How to Leverage the CrowdStrike Store
Introduction
This document and video will provide an overview of the CrowdStrike store and demonstrate how it can add value for customers and prospects.
Video
Overview
The CrowdStrike Store is available as an app in the Falcon UI. It enables existing customers to discover, try, buy and deploy trusted partner applications and add-ons that extend their existing investment in the Falcon platform. By leveraging existing CrowdStrike agents and event telemetry, customers can address new challenges without wasting more time and resources to deploy additional agents. This approach also helps customers reduce security risk by leveraging applications that are pre-built, tested and certified by CrowdStrike.
What is in the CrowdStrike Store?
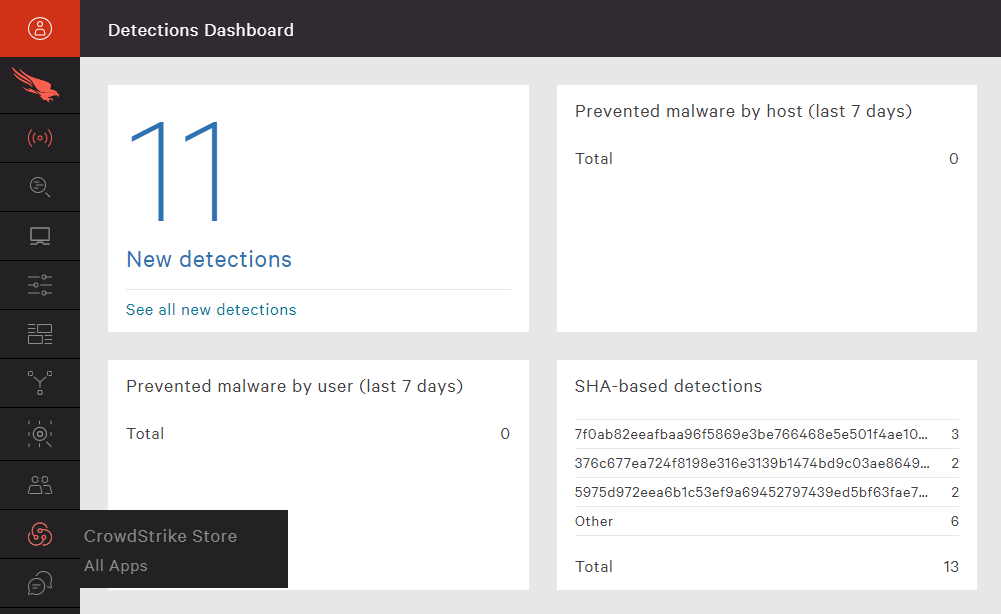
