Cloud Workload Protection: 5 Key Take-Aways
- Cloud Workload Protection (CWP) continuously monitors and removes threats from cloud workloads like VMs, containers, and serverless functions.
- A Cloud Workload Protection Platform (CWPP) offers unified, real‑time threat detection across modern cloud environments, including hybrid, multi‑cloud, and on‑premise.
- Modern CWPPs deliver runtime visibility, AI-driven threat detection, and native DevSecOps integration across multi-cloud workloads and containerized environments.
- CWPP differentiators include in‑depth workload visibility, automated detection and response capabilities, and continuous security across CI/CD pipelines without slowing DevOps workflows.
- Cloud workload protection adoption is rising due to increased cloud-native complexity, compliance demands, and evolving runtime threats.
What is cloud workload protection (CWP)?
Cloud Workload Protection (CWP) is the process of continuously monitoring for, and removing threats from cloud workloads and containers. A Cloud Workload Protection Platform (CWPP) is a security solution that protects workloads of all types in any location, offering unified cloud workload protection across multiple providers.
Why is CWP important?
Cloud adoption remains a key driver for digital transformation and growth for today's businesses, helping them deliver applications and services to customers with the speed and scalability that only the cloud can provide. However, protecting the cloud means securing an increasingly large attack surface that ranges from cloud workloads to the virtual servers and other technologies that underpin your cloud environment.
Cloud workload protection is important because it offers breach protection for workloads, containers, and Kubernetes while enabling organizations to continue to build, run, and secure cloud applications with speed and confidence.

The Complete Guide to CNAPPs
Download CrowdStrike's Complete Guide to CNAPPs to understand why Cloud-Native Application Protection Platforms are a critical component of modern cloud security strategies and how to best integrate them to development lifecycles.
Download NowWhat are the benfits of cloud workload protection?
- Visibility: CWP provides complete visibility into workload and container events to ensure that nothing goes unseen in your cloud environment, enabling faster and more accurate detection, response, threat hunting and investigation.
- Protection: CWP secures your entire cloud-native stack, on any cloud, across all workloads, containers and Kubernetes applications. A cloud workload protection platform will automate security and detect and stop suspicious activity.
- Frictionless: A CWPP should support continuous integration/continuous delivery (CI/CD) workflows allowing you to secure workloads at the speed of DevOps without sacrificing performance.
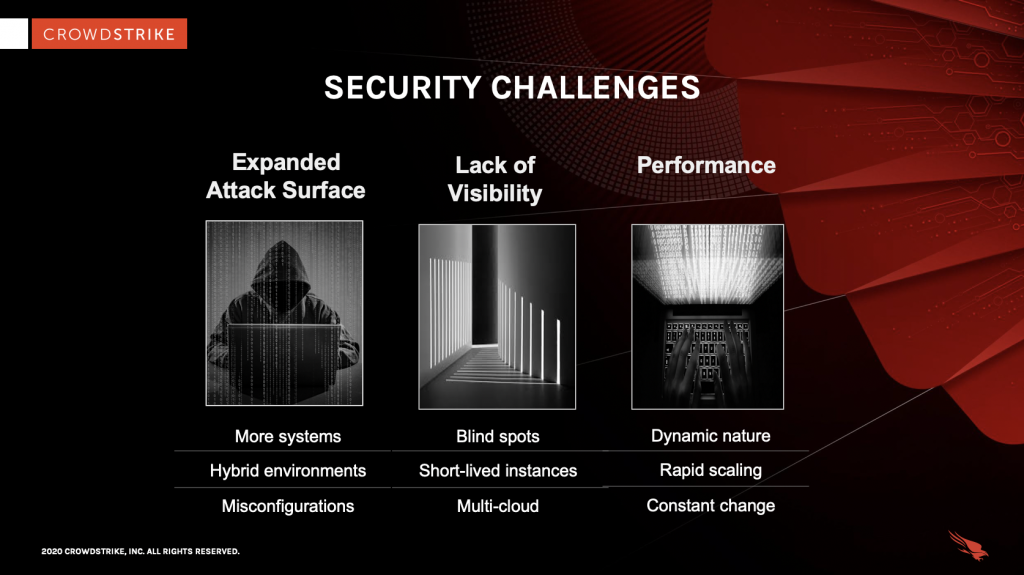
What are cloud workload security challenges?
