- CrowdStrike is a Research Partner with the MITRE Engenuity Center for Threat-Informed Defense and actively participates in the Center’s research into proactive cybersecurity defense
- As a global leader in threat intelligence, CrowdStrike provided expertise in adversarial tradecraft for the Summiting the Pyramid project
- The Summiting the Pyramid project was launched in order to “change the game on the adversary” by enabling cybersecurity defenders to write more robust analytics that are more difficult for adversaries to evade
The MITRE ATT&CK® framework is a foundational resource that is invaluable for helping organizations to defend against adversarial cyberattacks. ATT&CK is a knowledge base that models cyber adversaries' tactics and techniques, providing a common language for describing adversarial behaviors — and then shows how to detect or stop them. ATT&CK is also a critical resource for advancing research across the threat landscape.
One of the challenges faced by users of the MITRE ATT&CK framework is the “brittleness” of many of the analytics that are labeled with an ATT&CK technique. These analytics are dependent on specific tools, artifacts or TTPs (tactics, techniques and procedures). This reliance makes it too easy for adversaries to evade detection by an analytic.
The goal of the MITRE Engenuity Center for Threat-Informed Defense’s Summiting the Pyramid project is to make defenders’ analytics more robust — in other words, make it much more difficult for an adversary to evade the analytics. More robust analytics give defenders an immediate advantage and also make it easier to detect adversaries as they evolve, providing protection against future cyberattack campaigns.
The “Pyramid of Pain” model used by the Center categorizes observables based on how difficult it would be for an adversary to evade an analytic based on that observable, or how much pain each detection causes to an adversary. In this model, IOC (indicator of compromise) hash values are at the base of the pyramid, as they are considered trivial for adversaries to evade. At the top of the pyramid are TTPs, which are much more difficult.
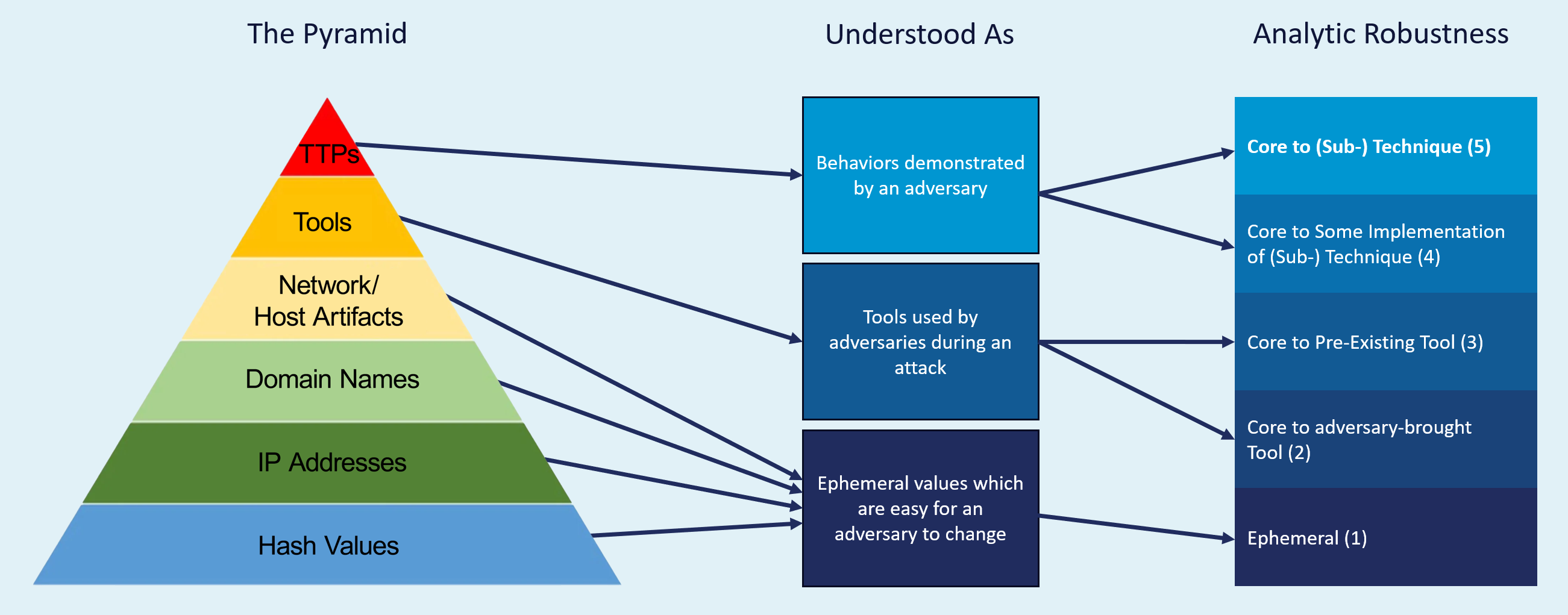 Figure 1. The “Pyramid of Pain” model for the Summiting the Pyramid project (Source: The MITRE Engenuity Center for Threat-Informed Defense)
Figure 1. The “Pyramid of Pain” model for the Summiting the Pyramid project (Source: The MITRE Engenuity Center for Threat-Informed Defense)CrowdStrike has embraced ATT&CK in the Falcon® platform and security operations. The CrowdStrike Counter Adversary Operations team annotates its curated intelligence with ATT&CK tactics and techniques to streamline operationalization of its threat intelligence, and we see significant value in making detections and analytics more robust.
