Limited data retention resulting from financial or technological constraints makes it hard for security teams to see the complete history of an attack. This lack of full context about a threat — or a potential threat — eventually catches up with organizations, leading to longer dwell times and increased risk of a breach. The innovative technology addresses one of the biggest challenges in threat hunting and security awareness: unknown unknowns. Without the context provided by log and event data from across your IT infrastructure, it’s increasingly difficult to investigate incidents and uncover potential attack paths. Despite this, historical retention is often a problem for security teams because of the costs and technological complexity of retaining this data.
The innovative technology addresses one of the biggest challenges in threat hunting and security awareness: unknown unknowns. Without the context provided by log and event data from across your IT infrastructure, it’s increasingly difficult to investigate incidents and uncover potential attack paths. Despite this, historical retention is often a problem for security teams because of the costs and technological complexity of retaining this data.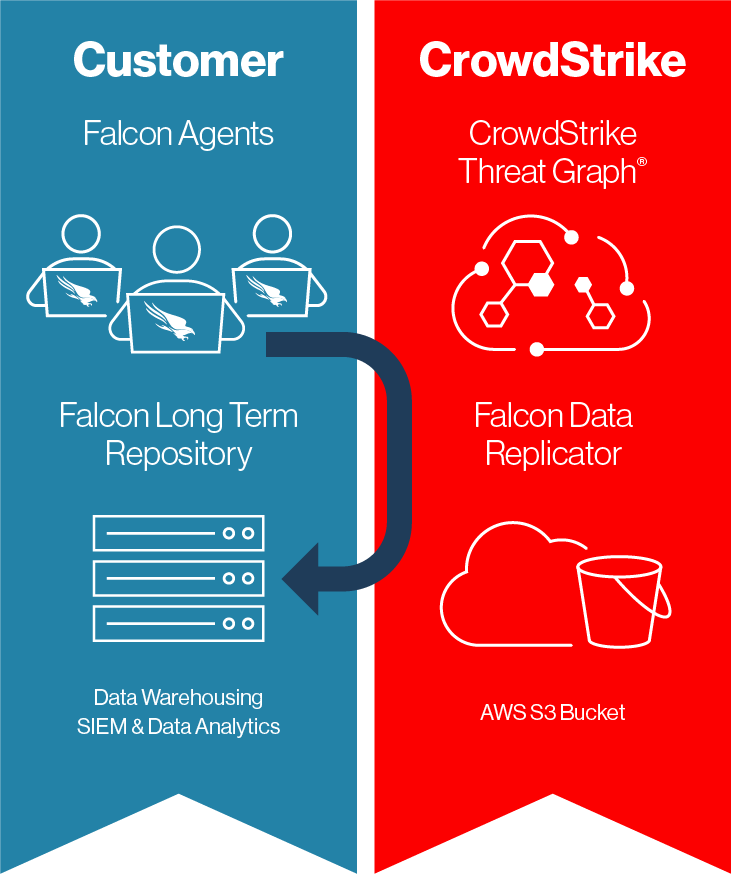 Note: Customers using self-hosted deployments of Falcon LTR must use Falcon Data Replicator instead of the CrowdStrike Data Connector to bring data into the platform.
Note: Customers using self-hosted deployments of Falcon LTR must use Falcon Data Replicator instead of the CrowdStrike Data Connector to bring data into the platform.
CrowdStrike Falcon® Long Term Repository (LTR), formerly known as Humio for Falcon, allows CrowdStrike Falcon® platform customers to retain their data for up to one year or longer. Users can then correlate this deep well of information with other data sources to better detect potential threats and search the data with sub-second latency.
 The innovative technology addresses one of the biggest challenges in threat hunting and security awareness: unknown unknowns. Without the context provided by log and event data from across your IT infrastructure, it’s increasingly difficult to investigate incidents and uncover potential attack paths. Despite this, historical retention is often a problem for security teams because of the costs and technological complexity of retaining this data.
The innovative technology addresses one of the biggest challenges in threat hunting and security awareness: unknown unknowns. Without the context provided by log and event data from across your IT infrastructure, it’s increasingly difficult to investigate incidents and uncover potential attack paths. Despite this, historical retention is often a problem for security teams because of the costs and technological complexity of retaining this data.Falcon LTR employs an index-free architecture designed to minimize the storage and computing resources required to ingest and retain data at any scale. It also uses advanced data storage techniques to compress data by 6-80x, reducing total cost of ownership.
If you’re a Falcon platform customer who wants more data to work with for a longer period of time, Falcon LTR might be right for you. This blog post is the first in a three-part series that will teach you the basics of Falcon LTR and how it can improve your threat hunts, investigations and observability use cases. Let’s dive in.
I’ve got a data warehouse. Why do I need Falcon LTR?
