A Legal Perspective: Best Practices for Prevention and Immediate Response to a Breach
This blog originally appeared on Nov.20, 2019, as an article in LawyersWeekly.com.au, a site dedicated to independent news, analysis and…
CrowdStrike Webcast with Mercedes-AMG Petronas Motorsport Focuses on the Need for Speed in Cybersecurity
An on-demand webcast featuring CrowdStrike Sr. Engineer Zeki Turedi and Mercedes-AMG Petronas Head of IT Matt Harris details why speed,…
Who is REFINED KITTEN?
Common Aliases REFINED KITTEN may also be identified by the following pseudonyms: APT33 Elfin Magnallium Holmium REFINED KITTEN’s Origins REFINED…
CSO Australia on CrowdStrike Global Security Attitude Survey and What it Means for APAC Region
A recent article in CSO Australia titled, “Australian businesses slower to detect breaches than global peers, but everyone is still…
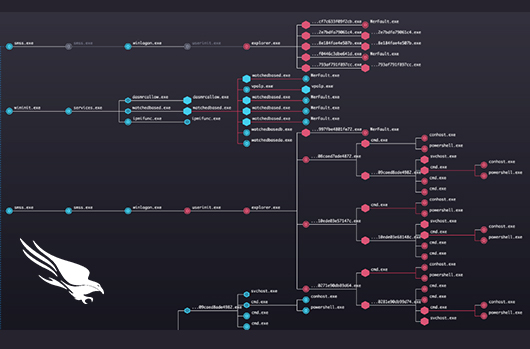
Organizations See Dramatic Reductions in Alert Fatigue With CrowdScore
Organizations face enormous challenges in prioritizing, understanding and responding quickly to a deluge of alerts triggered by a wide range…
CrowdStrike Debuts Product and Partnership News at AWS re:Invent 2019
CrowdStrike® is thrilled to be attending AWS re:Invent 2019 this week as an AWS Partner Network (APN) sponsor. Amazon Web…
Video Highlights the 4 Key Steps to Successful Incident Response
Given the current threat landscape, most organizations will likely encounter a cyber incident at some point, which will require them…
For the Second Year in a Row, CrowdStrike Has Highest Overall Rating Among Vendors Named a November 2019 Gartner Peer Insights Customer’s Choice
In the latest Customer’s Choice recognition for endpoint protection platforms (EPP), CrowdStrike has the highest overall rating among vendors named…
Outpacing the Adversary: Three Tips on How Mature Organizations Can Continuously Improve Cybersecurity
A new survey conducted by Lloyds Banking Group reveals that improving cybersecurity ranks as the top concern for banks, edging…
New CrowdStrike Report Reveals Organizations’ Attitudes Toward Cybersecurity Readiness
A new report from independent research firm Vanson Bourne titled The 2019 Global Security Attitude Survey studies how organizations assess…