To access the store, find the store app in the menu on the left side of the CrowdStrike UI.
Once you are on the store, you will see three different types of offerings.
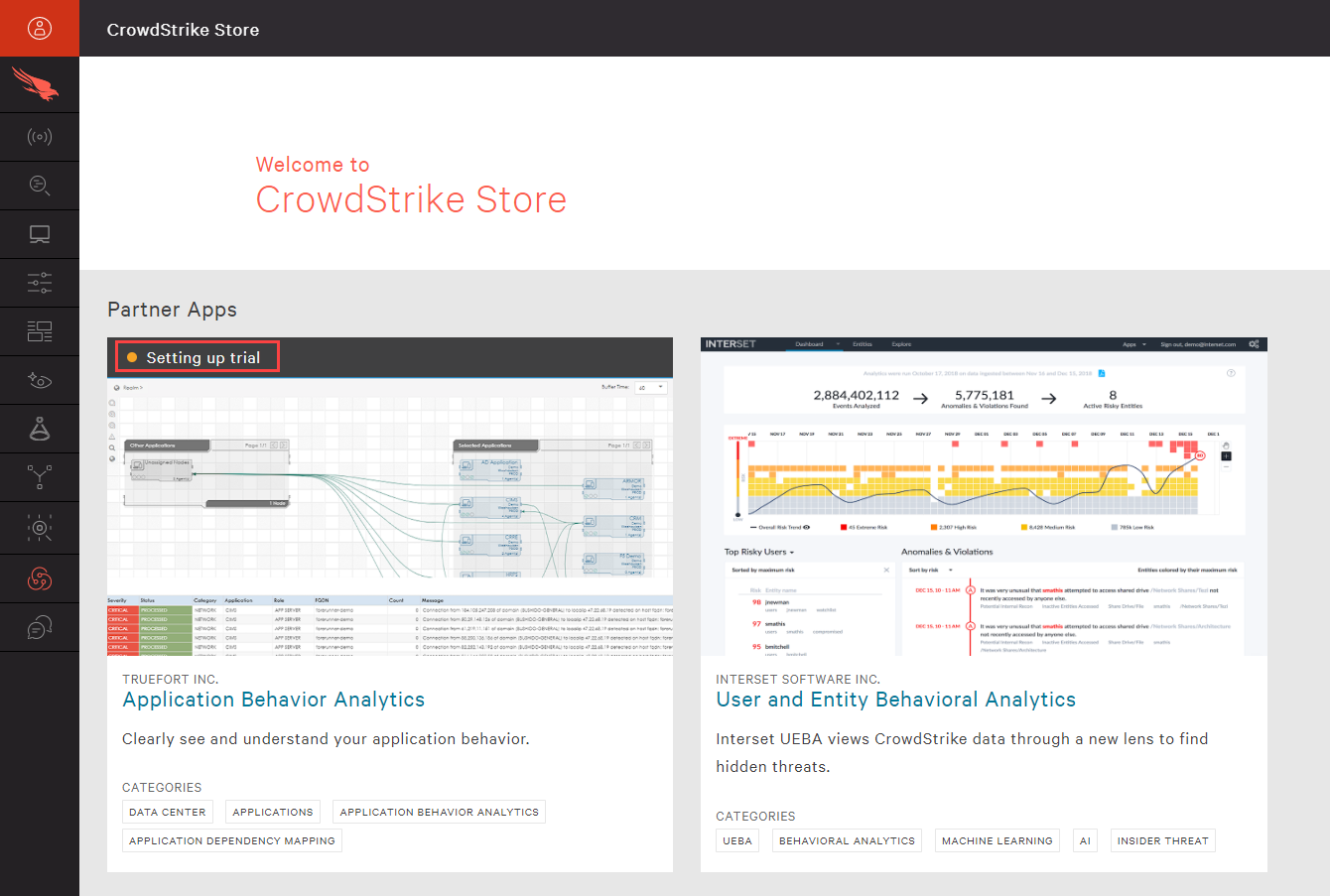
Highlighted partners – For these partners, the integrations are developed and ready to use. Leveraging the existing CrowdStrike event data, customers can quickly realize the value of these additional security solutions.
