- Fourteen key cloud analytics for Azure and GCP cloud environments were identified and mapped as indicative of adversary behavior and serve as a blueprint for understanding and writing new cloud analytics.
- The CrowdStrike Falcon® platform delivers a powerful combination of agentless capabilities to protect against misconfigurations and control plane attacks, along with agent-based runtime security to proactively secure cloud environments by harmonizing real-time cloud-native events and TTPs to comprehensively detect adversaries.
CrowdStrike is a Research Sponsor in the Cloud Analytics project — a new MITRE Center for Threat-Informed Defense initiative (CTID) to capture key adversarial tactics, techniques and procedures (TTPs) to improve detection of threat actor behavior in cloud environments. CrowdStrike’s work with the CTID lays the groundwork for advancing public cloud security.
The goal of the project was to map analytics across disparate infrastructures and cloud services to reduce alert noise and quickly identify abnormal and evasive behaviors faster than going through each separate infrastructure. The project uncovered 14 key cloud analytics for Azure and GCP cloud environments mapped to the MITRE ATT&CK® Cloud Matrix and indicative of cloud-specific adversary behavior.

The CrowdStrike Falcon® platform identifies and protects customers against all adversary tactics uncovered in the project. CrowdStrike delivers comprehensive cloud security by combining agent-based and agentless protection in a single, unified platform experience using machine learning and indicators of attack (IOAs) to observe, detect, remediate and prevent adversarial or anomalous activities. The results of this research are presented in a blueprint document that maps some of the key cloud analytics and offers best practices and lessons learned. Protectors can use this document as a guide for identifying and mapping cloud analytics in their environments.
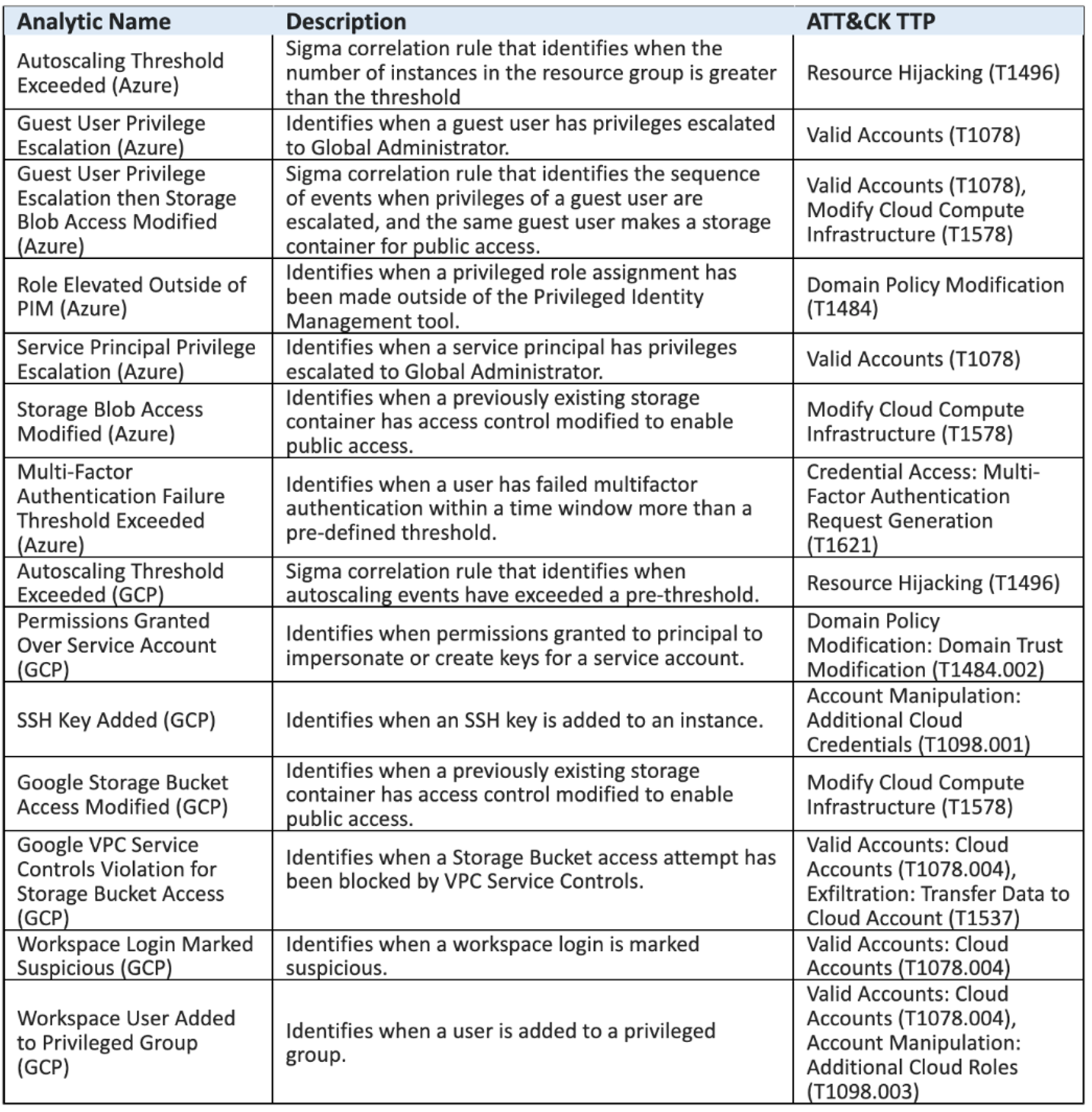 Figure 1. The 14 key cloud analytics for Azure and GCP cloud environments identified in the MITRE CTID Cloud Analytics project (source) (click to enlarge)
Figure 1. The 14 key cloud analytics for Azure and GCP cloud environments identified in the MITRE CTID Cloud Analytics project (source) (click to enlarge)Detecting Adversaries in the Cloud Is Hard
Detecting adversaries using cloud analytics is hard — because it’s expensive to do it right. You must ingest and store large amounts of log data, you need the right people looking at the data, and you need tooling and time to make the cloud data reveal adversaries without false positives.
