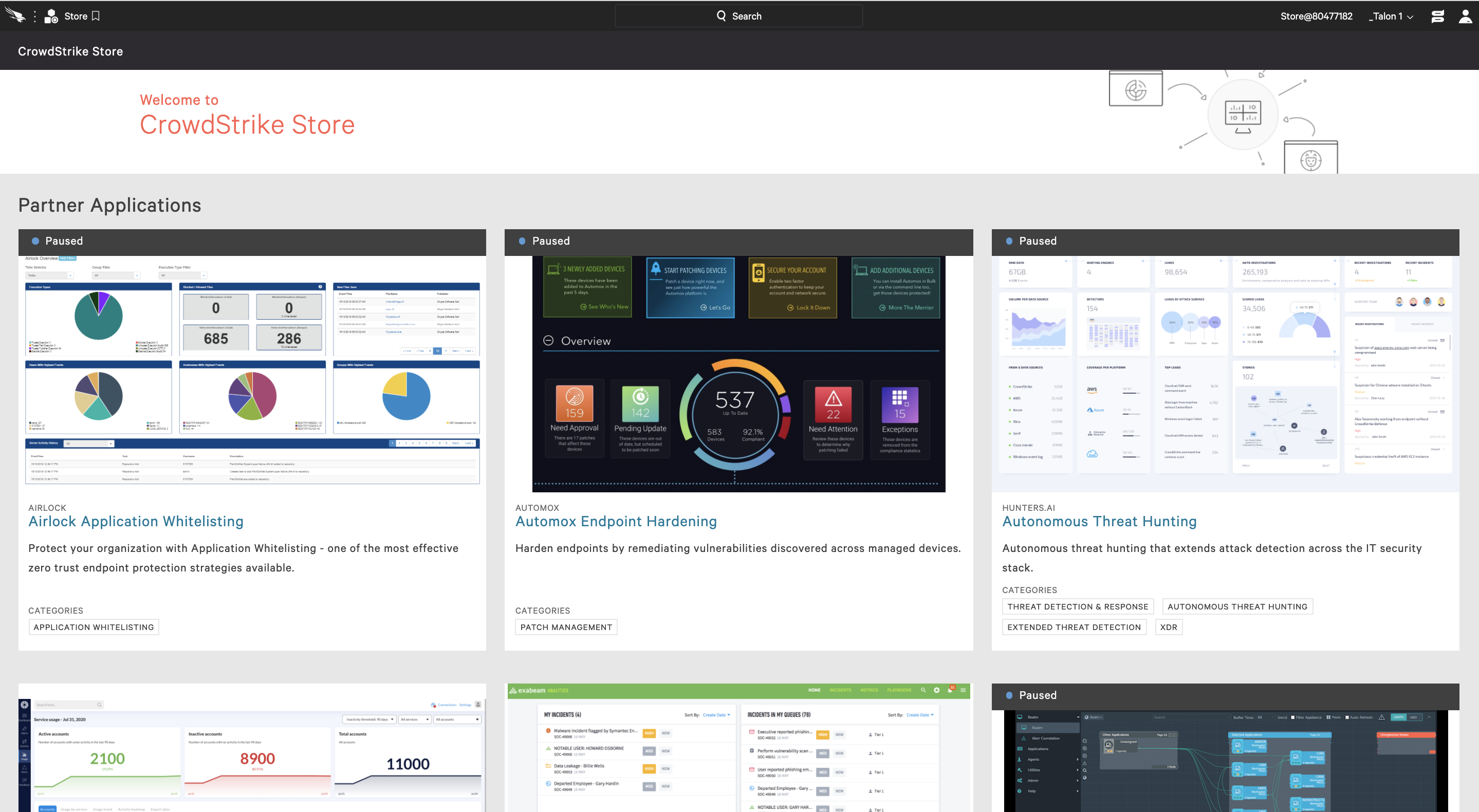
CrowdStrike continues to deliver a variety of innovative solutions from trusted technology partners, and we’ve just added three new applications from Illumio, Obsidian and SecurityAdvisor. These applications deliver diverse business-critical solutions, extend the customer’s existing investment in the CrowdStrike Falcon®® platform and demonstrate the robust capabilities of the CrowdStrike® Store, which is continually expanding its ecosystem of partners and the security use cases it serves. The apps include an endpoint segmentation solution to stop malware and ransomware propagation; security visibility for software-as-a-service (SaaS) applications; and personalized contextual security awareness training.New CrowdStrike Store Apps Secure Hybrid Workforces
The impact of the ongoing global pandemic, which has resulted in organizations having to quickly transition their employees to working remotely, has not deterred cyber adversaries — in fact, it has emboldened them. CrowdStrike has observed both nation-state and eCrime actors launching phishing campaigns that use pandemic-based lures to deliver ransomware and other threats. As organizations transition to hybrid models — some workers in an office and some at home — we expect to see adversaries continue to leverage this crisis to their advantage. These new CrowdStrike Store apps provide use cases that solve specific issues for organizations and strengthen their security postures. The following offers details on these apps:
Use Case: Blocking Lateral Movement