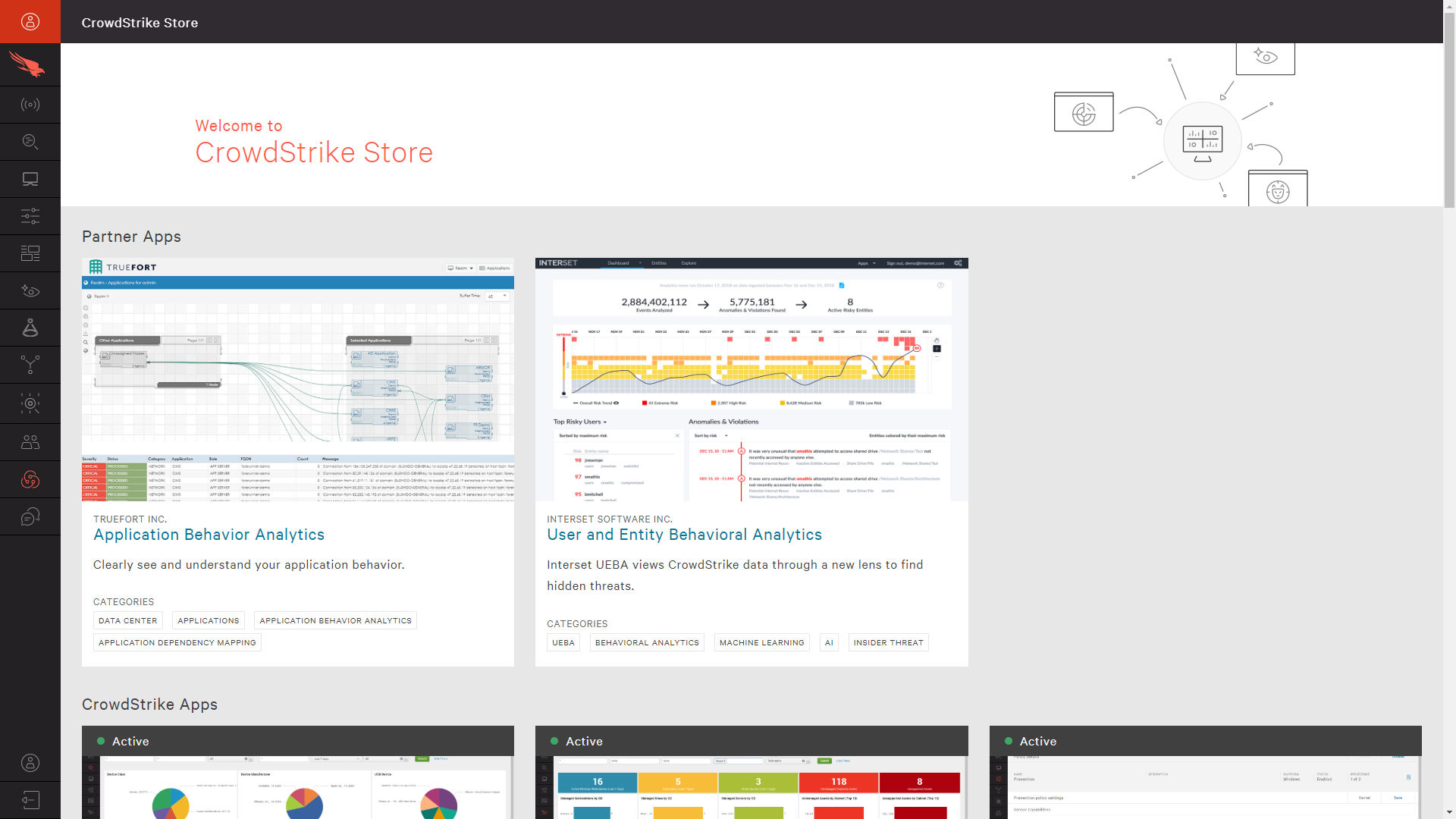
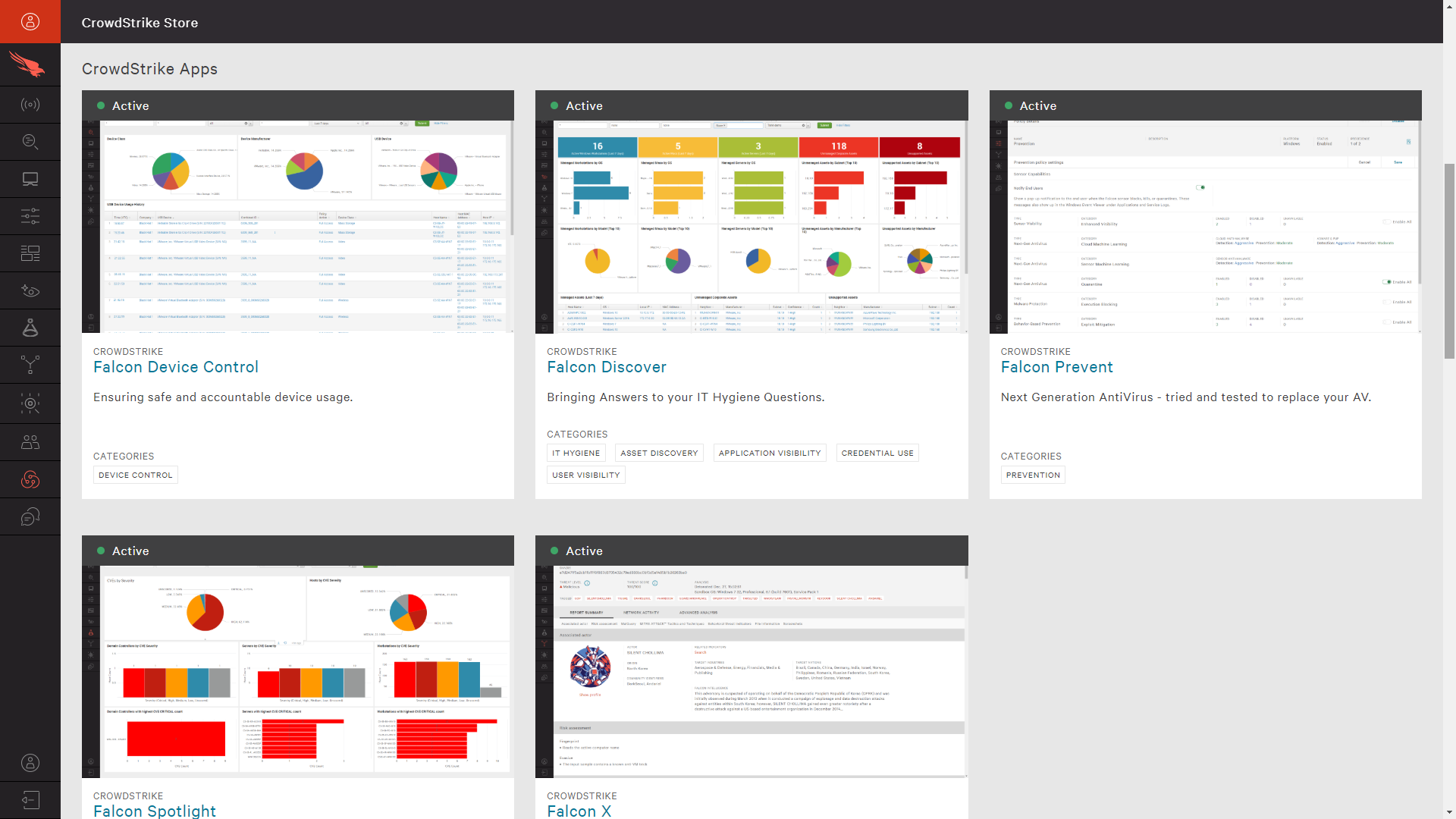
CrowdStrike apps – The store also provides access to research, understand and enable additional CrowdStrike provided apps. These apps can be found in the section just beneath the highlighted partners. Customers who are already entitled to a given app will see it labeled as “Active”, while additional applications will include an option to “Try It Now”.
