If you think your small business is not a target for hackers and cybercriminals — think again. A 2023 ITRC report states that 73% of small business owners reported experiencing a cyber attack in the last 12 months, likely because adversaries believe smaller organizations do not have robust security measures in place to defend the business and its data.
While cybercriminals rely on a variety of methods to attack a company, one of the most common — and often easiest — is by targeting employees through coordinated phishing attacks or other social engineering techniques.
To minimize this risk, small- and medium-sized businesses need to develop an employee cybersecurity training program that will educate their people about common security risks, promote responsible online behavior and outline steps to take when they believe an attack may be in progress.
Understanding Internal Cybersecurity Policies
Before employee training programs can be developed, your business must have a clear sense of its cybersecurity strategy, as well as the people, processes and technologies that will execute the security program. Here we review the essential elements of the cybersecurity architecture.
Are you using a cybersecurity platform?
A wide variety of solutions and services are available on today’s cybersecurity market. While a trusted and reputable cybersecurity partner can help businesses develop a custom toolset to meet their unique needs, every cybersecurity platform should start at a baseline with antivirus protection.
Expert Tip
While cost is a concern for many small business owners, it is important to find solutions that provide the right level of protection at the right budget with the right technology. Learn how to start building a robust cybersecurity plan to meet the specific needs of small businesses.
Download: Cybersecurity for Small Businesses: Proactive solutions that meet your need
Develop an Incident Response Plan and Document Cybersecurity Procedures
An incident response plan is a document that outlines an organization’s procedures, steps and responsibilities to prepare for, detect, contain and recover from a data breach.
Document the Software, Programs and Internet Sources that Are Allowlisted for the Organization
Even small businesses should develop a clear acceptable use policy for employees who use corporate devices and networks, or have access to data and other sensitive assets. This would include listing the different software applications, programs, websites and social media platforms that are allowed to be accessed with a company device or via a corporate network, as well as the steps that need to be taken to secure and protect the device and its data.
As part of this process, it may also be helpful to outline unacceptable behaviors and prohibited activity.
Learn More
EXAMPLE: A company’s IT policy should make clear that employees are not allowed to install unlicensed software on any company computer, phone or other device or to download files or programs, such as music, movies, games or other applications. This is because unlicensed software downloads, or any file download, could make the company susceptible to cyberattacks.
Define Scope of the Cybersecurity Training Program
Cybersecurity awareness training should be a mandatory task completed by every employee, regardless of level, location or job scope. That said, it may be wise to tailor learning programs based on job type or level of experience, as well as location.
The training program may be adapted for the following audiences:
- Basic/individual contributor: A basic level of cybersecurity training suitable for all employees who have access to any internet-connected device or the company network. This course would review common cyber threats, how to detect attacks that are in progress and how to engage in responsible online behavior to reduce risk.
- Managerial: A managerial training module is specifically designed to help managers and supervisors answer questions from their teams, enforce corporate security policies, identify and mitigate high-risk behaviors and coordinate with the security team.
- IT staff: While IT staff are highly trained in technical matters, many do not have deep expertise in cybersecurity. This training module would provide IT professionals with a high-level overview of cybersecurity best practices and training on how to use the company’s existing cybersecurity tool set.
- Remote workers: As the remote work trend continues to grow, organizations must take extra steps to protect the company from risks that occur when an employee uses a personal network to conduct official business. As part of this process, the organization must outline what security measures must be in place for the employee to work from a remote location — whether it is their home, a partner site, a hotel or any location of their choosing.
- Contractors, freelancers, vendors: Similar to remote workers, contractors, freelancers and vendors often do not work onsite but have access to corporate devices, data and networks. These individuals should complete the basic cybersecurity training program. In addition, the company can also consider developing a special module to address the specific needs and limitations of this group.
Planning Your Training Program: What Topics to Include
The training program should cover common and significant cyber threats. These include:
Phishing and Other Social Engineering Attacks
Social engineering is one of the most common methods of cyberattack, where a hacker tricks an employee into sharing sensitive data or credentials by posing as another legitimate employee or partner. For example, a hacker may pose as a help desk agent to ask a user for sensitive information, such as a username and password.
