This blog was originally published on June 11, 2019.
On June 2019 Patch Tuesday, Microsoft released patches for CVE-2019-1040 and CVE-2019-1019, two vulnerabilities discovered by Preempt (now CrowdStrike) researchers. The critical vulnerabilities consist of three logical flaws in NTLM (Microsoft’s proprietary authentication protocol). Preempt researchers were able to bypass all major NTLM protection mechanisms.
These vulnerabilities allow attackers to remotely execute malicious code on any Windows machine or authenticate to any HTTP server that supports Windows Integrated Authentication (WIA) such as Exchange or ADFS. All Windows versions which did not apply this patch are vulnerable.
 Over the years, Microsoft has developed several mitigations for thwarting such NTLM relay attacks. Preempt researchers were able to bypass all the significant defense mechanisms:
Over the years, Microsoft has developed several mitigations for thwarting such NTLM relay attacks. Preempt researchers were able to bypass all the significant defense mechanisms:
Attack Details
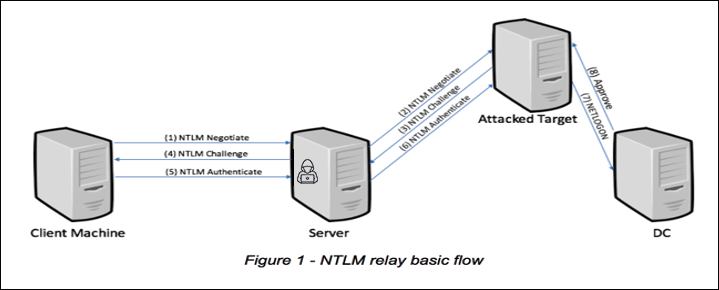
NTLM authentication protocol is susceptible to relay attacks. NTLM relay is a common attack technique where an attacker that compromises one machine can move laterally to other machines by using NTLM authentication directed at the compromised server. Over the years, Microsoft has developed several mitigations for thwarting such NTLM relay attacks. Preempt researchers were able to bypass all the significant defense mechanisms:
Over the years, Microsoft has developed several mitigations for thwarting such NTLM relay attacks. Preempt researchers were able to bypass all the significant defense mechanisms:
- SMB Session Signing: Prevents attackers from relaying NTLM authentication messages to establish SMB and DCE/RPC sessions. The bypass we discovered enables attackers to relay NTLM authentication requests to any server in the domain, including domain controllers while establishing a signed session to perform remote code execution. If the relayed authentication is of a privileged user, this means full domain compromise.
- Message Integrity Code (MIC): The MIC field ensures that NTLM messages are not tampered by attackers. However, our bypass allows attackers to remove the MIC protection and modify various fields in the NTLM authentication flow, such as signing negotiation.
- Enhanced Protection for Authentication (EPA): Prevents attackers from relaying NTLM messages to TLS sessions. Our bypass allows attackers to modify NTLM messages to generate legitimate channel binding information. This can allow attackers to connect to various web servers using the attacked user’s privileges and perform operations such as reing the user’s emails (by relaying to OWA servers) or even connecting to cloud resources (by relaying to ADFS servers).
How can I protect myself from these vulnerabilities?
Here are the main steps you need to take to make sure you are protected from these threats:- Patch: Make sure workstations and servers are properly patched. This is a basic requirement, but it is important to note that patching alone is not enough as you will also need to make configuration changes in order to be fully protected.
- Configuration:
- Enforce SMB Signing: To prevent attackers from launching simpler NTLM relay attacks, turn on SMB signing on all machines in the network.
- Block NTLMv1: Since NTLMv1 is considered less secure, it is recommended to completely block it by setting the appropriate GPO.
- Enforce LDAP/S Signing: To prevent NTLM relay in LDAP, enforce LDAP signing and LDAPS channel binding on domain controllers.
- Enforce EPA: To prevent NTLM relay on web servers, harden all web servers (OWA, ADFS) to accept only requests with EPA.
- Reduce NTLM usage: Even with a fully secure configuration and fully patched servers NTLM still poses a significantly greater risk than Kerberos. It is recommended that you remove NTLM anywhere it is not needed.
Additional Resources
- Learn more by reading the white paper, “The Security Risk of NTLM.”
- Visit the CrowdStrike Falcon® Identity Protection solutions webpage.
- Request a demo of CrowdStrike Falcon Zero Trust or Falcon Identity Threat Detection products.
- Read expert insights and analysis on other complex threats — download the CrowdStrike 2020 Global Threat Report.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)


?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)






