At the same time, adversarial TTPs in the cloud have been evolving rapidly, revealing the critical need for defenders to have both real-time visibility into the cloud control plane and targeted activity analytics to observe, hunt and remediate cloud-based threats.
The industry is trying to solve cloud security by managing configurations or applying a legacy antivirus mindset to it. Neither will succeed. Comprehensively securing cloud environments requires the powerful combination of agentless capabilities that protect against misconfigurations and control plane attacks, along with agent-based runtime security to protect your workloads. The growing volume, velocity and variety of cloud logs, coupled with log file-based monitoring, makes it incredibly difficult for analysts to identify adversary behaviors in real time to stop breaches. Adversary breakout time — the time from when an adversary infiltrates a system to when they move laterally across the organization’s network — is now 1 hour and 24 minutes, according to the 2022 Falcon OverWatch Threat Hunting Report, leaving analysts with a short window of opportunity to identify and contain threats to their infrastructure — otherwise the organization could suffer a costly breach if the threat actor is able to move laterally and expand across the cloud estate. Traditional approaches to cloud security, such as securing the access layer — for example, the cloud access security broker (CASB) — are not enough as adversaries employ a wide range of TTPs. What’s necessary to stop breaches is access to usable, accurate and actionable real-time analytics and cloud controls.
CrowdStrike Leads the Way in Cloud Workload Protection
The CrowdStrike Falcon® platform was born in the cloud with a mission to stop breaches. CrowdStrike understands how to secure cloud environments using cloud-native IOAs to solve the current challenges the industry is experiencing with cloud analytics.
The CrowdStrike Falcon® platform sets the new standard in cloud security. Watch this demo to see the Falcon platform in action.
The Falcon platform can offer behavioral detections by using the power of the CrowdStrike Security Cloud and cloud data analytics to harmonize runtime events and produce cloud analytics indicative of real-time adversary behavior. It correlates new and historical events and malicious indicators, such as suspicious login activity or privilege escalations, to detect adversarial behavioral patterns against end-to-end activity events from the cloud control planes in near real time.
For example, CrowdStrike’s AWS IAM policy behavior detection monitoring will alert customers when an API call has been made to modify an IAM role policy to allow public access — essentially allowing a public AWS user to inherit the permissions granted by the IAM role. This behavior could be used by an adversary to expand and elevate their access via a user account they already control.
CrowdStrike’s Automated Cryptocurrency Miner Attack alert monitors for and alerts customers when a rapid series of calls are observed to the EC2 service that often aligns with how adversaries set up miners. This may include EC2 enumeration, VPC creation and instance run commands all executed in quick succession. The Falcon platform provides visibility into your entire cloud infrastructure, continuous monitoring for misconfigurations, and proactive threat detection — allowing organizations to stop breaches in their tracks with unified visibility, threat detection and continuous monitoring and compliance for multi-cloud environments. CrowdStrike Falcon® Cloud Security can look beyond configurations to alert organizations when suspicious activity is detected, such as the rapid sequence of calls that would be used by an attacker launching a scripted mining attack. Falcon Cloud Security provides granular policy assessment and visibility to help organizations instantly identify potential exposures, resolve findings, detect and prevent identity-based threats across hybrid and multi-cloud environments and minimize overall risk. CrowdStrike’s expertise in securing cloud infrastructures from sophisticated adversaries demonstrates that we understand what the current industry challenges are and we have addressed them with a clear adversary-focused approach to detecting malicious behavior to stop breaches. With the CrowdStrike Falcon® platform, organizations can secure their entire cloud-native stack, on any cloud, across all workloads, containers and applications as it enables them to automate security and detect and stop suspicious activity and risky behavior, to stay ahead of threats and reduce the attack surface.
See for yourself how the industry-leading CrowdStrike Falcon® platform protects your cloud environments. Start your 15-day free trial today.
CrowdStrike is proud to partner with MITRE CTID to advance cybersecurity in the public interest, in particular to help organizations improve visibility and understanding of adversary tradecraft. Past initiatives such as the Top MITRE ATT&CK® Techniques project — which enabled defenders to prioritize and take actions against key TTPs — as well as the recent Cloud Analytics project underline our commitment to leading the way in advancing the state of security so defenders can better secure their infrastructures.
Additional Resources
- Learn more about the CrowdStrike partnership with MITRE in this blog: CrowdStrike Partners with MITRE CTID, Reveals Real-world Insider Threat Techniques
- For an in-depth examination of how attackers target the cloud, download “Protectors of the Cloud: Combating the Rise in Threats to Cloud Environments.”
- Learn how you can stop cloud breaches with CrowdStrike unified cloud security posture management and breach prevention for multi-cloud and hybrid environments — all in one lightweight platform.
- Read about adversaries tracked by CrowdStrike in 2021 in the 2023 CrowdStrike Global Threat Report and in the 2022 Falcon OverWatch™ Threat Hunting Report.
- Test CrowdStrike next-gen AV for yourself. Start your free trial of Falcon Prevent™ today.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)