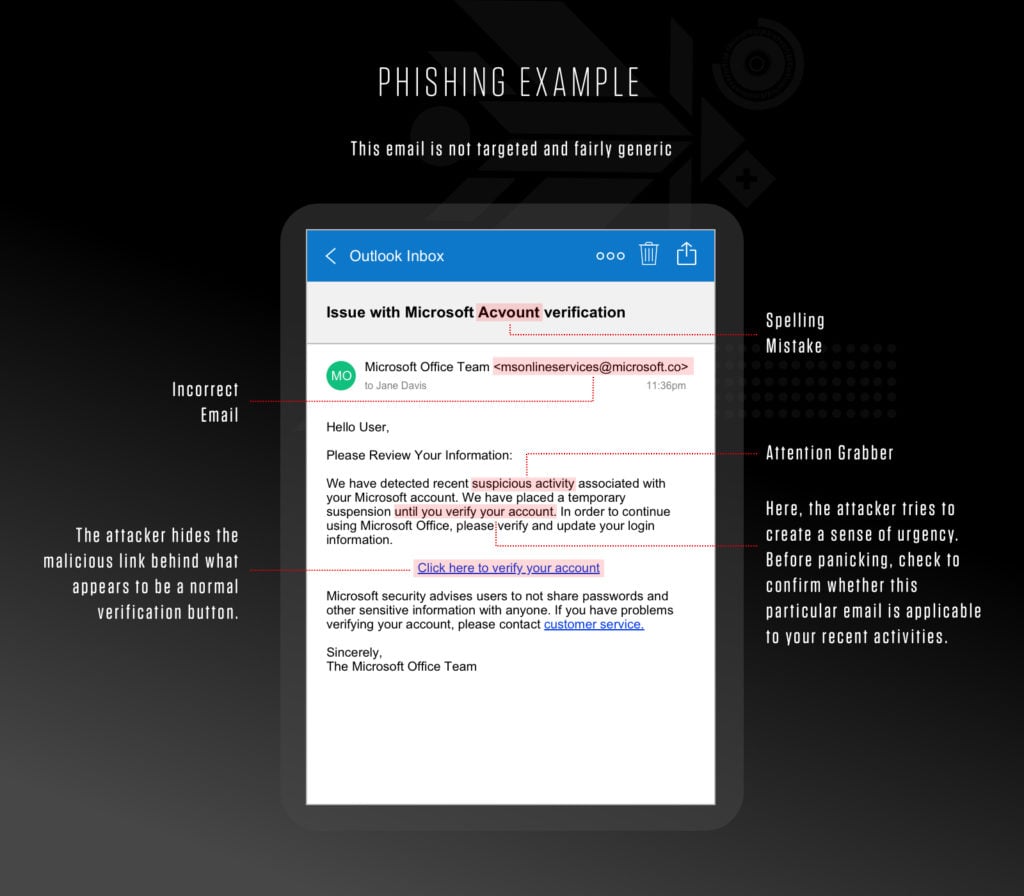
Phishing is a type of social engineering cyberattack that uses email, text message, phone call or social media to entice a victim to share sensitive information — such as passwords or account numbers — or to download a malicious file that will install viruses on their computer or phone.
When creating your training program, include real-life examples of a phishing attack to educate your employees on the main key indicators like you’ll see in the example below:
Password Attacks and Credential Theft
Attackers are constantly after user IDs, email addresses and passwords because these items enable them to pose as a legitimate user to avoid detection while they carry out an attack.
Once the hacker has your credentials they can access any service or network the account is entitled to. One of the best ways to reduce the risk of password compromise is to require users to create strong passwords. Below are examples of strong passwords.
Expert Tip
Strong passwords are:
- Complex: Comprised of 25 or more characters
- Random: Do not contain any recognizable words, phrases or patterns
- Changed frequently: Rotated every 30 days or less
Long, complex, random passwords are exponentially more difficult for password cracking tools to breach. In addition, frequently updated passwords limit the amount of time adversaries have available to crack password hashes.
Insider Threats
An insider threat is a cybersecurity risk that comes from within the organization. This is usually a current or former employee or other person who has direct access to the company network, sensitive data and intellectual property.
Typically an insider is financially motivated to lead or take part in a malicious act. These attacks usually involve theft of data or trade secrets which can be sold on the dark web or to a hostile third party. Luckily, there are ways to mitigate insider threats for SMBs, which include continuously monitoring your network and educating employees on all company policies regarding cybersecurity practices.
Protecting Mobile Devices
Every internet-connected device can be the entry point for an attack. Your cybersecurity training program should share best practices for how employees can keep their devices safe, as well as how to install and update the security tools used by the organization.
Social Media
Social media can be another avenue for cybercriminals to connect with employees, gather personal information and otherwise exploit personal relationships to advance an attack using social engineering techniques. While companies generally cannot prohibit employees from using social media on their own time using their own devices, they can construct clear policies that limit use on company devices or the corporate network.
Key Responsibilities of Employees
The main goal of every cybersecurity program is to keep the organization and its assets safe. This includes data of all kinds — including sensitive customer data and intellectual property.
In many cases, employees who handle sensitive customer data, such as personal information, bank details or health records, are required by law to complete cybersecurity training. Organizations that are subject to such regulations should ensure that the training program they develop meets the requirements dictated by government or industry groups.
Get Buy-In from Team Leaders
Cybersecurity must be seen as a company-wide effort. It is important the program has dedicated leadership from IT and HR to ensure training modules are properly developed and rolled out to the appropriate audiences.
As part of this process, the CEO, CFO, IT lead and HR manager should also coordinate on all aspects of program management, including budget. This will help ensure that cybersecurity remains an important part of the company’s ongoing operations and is supported with the proper resources and investments.
Roll Out, Measure, Ask for Feedback and Update
As with any new training program, it may be helpful to conduct an initial pilot of the program with a subset of employees and gather feedback about the program content and user experience.
When rolling out the program to your employees, it will be important to track completion rates and test knowledge through both a completion quiz and regular cybersecurity testing, such as a simulated phishing email.
All basic training should be conducted annually in order to refresh employees’ knowledge and keep best practices top-of-mind.
Next Steps with CrowdStrike
Don’t let the size of your business or your budget stand in the way of developing a strong security defense. CrowdStrike Falcon® Go is an easy-to-install, easy-to-use, and affordable solution that protects your small business from ransomware, malware and the latest cyber threats.
- Protect your business with the industry-leading, next-generation antivirus solution proven to stop advanced attacks.
- Leverage device control to help you monitor and govern USB devices that could put your network at risk.
- Deploy one lightweight sensor and start protecting your business instantly, no matter where your devices are.
Ready to try it free?
Start a free, 15-day trial of Falcon Go and protect your small business from ransomware, malware and sophisticated cyberattacks.





