Across the conference circuit and the general cybersecurity community this year, Zero Trust – a term originally coined in 2010 – has been perhaps the industry’s hottest buzzword. Move over, blockchain, and machine learning.
In a previous post, we outlined what Zero Trust Security means and what lessons the framework offers for the security community. We also discussed the challenges of implementing Zero Trust, including:
- hurdles around securing legacy applications/network resources and tools and protocols
- regulatory headwinds given that the framework can theoretically conflict with global legislation, including GDPR
- the looming reality that the typical large global enterprise lacks the organization-wide visibility and control necessary for implementation.
There are plenty of other reasons why most enterprises are far from achieving a true Zero Trust posture, despite increasing industry agreement of the necessity for this framework. In practice, implementing a Zero Trust model can mean re-architecting an organization’s entire network, a costly, often politicized move that requires C-suite (and even board) sign-off.
In this post, we'll outline a framework for a true Zero Trust model that adheres to industry best practices while specifically avoiding the potential for an over-engineered network overhaul, wasted IT budget, and potentially costly organizational disruption.
5 Steps to Building a Zero Trust Strategy
The path forward for a realistic Zero Trust model that doesn’t require a cost-prohibitive overhaul involves building a strategic understanding around – and enforcement capability for – every user’s identity, behavior, and risk profile, including visibility and control. This should encompass all IT environments: cloud, on-premise, and hybrid.
Here are five steps you can take to get closer to building a Zero Trust strategy that dramatically improves your organization’s security posture:
Step #1. Verify trust upon access to any network resource – and do it in real-time.
Include assets that are ignored today. Be sure to focus on legacy systems, tools, and protocols that traditionally are unprotected, do not rely on trust or risk and are commonly used and abused by adversaries (for example, PsExec is a favorite tool for malicious actors).
Step #2. Define trust, especially when it comes to devices.
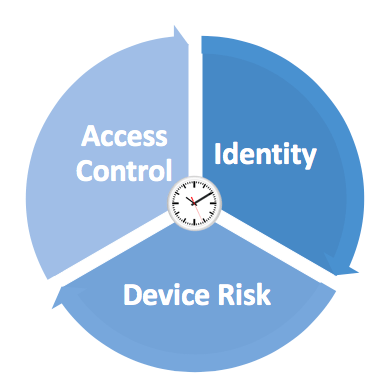
In your organization, what is trust? Theoretically, if we go by the concept at a network level, trust is based on identity, access levels, and device risk all wrapped up into a specific point in time, which can be the 4th dimension. But what if you don’t have a device management solution? Or if you’re not utilizing certificates? Does this mean that you need to work on these implementations first?
You can define device trust based on other features, which are tied to the device activity while measuring ownership relations between the authenticating user and the device. You can also utilize EDR data or even endpoint protection software. These can be used in a straightforward manner as compensating controls for the perceived traditional device risk.
Step #3. Personalize your security posture with a user-centric approach.
At the heart of the Zero Trust concept, there is an understanding of the shift in responsibility and the need to emphasize security at the end-user level. This means empowering end-users to take charge of the necessary actions required for accessing resources. End users are expected to be able to remediate their problems, such as enroll a device with MFA, install a certificate, patch their system to the required level to get access, choose which MFA vendor they want to work with, or other measures to meet the organization’s defined trust level.
Step #4. Collect use cases.
Explore and define the situations that the solution should address. Most users are OK with only internet access and perhaps VPN. Zero Trust is about managing situations, and a custom policy-based approach is the most realistic option. You must prioritize your use cases. For example, you should at the first vet the authentications to the domain, then review access to services and applications, followed by tools. Don’t limit the analysis to web applications just because it is easy to do with a web proxy. Make sure to vet every aspect of where authentication is involved, regardless of the application type.
Step #5. Gradually expand.
Ditching remote access VPNs immediately is not required. Even for Google, it took years to adopt and practice BeyondCorp, which can be considered one of the well-known implementations of the Zero Trust concept. Another example is Netflix Lisa, which is defined as a practical model of Zero Trust – and it doesn’t eliminate a VPN immediately. Once you have prioritized the defined use cases, it is time to build these situations into rules. With time, organizations can move from audit mode to active enforcement mode.
Expert Tip
By starting with this approach organizations can implement Zero Trust without blowing up the fundamentals of the current infrastructure. The overarching strategy is to comprehensively manage all situations all in one place, which both reduces cost and improves operational efficiency via a holistic view.
Traditionally, most Zero Trust implementations at major companies have tried to position a proxy in front of every point of access (such as a Proxy for Web Applications and Proxy for SSH, with on-premise proxies for other communications). All of these proxies are eventually connected to an authentication provider. Yet the ideal scenario of achieving Zero Trust is one without this complex patchwork of solutions and instead involves making the authentication provider smarter by adding an evaluation layer based on Identity, Behavior, and Risk. A centralized approach of this type not only eases the implementation but also addresses many more use cases that aren’t traditionally addressed by the current proxy approach.
How Identity & Access Threat Prevention Can Support Zero Trust
At this time, one-stop shopping for Zero Trust isn’t quite a reality or possibility for most organizations. In most cases, organizations are mostly focused on web applications but don’t know how to move forward from there or don’t have the right tools. To help organizations get closer to Zero Trust adoption to the places and situations in your network that they are struggling with, Identity and Access Threat Prevention (IATP) can be a key component that doesn’t require an organization to do surgery on their network.
With IATP, organizations can achieve unified visibility and proactive control across siloed solutions and platforms. IATP preempts threats before impact with adaptive and policy-based responses.
With an adaptive and personalized approach to end-users’ security experience based on identity, behavior, and risk. In particular, IATP solutions like CrowdStrike’s can support:
- Any application access control (Web services, Network tools, Legacy Apps, Domain Logon, Service access, Remote Desktop)
- Adaptive and situational management with policy rules
- Risk assessment and threat detection
- Verification of identity and access in real-time
- Comprehensive control that doesn’t unnecessarily burden employee workflows and productivity
An IATP approach can work seamlessly, regardless of users’ locations, devices, or workflows, all while significantly reducing an organization’s attack surface.
Conclusion
The Zero Trust model has strong merit, and we expect this philosophy to be increasingly adopted. Forward-looking organizations are increasingly looking to a Zero Trust posture that includes proactive capabilities to respond to suspicious activities in real-time, across any application, and in any network (e.g. not only web applications). CrowdStrike’s proactive threat prevention approach with IATP provides a comprehensive solution for organizations to adopt Zero Trust with a complete picture of Identity, Behavior, and Risk.

The Complete Guide to Building an Identity Protection Strategy
Take the first step toward a resilient identity security posture and download the Complete Guide to Building an Identity Protection Strategy to protect your organization’s digital identity landscape today.
Download Now