With the 2020 CrowdStrike Global Threat Report breakout times as a backdrop, we can see how global attacks such as WannaCry and Not Petya target a Server Message Block (SMB) vulnerability to spread among endpoints. (Breakout time is the time it takes for an intruder to begin moving laterally outside of the initial beachhead to other systems in the network.) Another infamous malware, TrickBot, also exploits SMB to propagate and drop ransomware such as Ryuk. Note that SMB lets endpoints in the same network connect directly and share files.Use Case: Unified Visibility and Security for SaaS Apps
SaaS adoption continues to show tremendous growth, and in many categories it has already surpassed on-premises deployment options. While SaaS delivers exceptional business value, security teams are struggling to make sure they are able to safely enable the use of SaaS across their hybrid workforces without compromising business productivity. Each SaaS application comes with a unique set of security configurations and controls that make it hard for security teams to ensure that all of these applications have been set up without exposing data, credentials and sensitive user information. In addition, security teams require consolidated, continuous visibility into what users have access to and what they are doing in SaaS applications and endpoints.Use Case: Contextual and Personalized Cybersecurity Awareness
Studies by IBM, Computer Weekly and Kroll report that 75% to 95% of security breaches and incidents can be traced back to human actions. Yet, when it comes to fortifying humans, the primary tools that CISOs use today are periodic training for their employees and email-based phishing assessments. The main challenges with this approach are:The CrowdStrike Store
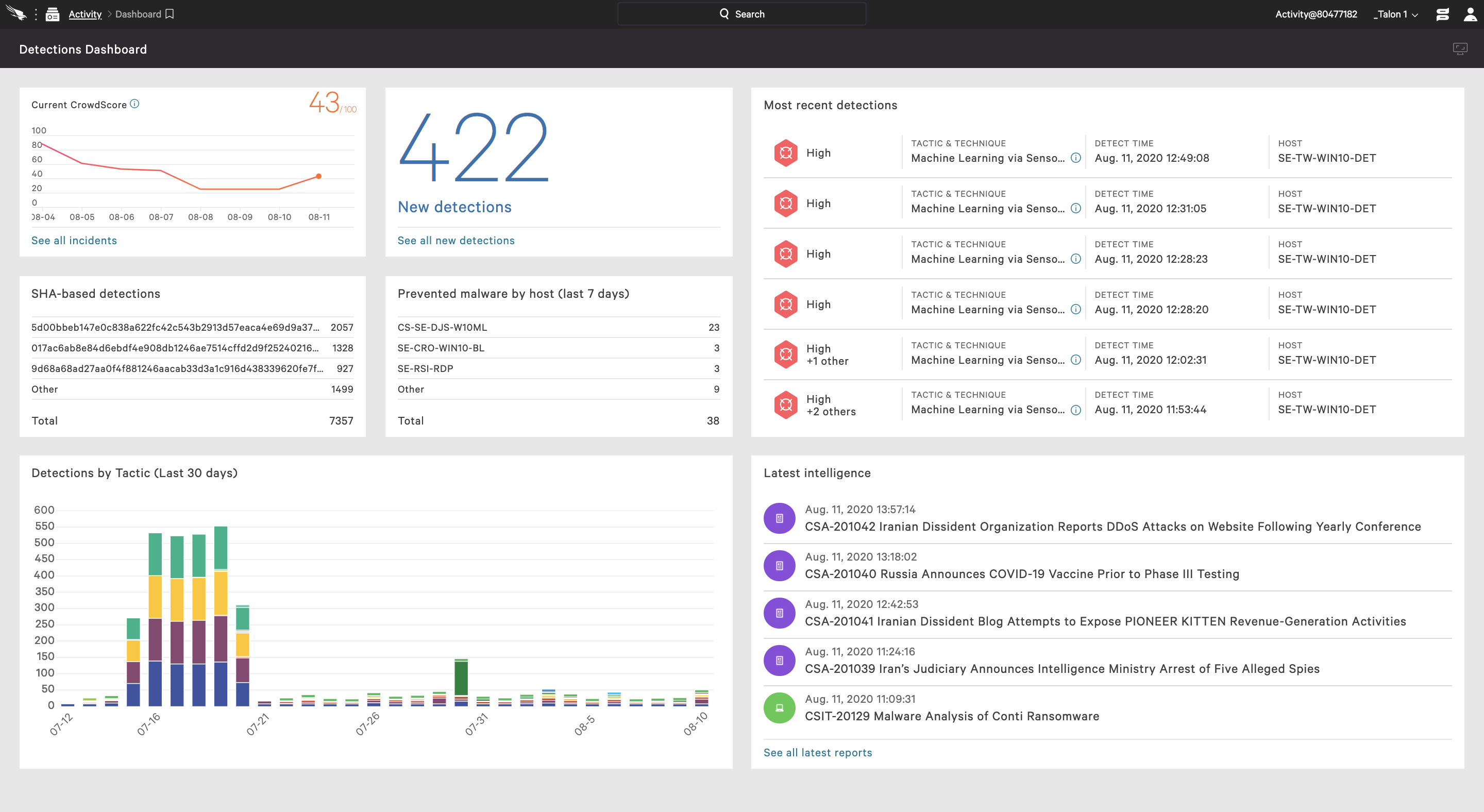
