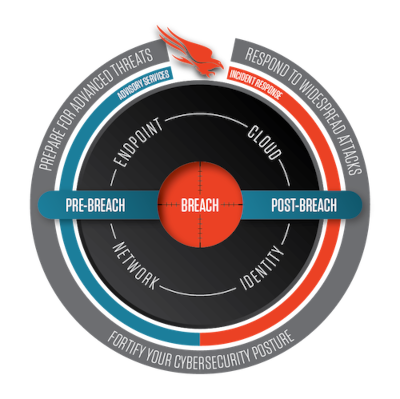
Prepare:
Advisory Services
Advisory Services
CrowdStrike Services help you prepare and train to defend your organization against sophisticated threat actors using real-life simulation exercises.
Service offerings
Tabletop Exercise
Tabletop Exercise
Leveraging the Service team’s experience, CrowdStrike will guide your organization – both executive and technical participants – through a targeted attack scenario in the Tabletop Exercise. This discussion-based exercise simulates a targeted attack in a time-compressed fashion, but without the risk and time required for a full adversary emulation.

Adversary Emulation Exercise
Adversary Emulation Exercise
Adversary Emulation is the most realistic way to gauge your organization’s readiness and ability to defend against a targeted attack. During this simulated attack, the Services team takes a step-by-step approach that follows the attack kill chain, mimicking tactics, techniques and procedures (TTPs) used by real-world adversaries as they try to gain access to your network

Red Team / Blue Team Exercise
Red Team / Blue Team Exercise
Too often, an organization is compromised and the security team doesn’t see an alert. This could be due to multiple factors such as;, a lack of skilled people, inadequate processes, or misconfigured technology. By conducting a CrowdStrike Services Red Team / Blue Team Exercise, organizations are able to identify the gaps in their security postures that limit their ability to detect malicious activity.

Penetration Testing Services
Penetration Testing Services
Penetration Testing, or Pen Testing, is the simulation of real-world attacks in order to test your organization’s detection and response capabilities. The purpose of Pen Testing is not just to identify your environment’s vulnerabilities, but also to test your people and processes against likely threats to your organization. Knowing which adversaries are more likely to target you allows pen testers to mimic the exact TTPs of those specific adversaries — giving your organization a much more realistic picture of how a breach might occur.

Experienced a breach?
Get immediate assistance
What our customers say
"The team was great to work with and designed a very interesting incident for our technical walkthrough after learning about our environment. "
Finance: Global Atlantic Financial
Adrian Vargas - AVP, Information Security Risk Management
"I am highly satisfied with the quality of service provided by CrowdStrike. "
Information Technology: ServiceNow
Bhavesh Goswami - Technical Manager, Incident Response