Cloud computing requires security measures from customers and providers alike since public cloud deployments operate under a shared security model. Both the cloud computing provider and the customer have a responsibility to ensure the security within their area of control.
In general, the provider is responsible for security of the cloud. That includes physical access and infrastructure.
In turn, the customer is responsible for security in the cloud. That includes their applications, identity management, data and encryption. The unique characteristics and capabilities of the cloud introduce new security challenges for customers as they migrate their workloads:
1. Expanded Attack Surface
Having more systems and instances distributed to various off-premises locations means more risk and an expanded attack surface. It is no longer just about protecting physical data centers and servers. Having a cloud presence means the additional responsibility of securing virtual servers, remote applications, cloud workloads, containers and the network communications between the environments. There is also the issue of having more users with different levels of security expertise but the same ability to create and use cloud workloads.
2. Visibility
Blind spots lead to silent failure and ultimately breaches. Cloud workloads are challenging in terms of visibility for a number of reasons. First, traditional security tools are not designed to provide granular visibility. For example, tools such as Linux logs make it difficult to uniquely identify events generated by containers versus those generated by the host, since visibility is limited to the host. Then, containers present additional visibility challenges because they are short-lived, making data collection and incident investigation difficult because forensic evidence is lost when a container is terminated. And, container portability creates even more challenges — deployment across cloud environments results in decentralized container controls that limit overall visibility.
3. Performance
Because of the dynamic nature of cloud workloads, and specifically containers, traditional solutions and manual processes no longer suffice. Rapid deployment and scaling mean the attack surface is constantly changing, and security solutions need to match the speed of DevOps without sacrificing performance.

Customer Story: CoreWeave
CoreWeave is a specialized cloud providor who needed protection from endpoint to cloud workload. Learn how CrowdStrike's Falcon platform met their needs with zero impact to their high-performance cloud.
Download NowWhat are key requirements of a cloud workload protection platform?
With the above challenges in mind, it is imperative that cloud workload security solutions deliver in these key areas:
Runtime Protection
Image scanning, while important, is blind to attacks. Vulnerabilities can be exploited before they can be patched. Misconfigurations can happen. Once a virtual machine or container is launched, even if the image is configured properly and verified, it can be compromised. Comprehensive runtime protection is required to secure containers and the hosts they run on.
Visibility
You can’t detect, stop or respond to something if you can’t see it. Workload events, including container events, need to be captured, analyzed and stored so that security products and teams alike have the visibility they need to detect and stop threats as they happen, as well as to hunt and investigate.
Simplicity and Performance
Companies need to address the security requirements of the cloud without increasing the number of products they deploy and manage. Ideally, companies could use the same platform for their on-premises and public, private and hybrid cloud needs to help provide consistent, low-impact security without adding complexity.
With cloud workloads, it is even more important for a solution to deliver protection while having minimal performance impact on systems, teams and workflows. DevOps requires speed, and delays and inconvenience can lead to hazardous behaviors, from weak passwords to the use of untrusted images.