The CrowdStrike Store provides a strategic choice of vendors and security technologies to our customers, managed through a single cloud platform. All CrowdStrike Store applications leverage our powerful lightweight agent that provides rich endpoint telemetry to the Falcon cloud-native platform. The CrowdStrike Store is focused on delivering a frictionless consumption of curated third-party applications for our customers, leveraging the power of our extensible platform architecture and rich threat intelligence data.
New CrowdStrike Store Apps Secure Hybrid Workforces
The impact of the ongoing global pandemic, which has resulted in organizations having to quickly transition their employees to working remotely, has not deterred cyber adversaries — in fact, it has emboldened them. CrowdStrike has observed both nation-state and eCrime actors launching phishing campaigns that use pandemic-based lures to deliver ransomware and other threats. As organizations transition to hybrid models — some workers in an office and some at home — we expect to see adversaries continue to leverage this crisis to their advantage. These new CrowdStrike Store apps provide use cases that solve specific issues for organizations and strengthen their security postures. The following offers details on these apps:
Use Case: Blocking Lateral Movement
With the 2020 CrowdStrike Global Threat Report breakout times as a backdrop, we can see how global attacks such as WannaCry and Not Petya target a Server Message Block (SMB) vulnerability to spread among endpoints. (Breakout time is the time it takes for an intruder to begin moving laterally outside of the initial beachhead to other systems in the network.) Another infamous malware, TrickBot, also exploits SMB to propagate and drop ransomware such as Ryuk. Note that SMB lets endpoints in the same network connect directly and share files.Often we see attackers take more time with targeted attacks that move laterally as they "live off the land"
and target critical assets.