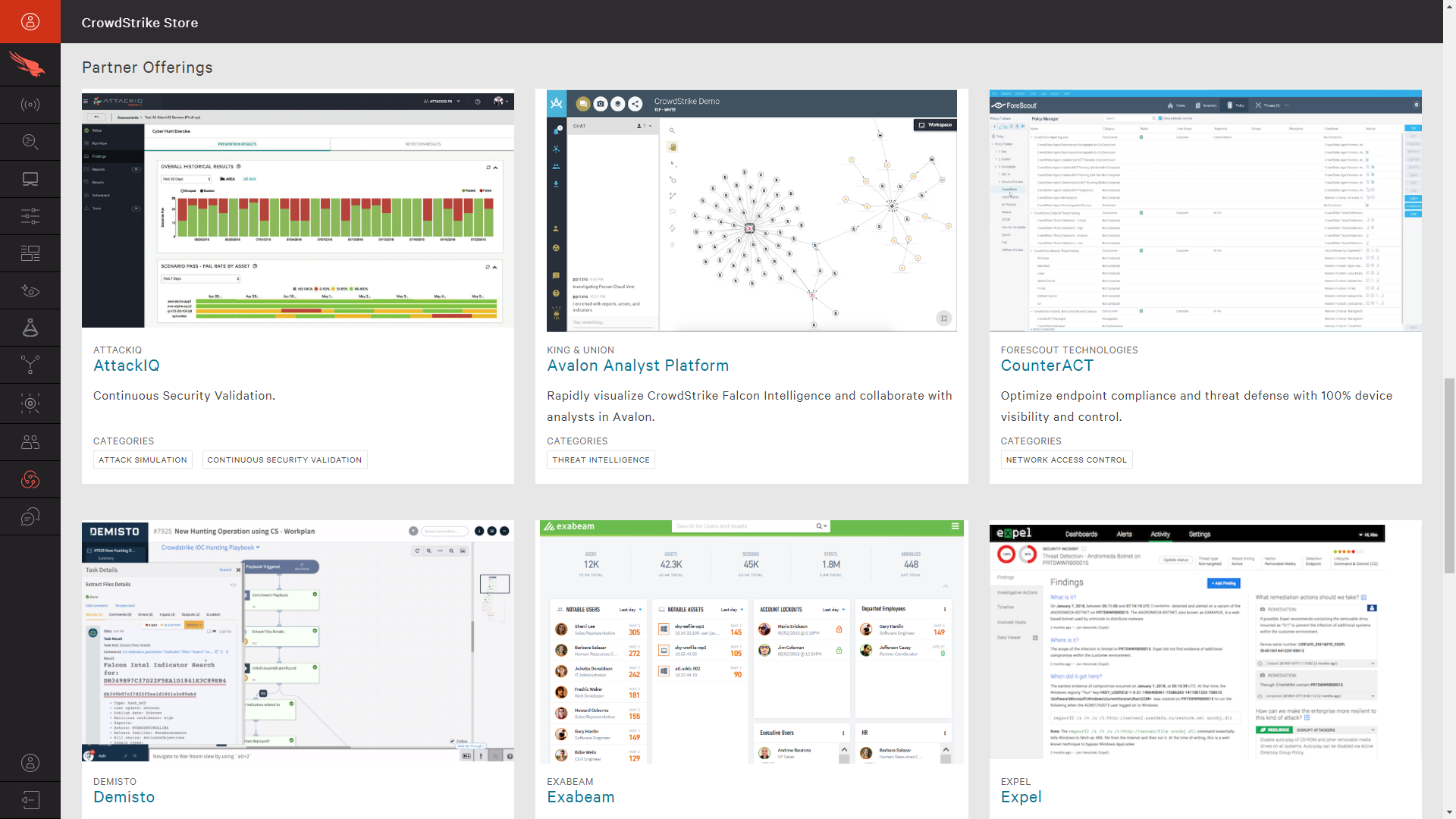
Partner offerings – Below the CrowdStrike apps, you will find another section of partner offerings. These solutions can also leverage the powerful Falcon API’s to maximize the value of the existing CrowdStrike agent and event data.
How do customers use the CrowdStrike Store?
