A Primer on Machine Learning in Endpoint Security
Although machine learning (ML) isn’t a new concept — it actually dates back to the origins of the computer itself…
What Causes IT Alert Fatigue and How to Avoid It
A recent survey by the Cloud Security Alliance found, among other things, that out of a sampling of 2,542 anomalous…
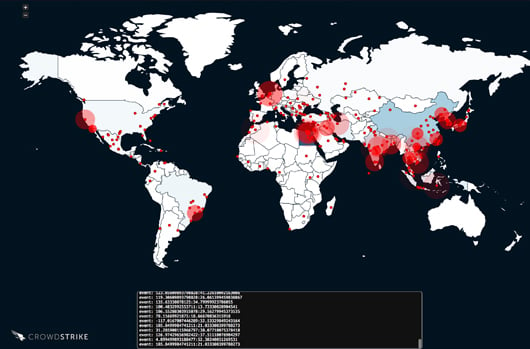
Inside the Takedown of ZOMBIE SPIDER and the Kelihos Botnet
This figure shows a snapshot of systems infected with Kelihos communicating with the sinkhole created to disable it. The arrest…
Securing the Mac-Based Organization
Though PCs still dominate the workplace, Macs continue to gain ground as the platform of choice for many organizations. As…
W-2 Phishing Scam Adds a New Twist to Wire Transfer Fraud
Organizations have long been aware of their vulnerability when it comes to email and yet phishing scams continue to be…
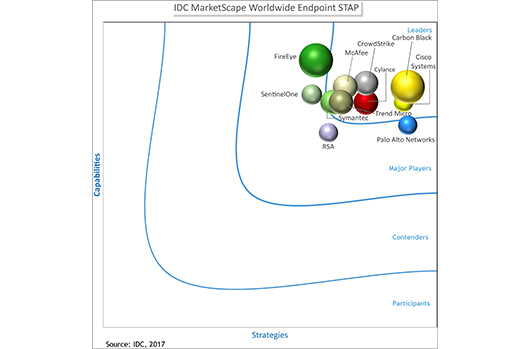
IDC MarketScape Names CrowdStrike Falcon® a “Leader” for Endpoint STAP
The IDC MarketScape vendor analysis model is designed to provide an overview of the competitive fitness of information and communications…
Understanding Indicators of Attack (IOAs): The Power of Event Stream Processing in CrowdStrike Falcon
Event Stream Processing (ESP) has been a central component of CrowdStrike Falcon’s IOA approach since CrowdStrike's inception. In this post…
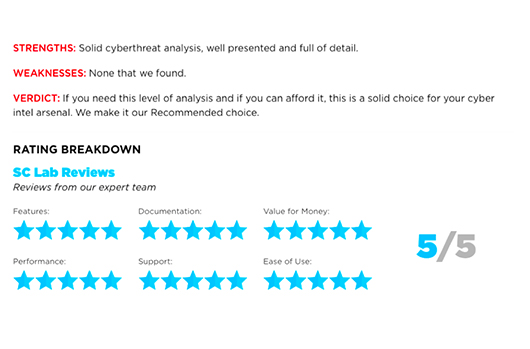
CrowdStrike Falcon Intelligence Receives SC Magazine Highest Recommendation and Rating
CrowdStrike Falcon™ Intelligence, powered by the CrowdStrike Global Intelligence Team, received top honors from SC Magazine with the highest possible rating…
The Economics of Ransomware: How SCADA/ICS Changes the Equation
Recent reports of SCADA/ICS proof-of-concept ransomware have spurred fresh discussion on the topic. Few threats exceed the level of concern…