The attackers behind Maze exploited Remote Desktop Protocol
(RDP) as part of their lateral movement. Lateral movement is what can make an isolated incident on a single endpoint turn into a large-scale
attack, particularly if new ransomware has yet to be detected. Stopping an attacker’s lateral movement has become fundamental to a defender’s job to such an extent that it is a key attacker technique laid out in the MITRE ATT&CK® framework.
Illumio Edge for CrowdStrike stops ransomware propagation and attacker lateral movement by segmenting every endpoint so they gain threat containment by default, for an even stronger enterprise security posture. This ensures that if an incident occurs, the first compromised endpoint is the last compromised endpoint. This capability is delivered seamlessly through the Falcon agent with nothing additional to deploy. Illumio Edge arms endpoints with a default deny/allowlist security posture that blocks all inbound endpoint communications, except the essential traffic needed for business. This vastly reduces the risk of ransomware or other malware spreading laterally between endpoints. This is attack surface reduction in its truest sense, bringing complete endpoint segmentation with Illumio’s easy policy creation that perfectly threads the needle between preventing lateral movement and maintaining business productivity.
Use Case: Unified Visibility and Security for SaaS Apps
SaaS adoption continues to show tremendous growth, and in many categories it has already surpassed on-premises deployment options. While SaaS delivers exceptional business value, security teams are struggling to make sure they are able to safely enable the use of SaaS across their hybrid workforces without compromising business productivity. Each SaaS application comes with a unique set of security configurations and controls that make it hard for security teams to ensure that all of these applications have been set up without exposing data, credentials and sensitive user information. In addition, security teams require consolidated, continuous visibility into what users have access to and what they are doing in SaaS applications and endpoints.Obsidian delivers the industry’s first cloud detection and response (CDR) solution. The Obsidian solution integrates with the Falcon platform to deliver frictionless security for SaaS applications and endpoints. This integration helps security teams uncover, investigate and respond to breaches and insider threats quickly, without slowing down business operations. Security teams can seamlessly receive data about user access, privileges and activity in SaaS applications, and correlate that with rich endpoint telemetry from CrowdStrike endpoints for increased visibility and protection.