Maximizing cost to adversaries is central to CrowdStrike’s detection engineering across the powerful, integrated CrowdStrike Falcon platform, which fortifies existing defenses, generates detections faster than adversaries can keep pace with and proactively delivers protection against emerging threats.
CrowdStrike is a Research Partner in the MITRE Engenuity Center for Threat-Informed Defense and actively participated in the Summiting the Pyramid project, lending industry-leading expertise in threat intelligence and detection engineering. The goals of the project were to:
- Define the components of analytics that make them more (or less) robust
- Publish best-practice guidance on how to evaluate and improve analytic robustness, enabling defenders to write more robust analytics
- Test online analytics and score them against the methodology introduced by the project
- Provide a corpus of examples
Key to the success of the Summiting the Pyramid project was the creation of organized tables of observables for both Analytic Robustness and Sensor Robustness categories. An observable is defined as an event (benign or malicious) generated on a network or system that is visible to a defender — it’s a key component of the analytic.
What Summiting the Pyramid Accomplished
When the Summiting the Pyramid project was complete, the team had delivered meaningful accomplishments that will have a positive impact in the cybersecurity industry. Through analysis of Sigma analytics and supporting research, they had leveraged Sigma rules as a basis for showcasing the Pyramid of Pain against a public analytics repository as a way of demonstrating its value. The creation of a best-practices guide is arguably even more important, as it provides the guidance that will help the industry to move forward.
The team scored and placed over 50 analytics from the public Sigma rules repository, leveraging the Sigma rules to showcase the Pyramid of Pain against publicly accessible analytics as a way of demonstrating its value. They improved four analytics based on observables placed in a robustness table (and submitted to Sigma) and created an additional three analytics to be submitted to Sigma. ATT&CK technique data scoring was improved with observables grouped based on technique for detection. In addition, new technique scoring was developed for Scheduled Tasks and LSASS Memory.
Ultimately, this project demonstrated that, by better organizing how observables are generated and capturing how an adversary might evade a specific observable, it is possible to gain a better understanding of an adversary’s goal — which is a critical piece of information. This methodology is not just applicable to cybersecurity companies. By employing the methods explored in the Summiting the Pyramid project, corporate SOC analysts are also able to develop robust analytics based around custom indicators of attack (IOAs) that are unique to their business.
The initial Summiting the Pyramid project is a success. The Center is planning a followup project to further refine the outcome through enhanced analytic precision (minimizing false positives while retaining robustness) and other improvements.
Summiting the Pyramid is the Latest Example of CrowdStrike’s Commitment to Cybersecurity Innovation
As a Research Partner with the MITRE Engenuity Center for Threat-Informed Defense, CrowdStrike is a firm supporter of the Center’s mission to advance state-of-the-art threat-informed defense globally. CrowdStrike researchers never rest in their efforts to ensure that we always remain a step ahead of the most sophisticated and determined adversaries. The best-in-class protection customers gain from the Falcon platform is the culmination of CrowdStrike’s relentless commitment to cybersecurity innovation.
In addition to advancing the Falcon platform, CrowdStrike researchers also publicly publish many of their findings to advance cyber defenses against newly discovered tactics and malware and make the world safer. In addition, publishing cutting-edge research helps drive development of testing and evaluation tools that cover the most recently identified cybersecurity threats.
Additional Resources
- Join us at Fal.Con 2023, the can’t-miss cybersecurity experience of the year. Register now and meet us in Las Vegas, Sept. 18-21!
- Learn how you can stop cloud breaches with CrowdStrike unified cloud security for multi-cloud and hybrid environments — all in one lightweight platform.
- Read about adversaries tracked by CrowdStrike in the CrowdStrike 2023 Global Threat report.
- Test CrowdStrike next-gen AV for yourself. Start your free trial of Falcon Prevent™ today.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)







