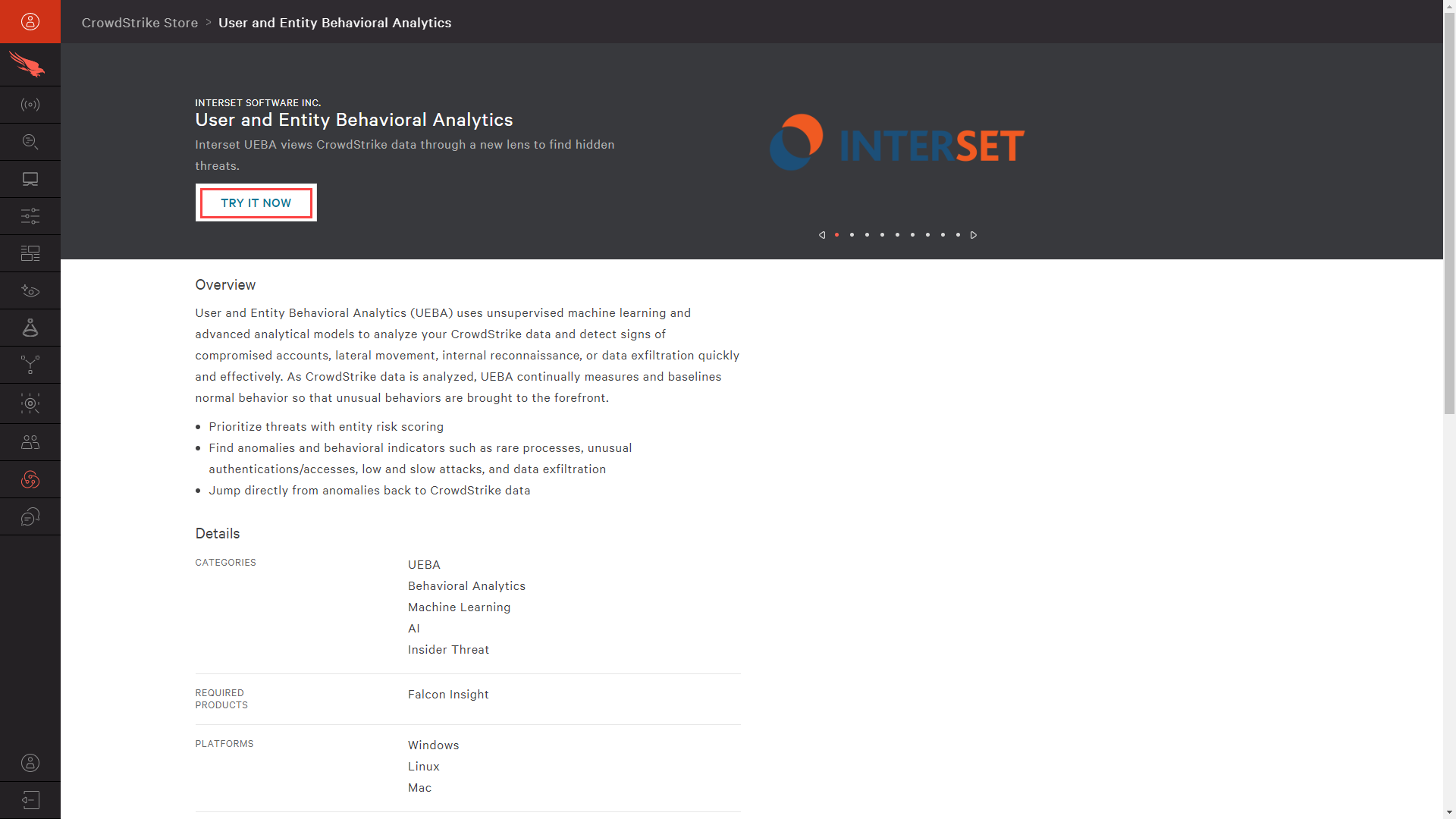
For each partner and application, the store provides an overview as well as details including category, supported platforms, a demonstration video and documentation. For the highlighted partners and CrowdStrike apps, you can chose to “Try It Now” directly from the store.
After reviewing the terms, you will receive an email regarding next steps. During the brief activation stage, the status in the store will be reflected accordingly as “Setting Up Trial”.
Once the activation is complete, the status of the app in the UI will change to “Active”.
