“I’m drowning in data, but starving for information.” Ever feel that way? Recently, I heard a CISO use this as a description of his company’s information security posture. Today, enterprises are littered with data collection sensors and data aggregation systems, creating an unrelenting deluge of non-contextual indicators. Somewhere in this jumble of alerts and indicators are gold nuggets, the kind of nuggets that make the difference between being the frazzled poster child for the latest breach, and hearing about it on the news while eating dinner at home with your family. Increasingly, the key to unlocking these gold nuggets to sort the proverbial wheat from the chaff is actionable threat intelligence.
Operationalizing threat intelligence is one of the first and greatest challenges organizations face when deciding to embrace an intelligence-driven security model. There are myriad formats that threat intelligence may come in, and many of the enterprise products used today have proprietary formats for ingesting and consuming externally sourced data. While whole volumes can be written on suggested methodologies or strategies for incorporating threat intelligence, there are some really great products out there today that make utilization of threat intelligence a breeze.
Data visualization is a powerful tool for conducting investigations or hunting for anomalous activity. Our friends at Paterva have a product used by many information security professionals today. Their data visualization and charting software Maltego has utility in everything from Penetration Testing to Incident Response. The CrowdStrike Intelligence team uses Maltego to map out complex relationships as well as to incorporate data from disparate sources into our investigations. Existing Maltego Chlorine users can access Falcon Intelligence data to perform attribution on 70+ adversary groups, to include nation-state, hacktivist, activist, and criminal threat actors.
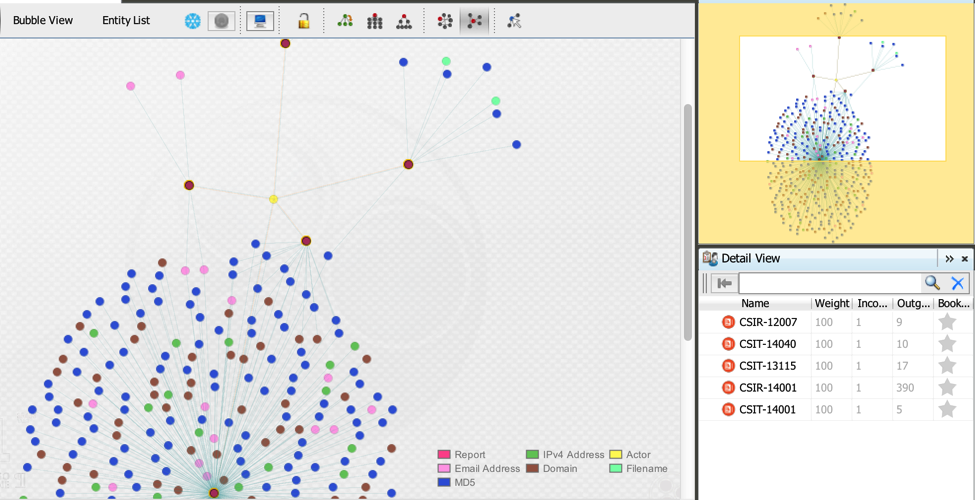 Use Maltego to visualize and pivot into detailed indicators of compromise related to threat actors targeting an organization.
Use Maltego to visualize and pivot into detailed indicators of compromise related to threat actors targeting an organization.For additional information on how to access CrowdStrike Falcon® Intelligence using Maltego, please contact: sales@crowdstrike.com.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)







































