Investment Banking Firm Greenhill Uses Falcon Complete to Protect Global Clients’ Data
Greenhill, an investment bank with global clients, estimates it has reduced alerts by 75% and saved $300,000 annually following deployment…
Cyber Insurance Is Not a Substitute for Cybersecurity
Ransomware is becoming increasingly pernicious — recently, the DarkSide attack disrupted a major U.S. fuel pipeline, and soon after another…
CrowdStrike and EY Join Forces to Boost Organizational Resiliency
The evolution of today’s remote workforces requires organizations to establish comprehensive and reliable cybersecurity strategies and operations to stay on…
The F1 “Pit Wall”: A Better Metaphor for Teamwork
In the split-second world of Formula One, what happens during a pit stop can make or break a race. Consider…
Response When Minutes Matter: When Good Tools Are Used for (R)Evil
This Falcon Complete incident response investigation recap was originally published by IT-daily.net on Apr. 13, 2021. It was late on…
Where Is the Cyber Insurance Market Going?
The ongoing ransomware outbreak has led to frequent and significant security incidents at organizations across the globe, such as the…
Corporate Sales Manager Olga Saburov on the Connection Between Sales and Service
For CrowdStrike employees, their role is much more than “just a job.” Whether they’re on our threat hunting team, a…
A Tale of Two RSA Conferences
Looking back at RSA 2020, it truly seems like it occurred in a different world. Thousands of us ranged the…
DarkSide Goes Dark: How CrowdStrike Falcon Customers Were Protected
The CrowdStrike Falcon® platform provides CrowdStrike clients with protection from DarkSide ransomware DarkSide is a ransomware as a service (RaaS)…
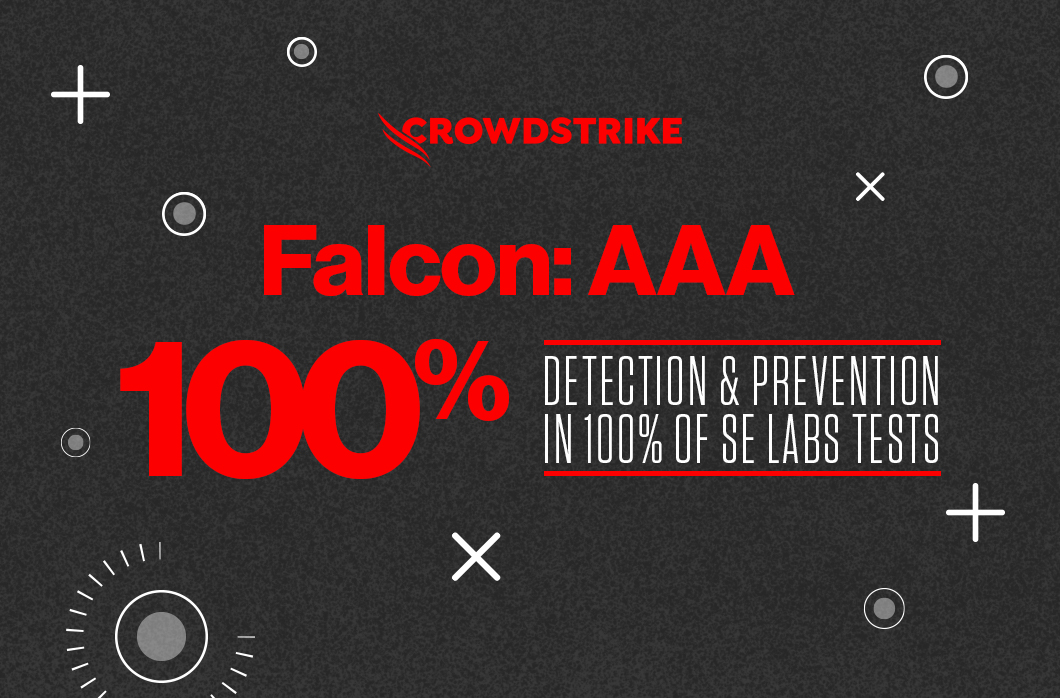
CrowdStrike Falcon Continues Impressive Record with Highest AAA Rating in SE Labs Enterprise Endpoint Protection Report
AAA rating In Q1 SE Labs Enterprise Endpoint Protection report 100% legitimate accuracy rating 100% protection against targeted attacks Track…