Most organizations will ingest log data into their own data warehouse, perform custom analytics and investigations, and define an event-retention policy based on the storage available. Falcon LTR improves upon this approach in four main ways:- Longer data retention. Falcon LTR allows you to keep data for as long as you need, including more than one year. With longer data retention, security teams can identify potential threats faster and conduct sub-second searches on log data. This speed enables threat hunting and troubleshooting at an unprecedented scale.
- Reduced cost. Legacy log management platforms make it cost prohibitive due to extensive infrastructure and storage requirements to retain log data long term. Falcon LTR offers long-term retention that requires minimal storage and computing resources, thus costing much less than what you might be used to.
- Fast and custom search. Humio, the log management technology that powers Falcon LTR, offers a feature-rich query language and index-free architecture. This allows customers to get immediate answers from their Falcon data via real-time dashboards, custom searches and prebuilt integrations.
- Smarter investigations. By ingesting your Falcon data into Falcon LTR, it instantly becomes searchable alongside other data sources, such as firewall logs and network telemetry. Now, findings from one log source can be used to trigger associated searches across other logs sources — enabling proactive threat hunting and investigations.
“With Falcon LTR, we were able to save approximately $150,000 in the first year. Also, the ability to save data for an extended time period is critical. When we detect an indicator of compromise, we can go back in time and analyze the entire attack chain to accelerate investigations and pinpoint issues more quickly.” —Tom Sipes, Director of IT Security and Compliance, Tuesday Morning
How does Falcon LTR work?
Falcon LTR allows customers to bring in data using the CrowdStrike Data Connector. This process makes it easy for data to flow from the CrowdStrike Threat Graph into Falcon LTR. The entire process is configured during provisioning of Falcon LTR and does not require any effort from the customer.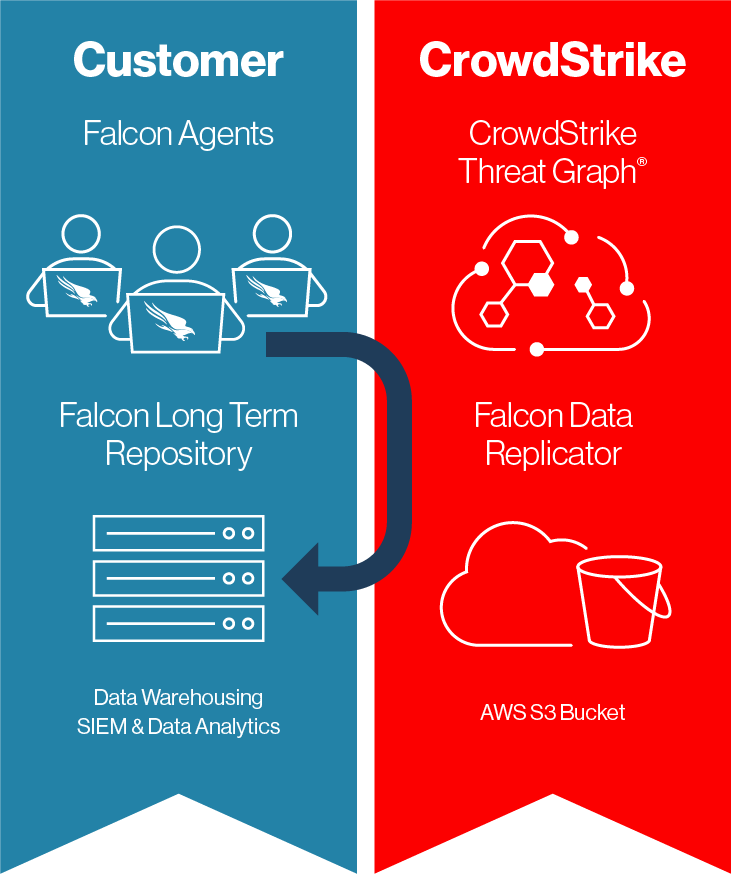 Note: Customers using self-hosted deployments of Falcon LTR must use Falcon Data Replicator instead of the CrowdStrike Data Connector to bring data into the platform.
Note: Customers using self-hosted deployments of Falcon LTR must use Falcon Data Replicator instead of the CrowdStrike Data Connector to bring data into the platform.
How do I get Falcon LTR?
To learn more about Falcon LTR capabilities and licensing, reach out to your CrowdStrike account manager. If you enjoyed this post, don’t miss the next two in the series, “Improve Threat Hunts with Long-Term, Cost-Effective Data Retention” and “The Force Multiplier of Correlating Your Security Telemetry.”Additional Resources
- Read Part 2 and Part 3 in this Falcon LTR blog series.
- Read the Falcon Long Term Repository press release.
- Read the Falcon Data Replicator data sheet.
- Stream the on-demand webinar Maximize the Value of Your Falcon Data with Humio.
- Discover the Total Economic Impact™ of Humio, a CrowdStrike Company.



?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)


![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)












