CrowdStrike Falcon® Platform: Built in the Cloud to Protect the Cloud
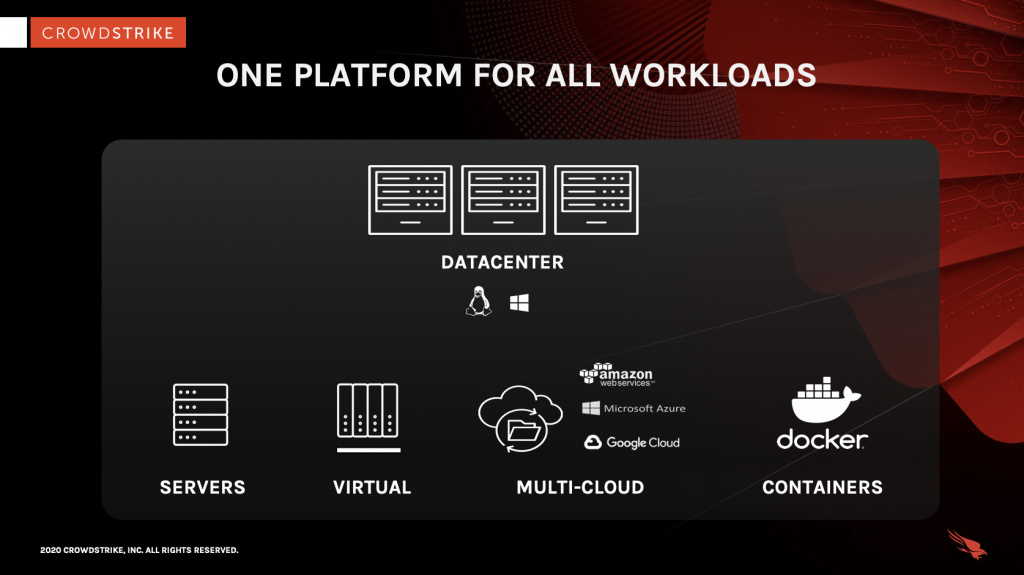
CrowdStrike sets the new standard in cloud workload protection by bringing the award-winning CrowdStrike Falcon® breach protection capabilities to cloud workloads, including virtualized workloads and containers in private, public and hybrid clouds. Falcon unifies and simplifies cloud workload security with one platform for all workloads.
Runtime protection for cloud workloads and containers: The Falcon platform combines the best and latest technologies to protect cloud workloads and containers against known and unknown malware and sophisticated attacks.
EDR for cloud workloads and containers: The Falcon platform offers full endpoint detection and response (EDR) for cloud workloads and containers, providing continuous and comprehensive visibility to enable proactive threat hunting and forensic investigation. You can distinguish activity within a container from activity on a host, and view event details and a full set of enriched data, even for ephemeral and decommissioned workloads.
Performance: The Falcon platform secures workloads at the speed of DevOps, providing immediate protection and adapting to the dynamic scalability of containers in real time without sacrificing performance. A single agent secures the host and containers and automatically applies protection as they spin up and then scales as they expand.
Simplicity: The Falcon platform was built in the cloud for the cloud. One platform secures all workloads, wherever they run, without added complexity and overhead. One console provides central visibility over cloud workloads, regardless of their location.
Cloud Workload Protection FAQs
Q: What is Cloud Workload Protection (CWP)?
A: CWP is a security approach that continuously monitors and neutralizes threats across cloud workloads, such as VMs, containers, and serverless environments.
Q: What is a CWPP and why is it important?
A: A CWPP is a unified platform that delivers continuous threat monitoring and protection for workloads across hybrid and multi‑cloud environments. It streamlines security across diverse infrastructures.
Q: What does CrowdStrike Falcon CWP offer?
A: Falcon CWP provides runtime protection, AI-driven threat detection, full visibility, and seamless DevSecOps integration across workloads, containers, Kubernetes, and serverless architectures.
Q: How does CWPP support CI/CD and DevOps workflows?
A: CWPPs integrate with CI/CD pipelines, enabling shift‑left security and protecting workloads at DevOps speed without compromising performance or scalability.
Q: What trends are driving CWP adoption?
A: Factors like cloud migration, complex runtime threats, regulatory compliance, and scalability concerns are increasing demand. AI capabilities and micro‑segmentation further fuel adoption.





