Application developers have always had a tricky balance to maintain between speed and security, two requirements that may often feel at odds with each other. Practices that increase speed also pressure development teams to ensure that vulnerable code is identified and remediated without slowing development. As companies embrace digital transformation initiatives, the need to weave better security into developers’ workflows has only grown clearer.
 Source: “Walking the Line: GitOps and Shift Left Security,” Enterprise Strategy Group (ESG)
When asked what elements of the cloud-native application stack they feel are most susceptible to compromise and therefore represent the greatest risk, respondents most often selected APIs followed by data storage repositories and internally developed application source code.
Source: “Walking the Line: GitOps and Shift Left Security,” Enterprise Strategy Group (ESG)
When asked what elements of the cloud-native application stack they feel are most susceptible to compromise and therefore represent the greatest risk, respondents most often selected APIs followed by data storage repositories and internally developed application source code.The Impact of Shift Left Security
Shifting security left does not always happen smoothly. When asked what challenges their organization faces when it comes to having developers take on more security responsibilities, 44% said “developers would be overburdened with security responsibilities or tools.” Forty-two percent said they did not feel developers are qualified to take over security duties, and 43% responded that “the whole process would make more work for the security team.”Walking the Line
Security is not meant to be a red light on the road to your business goals. It is meant to enable you to reach those goals safely and with minimal risk, and increasingly, organizations understand they need to integrate security into their development processes to do that. Organizations looking to walk the line should use solutions like, CrowdStrike Cloud Security, to integrate security early into the continuous integration/continuous delivery (CI/CD) pipeline in a way that is automated, frictionless, and empowers developers to deliver applications without decreasing speed.
And the Survey Says …
But just where are enterprises on this journey? In a new report, “Walking the Line: GitOps and Shift Left Security,” analyst firm Enterprise Strategy Group (ESG) found that the majority of app developers and IT and cybersecurity decision-makers recognize the need to bake security into the development process and their organizations are ready to spend money to do so. Yet technical and other challenges remain.

- Organizations recognize the need to incorporate security into the development process. Sixty-eight percent of respondents said adopting developer-focused security solutions and shifting some security responsibilities to developers was a high priority for their organization. Additionally, 69% said their organization plans “significant investments” in security solutions that can be integrated into their cloud-native software development processes.
- Most security teams are “mostly comfortable” or “completely comfortable” with developers taking responsibility for security testing. Still, when asked about challenges, some respondents expressed fears that developers would be overburdened.
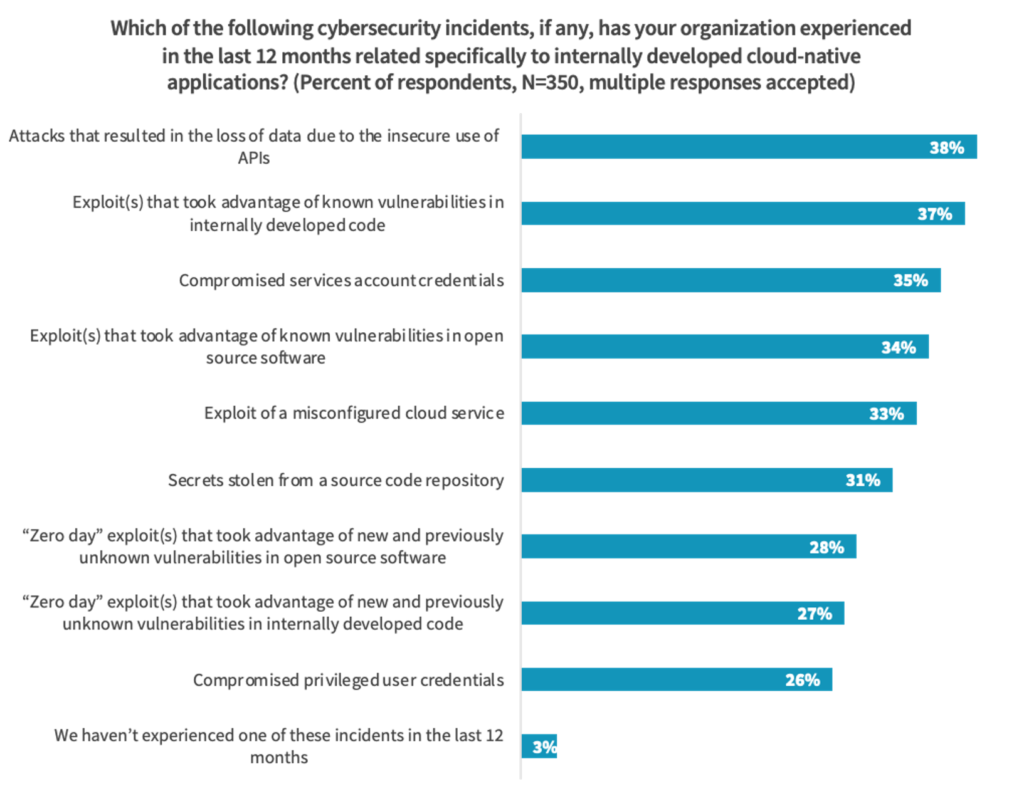
- The cloud-native cybersecurity threat landscape is getting riskier. Nearly every IT pro surveyed encountered incidents and related consequences in the past year. The most common issues were attacks leveraging the insecure use of APIs, exploits that took advantage of known vulnerabilities in internally developed code, and compromised service account credentials.
- Modern development practices increase speed but also security risks. As the use of infrastructure-as-code (IaC) has grown, security has become a significant issue. More than 80% reported an increase in IaC template misconfigurations. The impact of these misconfigurations ran the gamut from unauthorized access to applications and data to the introduction of crypto-jacking malware.