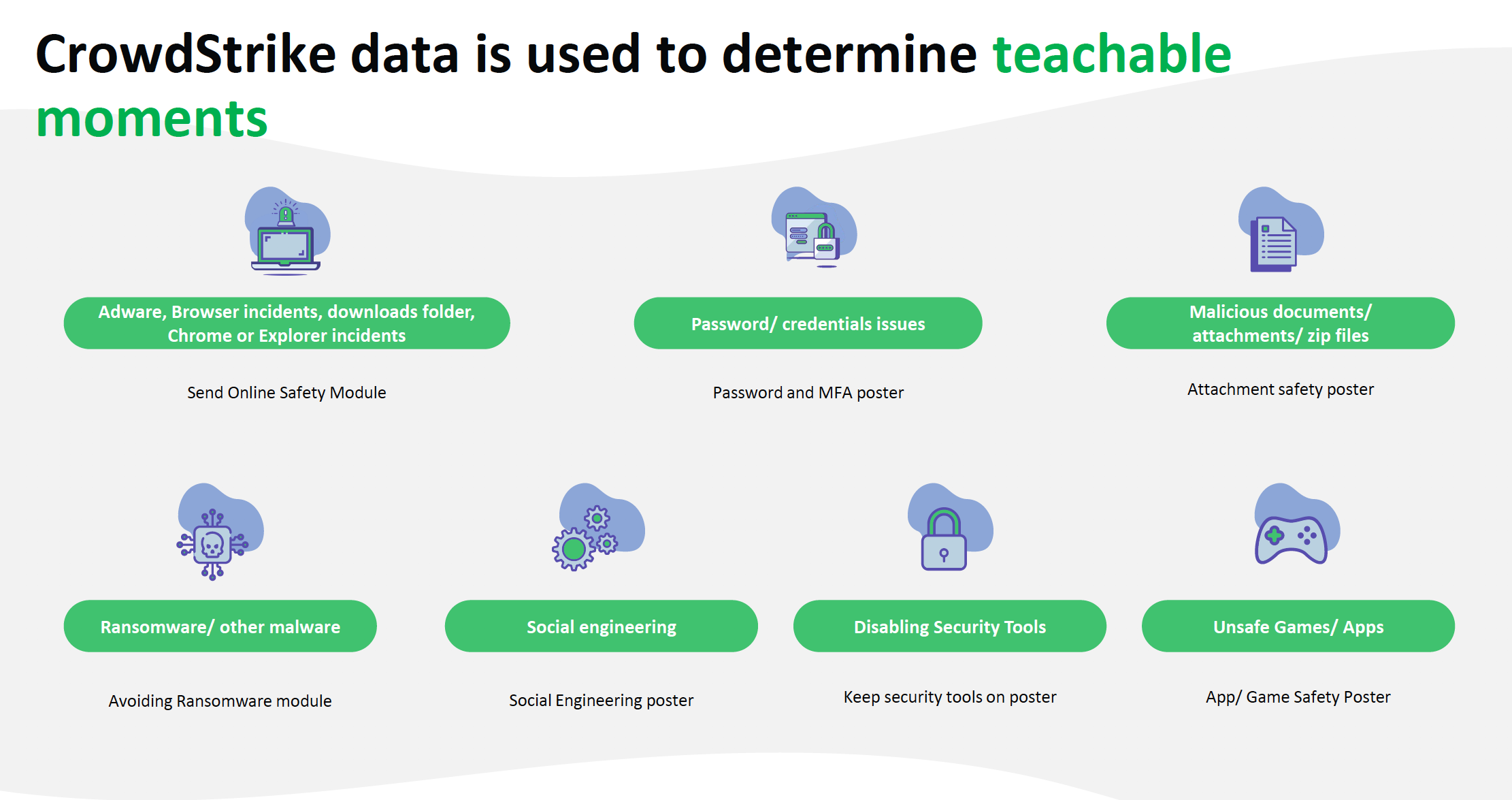
Use Case: Contextual and Personalized Cybersecurity Awareness
Studies by IBM, Computer Weekly and Kroll report that 75% to 95% of security breaches and incidents can be traced back to human actions. Yet, when it comes to fortifying humans, the primary tools that CISOs use today are periodic training for their employees and email-based phishing assessments. The main challenges with this approach are:
- Employees are bombarded with different types of training, and security awareness training is yet another chore for them to complete. Most employees do not pay attention, even if the content is great.
- There is no measurable ROI for CISOs from periodic security awareness training, other than fulfilling a compliance mandate.
- Each employee has a different risk profile depending on behavior, role, geography, etc. One set of generic security awareness modules sent to all employees does not address the learning needs of each individual employee.
The CrowdStrike Store
The CrowdStrike Store provides a strategic choice of vendors and security technologies to our customers, managed through a single cloud platform. All CrowdStrike Store applications leverage our powerful lightweight agent that provides rich endpoint telemetry to the Falcon cloud-native platform. The CrowdStrike Store is focused on delivering a frictionless consumption of curated third-party applications for our customers, leveraging the power of our extensible platform architecture and rich threat intelligence data.
Visit the CrowdStrike Store Via the Falcon UI
If you are a CrowdStrike customer, please visit the CrowdStrike Store via your Falcon console by clicking on the menu as shown above.Learn more about the new partner apps and how they can solve and simplify your specific security challenges. The CrowdStrike Store provides auto-provisioning of in-app trials to allow you to easily deploy and try an app before investing.
Additional Resources
- Read the CrowdStrike Store Momentum press release.
- Learn more about the CrowdStrike Store by visiting the webpage.
- Visit CrowdStrike Store Partner page if you are interested in becoming a CrowdStrike Store partner.
- Learn more about the powerful CrowdStrike Falcon® platform by visiting the webpage.
- Test CrowdStrike next-gen AV for yourself. Start your free trial of Falcon Prevent™ today.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)