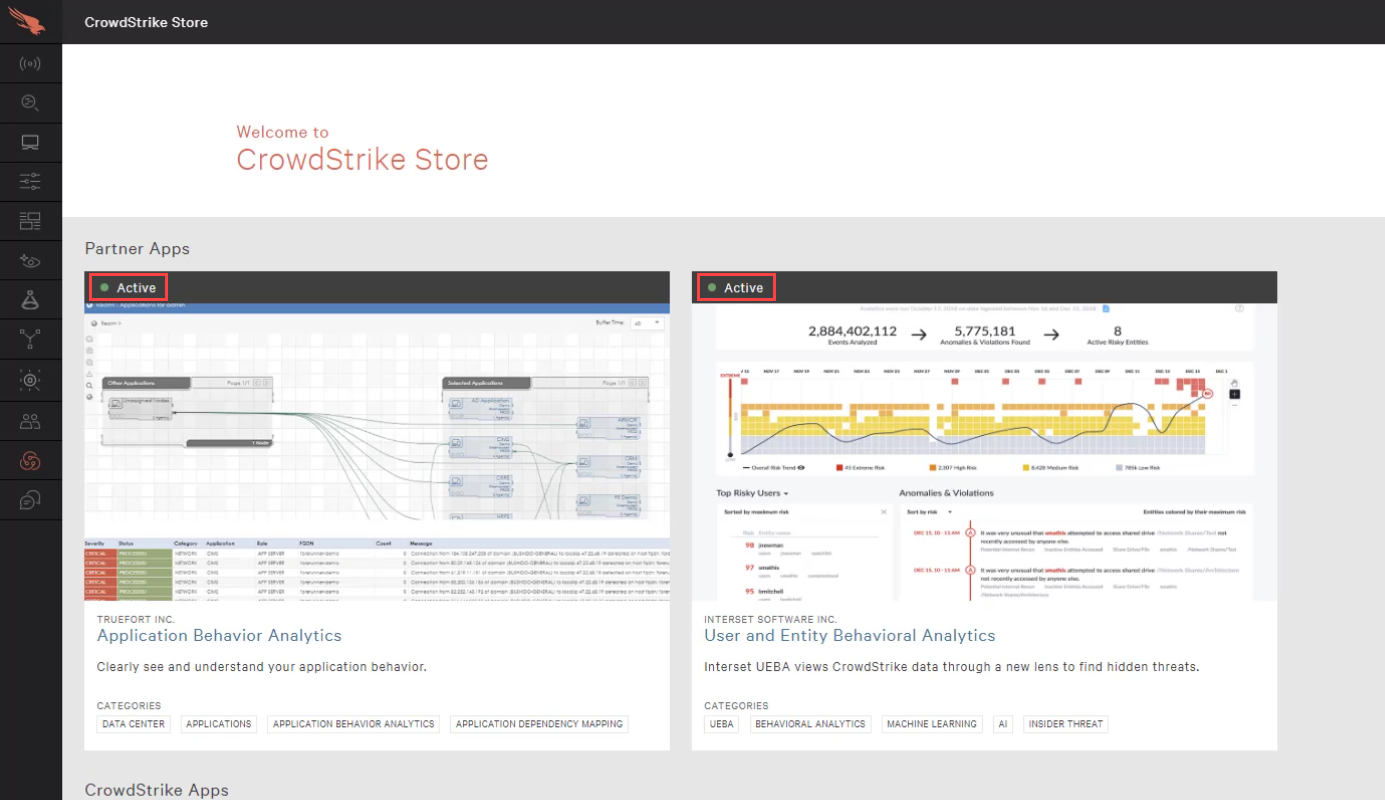
For partner integrations, you can then begin using the new application and understand how CrowdStrike’s event data quickly enables other security solutions to provide immediate time to value.
For CrowdStrike products, the new modules will be enabled and accessible in the same, easy to use, cloud delivered management UI. Trial customers will have access to full feature functionality across their entire population of managed systems.
Conclusion
The CrowdStrike Store is an ecosystem that lets you extend the capabilities of the Falcon platform with a host of ready-to-go partner apps and add-ons to solve security challenges. Through the Falcon UI, you have the ability to investigate and understand new integrations and CrowdStrike products with immediate access to request a trial, watch demonstrations and review documentation. Visit the CrowdStrike Store to try a new application today.
More resources
- CrowdStrike 15-Day Free Trial
- CrowdStrike Tech Center
- Sign up for a weekly Falcon demo
- Request a 1:1 Demo
- Guide to AV Replacement
- CrowdStrike Products
- White Paper on Falcon OverWatch