The Cybersecurity Threat Landscape Is Intensifying
The emphasis on integrating security into the development process could not have come at a more crucial time. Only 3% of respondents said they had not experienced one of the security incidents related to internally developed cloud-native applications and listed in the chart below in the past 12 months. At the same time, 38% said they had suffered an attack that resulted in data loss due to the insecure use of APIs.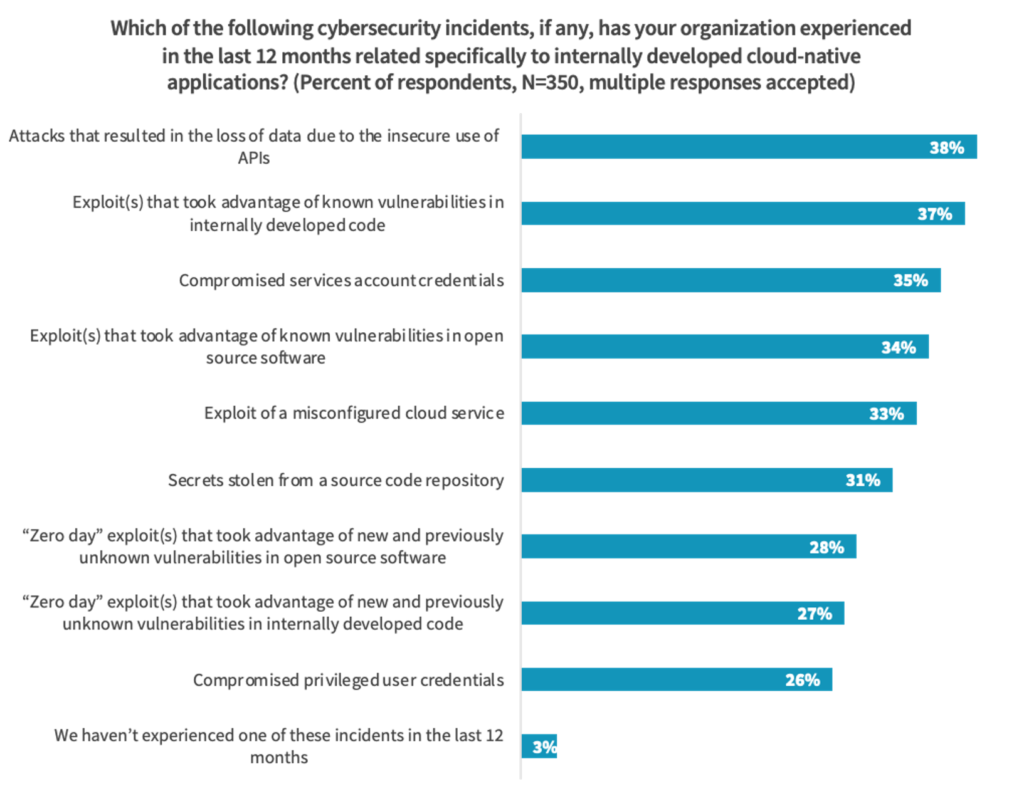 Source: “Walking the Line: GitOps and Shift Left Security,” Enterprise Strategy Group (ESG)
Source: “Walking the Line: GitOps and Shift Left Security,” Enterprise Strategy Group (ESG)The good news is that awareness of these challenges appears to be driving organizations to shift security left. During the next 12 to 18 months, 34% said improving application testing will be a top investment priority for their cloud-native application security plans. Thirty-one percent named applying runtime API security controls a top priority, and 31% said the same about detecting secrets that have been committed and stored in source code repositories.
The Impact of Shift Left Security
Shifting security left does not always happen smoothly. When asked what challenges their organization faces when it comes to having developers take on more security responsibilities, 44% said “developers would be overburdened with security responsibilities or tools.” Forty-two percent said they did not feel developers are qualified to take over security duties, and 43% responded that “the whole process would make more work for the security team.”
Some of those surveyed felt that developers are not always comfortable handling security due to friction: 46% said developers view security tasks as disruptive to development processes, and 44% said developers felt the security team should be doing the security work. This shows that in addition to facing some integration and technical challenges, organizations will have to overcome such workplace cultural issues if they are going to succeed in shifting left.
Walking the Line
Security is not meant to be a red light on the road to your business goals. It is meant to enable you to reach those goals safely and with minimal risk, and increasingly, organizations understand they need to integrate security into their development processes to do that. Organizations looking to walk the line should use solutions like, CrowdStrike Cloud Security, to integrate security early into the continuous integration/continuous delivery (CI/CD) pipeline in a way that is automated, frictionless, and empowers developers to deliver applications without decreasing speed.To learn more about the challenges organizations face with faster cloud-native development lifecycles and how developers and security teams work together, download the report here.
Additional Resources
- Learn more about today’s adversaries and how to combat them at Fal.Con 2022, the cybersecurity industry’s most anticipated annual event. Register now and meet us in Las Vegas, Sept. 19-21!
- To learn more about the cloud threat landscape, download “Protectors of the Cloud: Combating the Rise in Threats to Cloud Environments.”
- Learn how you can stop cloud breaches with CrowdStrike unified cloud security for multi-cloud and hybrid environments — all in one lightweight platform.
- Build, run and secure cloud-native applications with speed and confidence using Falcon Cloud Security
- Visit the Falcon Cloud Workload Protection Complete product webpage to see if a managed detection and response solution for cloud workloads is right for your organization.
- Request a demo: Falcon Cloud Security






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)










































